Application Service Provider Agreement Between Verizon Sourcing LLC And SYNCHRONOSS TECHNOLOGIES, INC. GDSVF&H\3541367.2Application Service Provider Agreement Synchronoss and Verizon Proprietary and Confidential

Application Service Provider Agreement Between Verizon Sourcing LLC And SYNCHRONOSS TECHNOLOGIES, INC. GDSVF&H\3541367.2Application Service Provider Agreement Synchronoss and Verizon Proprietary and Confidential

TABLE OF CONTENTS APPLICATION SERVICE PROVIDER AGREEMENT ...................................................... 1 1. PARTIES ............................................................................................................. 1 2. TERM .................................................................................................................. 1 3. DEFINITIONS ...................................................................................................... 1 4. SCOPE/AUTHORIZATION LETTERS .................................................................. 7 5. LICENSES........................................................................................................... 9 6. OVERALL PERFORMANCE REQUIREMENT .................................................. 14 7. HOSTING .......................................................................................................... 15 8. DEVELOPMENT SERVICES............................................................................. 16 9. SECURITY ........................................................................................................ 17 10. ADDITIONAL REQUIREMENTS ....................................................................... 17 11. FEES/PAYMENT ............................................................................................... 18 12. RECORDS AND REPORTS .............................................................................. 20 13. DELIVERY......................................................................................................... 21 14. TESTING, EVALUATION AND APPROVAL ..................................................... 21 15. REPRESENTATIONS AND WARRANTIES ...................................................... 23 16. ESCROW .......................................................................................................... 27 17. TERMINATION .................................................................................................. 30 18. INFRINGEMENT ............................................................................................... 32 19. CONFIDENTIAL INFORMATION ...................................................................... 33 20. OWNERSHIP .................................................................................................... 34 21. SUBSCRIBER DATA AND CONTENT ............................................................. 36 22. USE OF TRADEMARKS ................................................................................... 38 23. PUBLICITY AND DISCLOSURE ........................................................................ 39 24. COMPLIANCE WITH LAWS .............................................................................. 40 GDSVF&H\3541367.2Application Service Provider Agreement Synchronoss and Verizon Proprietary and Confidential
25. FORCE MAJEURE ............................................................................................ 42 26. ASSIGNMENT ................................................................................................... 42 27. SUBCONTRACTING ......................................................................................... 43 28. TAXES ............................................................................................................... 44 29. PERMITS ........................................................................................................... 45 30. WORK RULES AND ACCESS REQUIREMENTS .............................................. 45 31. INDEMNIFICATION ........................................................................................... 49 32. INSURANCE ..................................................................................................... 50 33. RELATIONSHIP OF PARTIES .......................................................................... 51 34. NOTICES .......................................................................................................... 51 35. NONWAIVER .................................................................................................... 52 36. SEVERABILITY ................................................................................................ 52 37. LIMITATION OF LIABILITY .............................................................................. 53 38. DISPUTE RESOLUTION ................................................................................... 53 39. ORDER OF PRECEDENCE .............................................................................. 54 40. SECTION HEADINGS ....................................................................................... 54 41. SURVIVAL OF OBLIGATIONS ......................................................................... 54 42. CHOICE OF LAW AND JURISDICTION ........................................................... 55 43. GIFTS AND GRATUITIES AND CONFLICTS OF INTEREST ........................... 55 44. ENTIRE AGREEMENT ...................................................................................... 56 45. SIGNATURES ................................................................................................... 56 EXHIBIT A – FORM OF AUTHORIZATION LETTER ................................................... 57 EXHIBIT B – CHANGE REQUEST FORM .................................................................... 59 EXHIBIT C-1 - BASELINE INFORMATION SECURITY REQUIREMENTS .................. 61 EXHIBIT C-2 - VERIZON WIRELESS NETWORK SECURITY REQUIREMENTS…….80 EXHIBIT C-3 - CLOUD SECURITY REQUIREMENTS……………………………………87 GDSVF&H\3541367.2Application Service Provider Agreement Synchronoss and Verizon Proprietary and Confidential

EXHIBIT D - DISASTER RECOVERY PLAN ................................................................ 88 EXHIBIT E – COMPLIANCE WITH MINORITY, WOMAN-OWNED, AND SERVICE- DISABLED VETERAN BUSINESS ENTERPRISES (MWDVBE) UTILIZATION ........... 89 EXHIBIT F- NONDISCLOSURE AGREEMENT ............................................................ 94 EXHIBIT G .................................................................................................................... 97 SUMMARY OF VERIZON’S GUIDELINES ................................................................... 97 FOR EVALUATING CRIMINAL RECORD REPORTS .................................................. 97 GDSVF&H\3541367.2Application Service Provider Agreement Synchronoss and Verizon Proprietary and Confidential
APPLICATION SERVICE PROVIDER AGREEMENT 1. PARTIES This Application Service Provider Agreement is made between Synchronoss Technologies Inc. a Delaware corporation, with offices at ▇▇▇ ▇▇▇▇▇▇▇▇ ▇▇▇▇, ▇▇▇▇▇▇▇▇▇▇▇, ▇▇ ▇▇▇▇▇, on behalf of itself and for the benefits of its Affiliates (“Supplier"), and Verizon Sourcing LLC, a Delaware limited liability company, having an office and principal place of business at ▇▇▇ ▇▇▇▇▇▇▇ ▇▇▇, ▇▇▇▇▇▇▇ ▇▇▇▇▇, ▇▇▇ ▇▇▇▇▇▇ ▇▇▇▇▇, on behalf of itself and for the benefit of its Affiliates (individually or collectively “Verizon”), each a Party and together the Parties hereto. NOW THEREFORE, in consideration of the mutual promises and conditions set forth herein, receipt of which is hereby acknowledged, and intending to be legally bound, the Parties hereto agree as follows: 2. TERM This Agreement shall become effective when fully executed by both Parties hereto (the “Effective Date”), and the term of the Agreement shall retroactively commence on April 1, 2013 and shall continue in effect until five years from the Effective Date (the “Initial Term”). This Agreement shall be automatically renewed for subsequent one-year periods (each, a “Renewal Term” and together with the Initial Term, the “Term”) at the end of the Initial Term or any Renewal Term unless written notice of intent not to renew is given by one Party to the other **** prior to the end of the Initial Term or any Renewal Term. Notwithstanding anything herein to the contrary, the Term shall continue in effect so long as any Authorization Letters are outstanding. 3. DEFINITIONS The terms defined in this Section shall have the meanings set forth below whenever they appear in this Agreement, unless the context in which they are used clearly requires a different meaning or a different definition is described for a particular Section or provision: 3.1 “Acceptance” or “Accepted” means delivery to Supplier by Verizon of its written notice of acceptance or deemed acceptance as provided in Section 14 or any Authorization Letter. 3.2 “Affiliate” means, at any time, and with respect to any corporation, partnership, person or other entity, any other corporation, partnership, person or entity that at such time, directly or indirectly through one or more intermediaries, controls, or is controlled by, or is under common control with, such first corporation, partnership, person, or other entity. As used in this definition, “control” means the possession, directly or indirectly, of the power to direct or cause the direction of the management and policies of a corporation, partnership, person or other entity, whether through the ownership of voting securities, or by contract or otherwise. 1 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential ****CERTAIN INFORMATION HAS BEEN OMITTED AND FILED SEPARATELY WITH THE COMMISSION. CONFIDENTIAL TREATMENT HAS BEEN REQUESTED WITH RESPECT TO THE OMITTED PORTIONS

3.3 “Agreement” means this Application Service Provider Agreement, including all Orders, Statements of Work, Exhibits, attachments and all mutually agreed to Authorization Letters attached to and made a part of this Agreement. 3.4 “App(s)” means the software applications, including Catalog Apps, developed by Supplier for distribution to Subscribers for download, installation and use on such Subscriber’s Wireless Devices. 3.5 “App Store Catalog” means the third party online repository of applications to which Verizon or Supplier submits for publication an App subject to this Agreement. Examples of this include the online Qualcomm Brew Catalog, the Apple iTunes App Store, the Google Play Store, and the Amazon Kindle Fire Marketplace. 3.6 “App Store Owner” means the third party that owns or controls a given App Store Catalog. 3.7 “App Store Developer Agreement” means the agreement (typically a standard- form agreement) governing the submission, review and publication of applications, including any App, to an App Store Catalog, entered into between the developer of such application and the App Store Owner (or its designee), in addition to any policies incorporated into such App Store Developer Agreement. 3.8 “Application Service Provider” or “ASP” means a Person who manages and delivers content or application capabilities to enable Verizon to make such content or application capabilities available to its Subscribers. 3.9 “Authorization Letter” means a service agreement, order, statement of work or authorization letter, substantially in the form of Exhibit A, mutually agreed to between Verizon and Supplier and duly executed by an authorized representative of each party. 3.10 “Background Materials” means Supplier’s tangible and intangible materials and intellectual property that was developed independently from this Agreement or existed before Supplier commenced work on any Software, or Services provided under this Agreement or any Authorization Letter, including without limitation reports, documentation, drawings, computer programs (source code, object code and listings), inventions, know-how, creations, works, devices, masks, models and work-in-process, and any enhancements, corrections, Updates or modifications to such tangible and intangible materials and intellectual property provided it does not include Verizon Confidential Information and expressly excludes any Custom Software or Paid Work Product. 3.11 “Call Detail Information” shall be any information that pertains to the transmission of specific telephone calls, including: (a) for outbound calls, the number called and the time, location or duration of any call, and (b) for inbound calls, the number from which the call was placed and the time, location, or duration of any call. 2 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential

3.12 “Catalog App(s)” means any software applications developed by Supplier using a third party software development kit and tools developed by an App Store Owner and posted on the online App Store Catalog. 3.13 “Change Request” means a request to modify a previously agreed upon Authorization Letter, in the form attached to this Agreement as Exhibit B, sent in writing or via electronic transmission pursuant to the Change Request Process set forth in Section 4.3 of this Agreement and mutually agreed to by Verizon and Supplier. 3.14 “Commercial Service Date” means the first date that Verizon makes a Data Service commercially available to Subscribers under an Authorization Letter. 3.15 “Content” means digital media objects that Subscribers may preview, download, display, store or otherwise use via the Verizon Service. For greater certainty, Content may include audio, pictures, images, text, graphics, video or other media objects in formats described in the Specifications or as mutually agreed by the Parties, but shall not include any text or digital media objects originated by Subscribers. 3.16 “Content Provider” means any third party who has licensed Content to either Verizon or Supplier. 3.17 “CPNI” or “Customer Proprietary Network Information” shall be as defined in 47 U.S.C. Section 222(h)(1). 3.18 “Custom Software” means the system software, application software and other computer programs resulting from the Development Services provided by Supplier under this Agreement or an Authorization Letter that are not part of the Platform or Supplier Background Materials. Custom Software includes both object code and source code. 3.19 “Data Service” means a service made available by Verizon to Subscribers based upon the Platform, Services, and/or Software described in an applicable Authorization Letter including all exhibits attached thereto, as amended by any Change Request. 3.20 “Deliverables” means all Documentation and other materials, and all Upgrades thereto (i) are delivered to Verizon as described in an Authorization Letter or (ii) that Supplier agrees to provide to Verizon in providing Software or in performing the Services described in an Authorization Letter. For the avoidance of doubt, the Platform shall not be considered a Deliverable. 3.21 ”Development Services” means the design, creation, development, modification or enhancement of computer programs by Supplier pursuant to this Agreement or an Authorization Letter. 3.22 “Documentation” means all documentation containing requirements, technical and functional specifications, relating to the design, testing, training, operation and support of a Platform or Software whether in print or in electronic form, including without limitation, (i) Supplier’s then current specifications relating to 3 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential

Platform, Service or Software, (ii) user, maintenance and system administration documentation including without limitation user guidelines, operating manuals, training manuals and technical materials relating to Platform or Services; and (iii) any and all revisions to the above that Supplier provides or agrees to provide to Verizon in an Authorization Letter. 3.23 “Error” means failure of the Platform, Software or Services to perform in accordance with its Specifications. 3.24 “Hardware” means the hardware, equipment or facilities furnished by Supplier or used by Supplier to provide Hosted Services (including the Firmware licensed to Verizon when such Firmware is in the Hardware) and all additions, extensions, components, supplies, test equipment, apparatus and parts, as specified or identified in this Agreement or in an Authorization Letter, including, without limitation, those set forth or otherwise identified in any Authorization Letter, and all other Exhibits to this Agreement. 3.25 “Hosting Service” or “Hosted Service” shall mean the implementation and ongoing operation of a Platform connected to the Verizon Network by any means, including, without limitation, wide area data communications network connections to enable a Data Service to be provided to and used by Subscribers. 3.26 “Indirect Channel Entity” means any third party whom Verizon has authorized in writing to offer, promote, market and resell Verizon Services indirectly or through one or more tiers of indirect distribution, under the Trademarks of Verizon or the Trademarks of such Indirect Channel Entity. For greater certainty, the term “Indirect Channel Entity” expressly does not include overseas Affiliates of Verizon or its parent companies. 3.27 “Intellectual Property Rights” means any patent, copyright, rights in trademarks, trade secret rights and other intellectual property or proprietary rights arising under the laws of any jurisdiction. 3.28 “Milestones” means the schedule of development and delivery milestones specified in an Authorization Letter. 3.29 “Person” means any natural person, corporation, partnership, limited liability company or other entity. 3.30 “Platform” means the system comprised of computer equipment, Software and network interconnections and services, owned, implemented and operated by Supplier (and any corrections, Updates, enhancements or modifications thereto which enables Verizon to provide or support a Data Service to Subscribers as provided in an Authorization Letter. 3.31 “Products” means all Platform, Software and Services, and all hardware, equipment, supplies, materials, parts, components and assemblies used to provide the Services described in an Authorization Letter. 3.32 “Self-Help Code” means (i) any back door, “time bomb”, drop-dead device, or other software routine designed to disable a computer program automatically 4 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential

with the passage of time or under the positive control of a person other than a licensee of the program and (ii) any digital rights management or copy protection code for the Software other than as noted in the applicable Documentation. Self- Help Code does not include software routines in a computer program designed to permit the licensor of the computer program (or other person acting by authority of the licensor) to obtain access to a licensee’s computer system(s) (e.g., remote access via modem) for purposes of maintenance or technical support. 3.33 “Services” means all installation, implementation, technical support, maintenance, modification, training, repair, Development Services, Hosting Services, and other services related to a Data Service or Software that Supplier will provide to Verizon, as described in an applicable Authorization Letter including all exhibits attached thereto, as amended by any Change Request. 3.34 “Service Description” means the document attached to the applicable Authorization Letter and made a part thereof, that describes the Service or Software (as applicable) that Supplier will provide to Verizon, as may be modified by Change Requests agreed to by Supplier and Verizon pursuant to the Change Request Process. 3.35 “Verizon Service Requirements” means, collectively, all of the Specifications and all of the requirements for a Data Service or Software set forth or referenced in the applicable Authorization Letter, including but not limited to the Service Description, Service Level Agreement; Security Requirements (as set forth in Exhibit C and as supplemented or as modified in an applicable Authorization Letter); Training Plan and Disaster Recovery Requirements documents, as applicable and as amended from time to time by any mutually agreed upon Change Request, or otherwise upon mutual written agreement of the Parties. 3.36 “Service Level Agreement” or “SLA” means the document attached to the applicable Authorization Letter, which defines and sets forth the service level commitments to be performed by Supplier. 3.37 “Service Web Site” means the location on the Internet or other public data network accessed via a computing device at a URL specified by Verizon which will serve as a location and mechanism through which (i) information about a Data Service or Software may be provided by Verizon, (ii) a Person may elect to become a Subscriber or modify elections made for such Data Service or Software, or (iii) Content may be accessed by, transmitted to the Data Service by, or delivered to Subscribers. With respect to any Web Site maintained on the World Wide Web, such Web Site includes all HTML Pages (or similar unit of information presented in any relevant data protocol) that either are identified by the same second-level domain (such as ▇▇▇.▇▇▇▇▇▇▇▇▇▇▇▇▇▇▇.▇▇▇) or by an equivalent level identifier in any relevant address scheme. 3.38 “Software” means on whatever media provided, a program, or programs, including data files, system software and application software and firmware consisting of machine readable logical instructions and tables of information, which guide the functioning of a processor or which provide functional and operational performance capabilities and capacities, including all updates, 5 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential

upgrades and enhancements thereto. The term Software as used in this Agreement shall include Apps. 3.39 “Source Code” means the human-readable version of particular Software, as well as associated documentation required or necessary to enable an independent third party programmer with reasonable programming skills to compile, create, operate, maintain, modify and improve such Software and associated documentation without the help of any other Person. 3.40 “Specifications” means the written functional and technical specifications and requirements for a Platform or Software attached to or referenced in this Agreement or the applicable Authorization Letter and all Documentation, as amended from time to time by any mutually agreed upon Change Request or otherwise by mutual written agreement of the Parties. 3.41 “Subscriber” means a Person who (i) subscribes, in a manner prescribed by Verizon, to access and use a Data Service or Software from a Wireless Device and/or (ii) registers in a manner prescribed by Verizon, to access and use a Data Service or Software from a personal computer. For greater certainty, a Person may become a Subscriber either directly through Verizon or indirectly through an Indirect Channel Entity. 3.42 “Subscriber Data” means information or data that (i) is provided by Verizon or a Subscriber, or compiled, generated or collected by either Party in connection with a Data Service or Software, and (ii) identifies the Subscriber individually, or that when compared to or otherwise combined or processed with other information enables an individual Subscriber to be identified. For greater certainty, “Subscriber Data” includes, without limitation, user name or ID, account number, individual usage data, user profile or preferences, credit card or other payment information, mailing address, email address, IP address, landline or cellular telephone numbers, Social Security number and date of birth. 3.43 “Trademarks” means, with respect to each Party, their trademarks, service marks, trade names, logos, brands and other proprietary indicia. 3.44 “Unauthorized Code” means any virus, Trojan horse, worm, rootkit, or other software routine or hardware component designed to enable unauthorized access to, to disable, to erase, or otherwise to harm software, hardware, or data or to perform any other such actions. The term Unauthorized Code does not include Self-Help Code. 3.45 “Updates” means all future releases, patches, fixes, corrections, enhancements program code changes, improvements, upgrades, updates and new releases relating to Software, as well as refinements, solutions, changes and corrections to the Software as are required to keep the Software in conformance with the applicable Service Requirements and that are created by Supplier as corrections for defects in the Software, including without limitation error corrections, installation programs, and data conversion programs applicable to the Software. 3.46 “Usage Data” means information or data other than Subscriber Data (as defined above) that describes the operation of a Data Service for or use of a Data 6 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential
Service by Verizon, including but not limited to the number of Subscribers served, the volumes or types of Content stored, downloaded or used, the patterns or frequency of such use, use by geographic area or other similar analytical breakdown, financial information, network configurations, characteristics or capacity, performance metrics, test results, trouble reports and customer service information. 3.47 “Use” means (i) to read Software into or out of hardware memory; (ii) to access, use, execute, operate, display, perform, and store Software, in whole or in part, on any computer system, processor or mobile devices on which Software will function, and on any number of computer systems, processors, or mobile devices; (iii) to transfer into, and store in, equipment all or any portion of the Software; and (iv) to process and execute instructions, statements and data included in, or output to, the Software, all without any modifications to the Software. 3.48 “Verizon Content” means Content (as defined in Section 3.15) that is owned by Verizon or licensed to Verizon by third parties. 3.49 “Verizon Trademarks” means the Trademarks of Verizon that are used in a Data Service or Software or by Verizon in connection with Verizon Services. 3.50 “Verizon Services” means all voice and data communications services provided by Verizon, including, but not limited to, the wireless airtime and landline usage incidental to providing such services. 3.51 “Verizon Network” means the combination of interconnected, integrated telecommunications equipment owned, operated, licensed or leased by Verizon or its Affiliates, into which a Data Service will be integrated at one or more specified points as mutually agreed, that interoperates concurrently and as a whole for the purpose of transmitting, switching and receiving signals, containing voice messages and data, by any means, including electromagnetic (i.e., through the air) means. 3.52 “Supplier Content” means Content (as defined in Section 3.15) that is owned by Supplier or licensed to Supplier by third parties. 3.53 “Wireless Device” means any communications device that enables Subscribers to access and use a Data Service or Software. 4. SCOPE/AUTHORIZATION LETTERS 4.1 This Agreement does not by itself order any Service or Software. Verizon shall order Service or Software by submitting an Authorization Letter, substantially in the form attached hereto as Exhibit A, in accordance with the terms of this Agreement. 4.2 Authorization Letters 4.2.1 Supplier shall furnish Service or Software as specified in Authorization Letters issued from time to time by Verizon and accepted by Supplier. 7 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential
Verizon shall from time to time issue Authorization Letters in the form appended hereto as Exhibit A, setting forth in detail the specific tasks to be performed and the time frame in which they are to be performed. Authorization Letters for Development Services shall set forth a description of the services and the Custom Software or Paid Work Product ordered, if any, including Service Requirements, Milestones, pricing, and other relevant information, shall be signed by both parties, and shall be identified as an Authorization Letter issued pursuant to this Agreement. 4.2.2 Verizon shall appoint a Project Leader in each Authorization Letter issued by Verizon under this Agreement. 4.3 Change Requests 4.3.1 Verizon and Supplier may, at any time, agree to make additions, deletions or other modifications to a previously requested Service or Software through the Change Request Process set forth in Section 4.3.2 below. Such requests may include one or more documents appended thereto, all of which collectively shall comprise the requests. Change Requests shall be in the form appended hereto as Exhibit B. The parties acknowledge and agree that Change Requests shall not be used when the work requested will involve creation of new Custom Software or Paid Work Product, the ownership of which has not been previously agreed upon in an Authorization Letter. 4.3.2 Upon receipt of any proposed Change Request from Verizon, Supplier will provide to Verizon (i) a written a description of the work Supplier anticipates performing in order to effectuate requested change(s), (ii) a schedule for commencing and completing such work, and (iii) the costs to Verizon associated with such change(s) or services. If Verizon elects to have Supplier perform the changes requested, Verizon will have such Change Request signed by an authorized representative and Supplier shall then also have such Change Request signed by an authorized representative. A Change Request shall not be valid and neither Supplier nor Verizon will incur any liability thereunder until signed and approved by authorized representatives of both Parties (the “Change Request Process”). 4.3.3 Except as otherwise provided in a Change Request (or the underlying Authorization Letter), Verizon may cancel or reschedule Change Requests for convenience, in whole or in part, by providing at least **** written notice to Supplier. Supplier shall promptly curtail all activities in respect of such Services in the Change Request. Except as otherwise provided in the Change Request (or the underlying Authorization Letter), Verizon’s sole liability to Supplier under such cancelled Change Request will be the payment of all amounts due Supplier for work performed as supported by reasonable documentation through the effective date of cancellation. Where such work was to be paid on delivery of a Milestone or Deliverable, charges for such work shall be based on a time and materials basis calculated as number of hours 8 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential ****CERTAIN INFORMATION HAS BEEN OMITTED AND FILED SEPARATELY WITH THE COMMISSION. CONFIDENTIAL TREATMENT HAS BEEN REQUESTED WITH RESPECT TO THE OMITTED PORTIONS

worked at $**** (no hours prior to the execution of such Change Request shall be included) for any work in progress, capped at **** of the payment due for such work in the applicable Change Request (or the underlying Authorization Letter) for such Milestone or Deliverable, unless other termination fees or charges are specified under such Authorization Letter (in which case such stated termination fees or charges shall be in lieu of any other partial payments). 4.4 Affiliates An Affiliate that issues an Authorization Letter may enforce the terms and conditions of this Agreement with respect to any Software or Services purchased by such Affiliate as though it were a direct signatory to the Agreement. Default by one Affiliate shall not affect any other Affiliate party to this Agreement. 5. LICENSES 5.1.1 Supplier grants to Verizon and its Affiliates and to its and their employees, agents and contractors, a non-exclusive, irrevocable (other than for Verizon’s uncured material breach), worldwide, license and right to Use and access the Platform, Services and, to the extent Software is provided to Verizon, an unlimited number of copies of any Software and any Documentation related thereto required for Use and access to the Platform as specified in an Authorization Letter during the Term, at the prices set forth in the applicable Authorization Letter. Where expressly permitted by an Authorization Letter, Software may be sublicensed by Verizon to its original equipment manufacturers (“OEMs”), customers and Indirect Channel Entities in accordance with the foregoing sentence. 5.1.2 Verizon shall also have the right, at no additional charge, to Use the Software by means of remote electronic access at locations other than the locations at which the Software is stored. Supplier also grants to Verizon the right to authorize Use of such license to its subcontractors, agents, contractors, outsourcing entities and others for use when performing services for Verizon; provided that Verizon shall remain responsible to any violation of the Agreement or any Authorization Letter by such parties. In addition, if Verizon transfers or assigns the Software to an Affiliate or a third party in connection with the provision or support of network services, then the license granted hereunder shall extend to such transferee or assignee. No such authorization, transfer or sublicense shall release Verizon from its obligations hereunder. 5.2 License Term Except as otherwise set forth herein, the term of each license of Software granted under this Agreement or any Authorization Letter shall commence on the applicable delivery date, or such other date as set forth in an Authorization Letter, and shall remain in effect perpetually, or for such shorter term as set forth in an Authorization Letter, or until the Use of the Software, as it may have been updated or enhanced is permanently discontinued by Verizon, unless such license for Software is terminated in accordance with Section 17. 9 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential ****CERTAIN INFORMATION HAS BEEN OMITTED AND FILED SEPARATELY WITH THE COMMISSION. CONFIDENTIAL TREATMENT HAS BEEN REQUESTED WITH RESPECT TO THE OMITTED PORTIONS

5.3 Shrink-Wrap Licenses Under no circumstances shall any Supplier shrink-wrap or click-wrap license be given any force or effect in connection with any Software and Verizon specifically rejects all such licenses. The Parties agree to replace the terms of such licenses with the terms of this Agreement or an Authorization Letter, if applicable. 5.4 Content Licenses 5.4.1 Verizon grants to Supplier a limited, nonexclusive, non-transferable, royalty-free license to Verizon Content to copy, store, display, transmit, distribute and sell Content solely for the purpose of providing Verizon Content via its Platform for Verizon’s Data Service to Subscribers in accordance with the applicable Authorization Letter, expressly without the right of further sublicense of any of the foregoing. Nothing in this Section shall be interpreted as granting Supplier any greater rights or authorizations than are granted to Verizon pursuant to its licensing agreements with Content Providers. Supplier shall have no right to reproduce or sub-license, re-sell or otherwise distribute all or any portion of Verizon Content to any person in any form or any manner other than as necessary or appropriate in providing a Service or Software in accordance with the applicable Service Requirements. Except as otherwise agreed in writing, Supplier shall not receive, transmit, alter, copy, access, store, or otherwise use Verizon Content except for purposes of performing its obligations under an applicable Authorization Letter. Supplier shall protect all Verizon Content from unauthorized alteration, copying, access, storage, transmittal or use as required in this Agreement and as provided in the Service Requirements. 5.4.2 Supplier grants to Verizon a limited, nonexclusive, non-transferable license to Supplier Content to copy, store, display, transmit, distribute and sell Supplier Content solely for the purpose of providing Supplier Content through the Platform via a Data Service to Subscribers in accordance with an applicable Authorization Letter, expressly without the right of further sublicense of any of the foregoing. Nothing in this Section shall be interpreted as granting Verizon any greater rights or authorizations than are granted to Supplier pursuant to its licensing agreements with Content Providers. Verizon shall have no right to reproduce or sub-license, re-sell or otherwise distribute all or any portion of Supplier Content to any person in any form or any manner other than as necessary or appropriate in providing a Data Service in accordance with the applicable Service Requirements. 5.5 All rights and licenses granted under or pursuant to this Agreement or any Authorization Letter by Supplier to Verizon are, and shall otherwise be deemed to be, for the purposes of Section 365(n) of the United States Bankruptcy Code (“Code”), licenses to rights to “intellectual property” as defined in the Code. The Parties agree that Verizon, as licensee of such rights under this Agreement, shall retain and may fully exercise all of its rights and elections under the Code. The Parties further agree that, in the event of a bankruptcy proceeding by or against Supplier under the Code, Verizon shall be entitled to retain all of its rights 10 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential
(including all licenses) under this Agreement and/or any Authorization Letter. In the event of filing a petition for relief under the Code, Supplier shall assume or reject the Agreement within ****. 5.6 Catalog Apps 5.6.1 Additional License Terms 5.6.1.1 Supplier hereby grants to Verizon and its Affiliates and to its and their employees, agents and contractors, a non-exclusive license to: (i) copy, reproduce, display, submit for approval and perform all Apps on the applicable App Store Catalog, in object code format only; and (ii) exploit, use, distribute, transmit, and sublicense for download an unlimited number of copies of all such Apps to Subscribers, in object code format only, such that Subscribers may access and use the corresponding Data Service in accordance with the Agreement or an Authorization Letter. 5.6.1.2 With respect to each Apps submitted to the applicable App Store Catalog, the foregoing license shall commence on the date the App is submitted to the applicable App Store Catalog and will terminate on the earlier of (a) the date the App is removed from the applicable App Store Catalog, or (b) the date of termination of the applicable Authorization Letter. No such removal or termination will terminate a Subscriber’s rights or licenses to continue to use those Apps that were downloaded by the Subscriber prior to such removal or termination. All rights not granted in this Agreement are hereby reserved by Supplier. 5.6.2 Developer 5.6.2.1 For each App, Supplier agrees and Verizon acknowledges that, unless otherwise required by the applicable App Store Owner or agreed between the Parties, for all purposes in connection with the submission of Apps to the applicable App Store Catalog, Supplier shall be the developer of the Apps and shall be bound by, and shall comply with, all applicable terms of the applicable App Store Developer Agreement (and any related submission policies made known to Supplier by the App Store Owner). 5.6.2.2 Removal by Supplier Notwithstanding anything to the contrary contained in the App Store Developer Agreement, which may provide Supplier the ability to request the removal of any Apps from the App Store Catalog ,Supplier shall not, without Verizon’s prior written consent, request that Apps be removed from the App Store Catalog. Upon such consent and removal, Supplier acknowledges and agrees that such removal will terminate the applicable Authorization Letter with respect to such App, and that the removal of any Catalog App from the App Store Catalog will not terminate a Subscriber’s rights or licenses to continue to use such App if the App was downloaded by the Subscriber prior to removal. The foregoing shall not limit the ability of Supplier to replace or update an App for a given Wireless Device (eg: provide an update App to correct an Error). 11 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential ****CERTAIN INFORMATION HAS BEEN OMITTED AND FILED SEPARATELY WITH THE COMMISSION. CONFIDENTIAL TREATMENT HAS BEEN REQUESTED WITH RESPECT TO THE OMITTED PORTIONS

5.6.2.3 Removal by Verizon. Verizon may at any time, at its sole discretion and for any reason, remove any App that is exclusively used for Verizon and provided under this Agreement from an App Store catalog and upon doing so will provide notice to Supplier. The removal of any App from the App Store Catalog will not terminate a Subscriber’s rights or licenses to continue to use such App if the App was downloaded by the Subscriber prior to removal. 5.6.2.4 Direct Pay. Except as expressly set forth in an Authorization Letter, the parties agree that all payments to Supplier for the download and/or use of Supplier’s Apps shall come directly from Verizon and Supplier shall not be paid by an App Store Owner for any Apps downloaded from the App Store Catalog by Subscribers. The fees payable by Verizon to Supplier as set forth herein shall be in lieu of any and all amounts that would otherwise have been payable to Supplier by Qualcomm or Verizon under the Qualcomm App Store Developer Agreement. 5.6.2.5 Qualcomm - Establishing the DAP. For each Apps that Supplier makes available on the Qualcomm App Store Catalog, Supplier must submit a pricing template(s), indicating the agreed upon Developer Application Price (DAP) for such Catalog App in accordance with the BREW Developer Agreement (the App Store Developer Agreement applicable to Qualcomm BREW applications). Supplier and Verizon may choose from time to time to discuss and negotiate a DAP for one or more such Qualcomm BREW Catalog Apps. If Supplier and Verizon negotiate a DAP for one or more such Qualcomm BREW Catalog Apps, Supplier must still submit a pricing template(s) for the Qualcomm BREW Catalog App(s) in accordance with the BREW Developer Agreement. 5.7 Limited License to Supplier APIs 5.7.1 (a) In addition to the license rights to the Software granted to Verizon hereunder, Supplier hereby grants to Verizon, subject to the terms and conditions of this Agreement, including payment of the fees as set forth therein or in an applicable SOW, if any, a perpetual, non-exclusive, limited right to use and sublicense Supplier’s Solution API (as defined below) to those manufacturers of devices supported by the Solution and developers of software applications that reside and operate on devices supported by the associated Supplier Platform (each, a “Device Application Developer”) solely to enable the App to interface and interoperate with the associated Supplier Platform and access and use the functionality of such Supplier Platform licensed from Supplier by Verizon solely for the benefit of Verizon’s Subscribers. Such right includes the right for Device Application Developers to incorporate the Solution API into an interface of the Device Application and to support and maintain such interface subject to the limitations above. 12 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential ****CERTAIN INFORMATION HAS BEEN OMITTED AND FILED SEPARATELY WITH THE COMMISSION. CONFIDENTIAL TREATMENT HAS BEEN REQUESTED WITH RESPECT TO THE OMITTED PORTIONS

(b) In addition, upon termination of this Agreement or the applicable Authorization Letter (other than for cause by Supplier), provided that such termination is not due to Verizon’s breach of this Agreement, and Verizon has paid all fees due, including termination charges due, such license to the Solution API shall be extended to grant to Verizon the right to use and sublicense the Solution API to Device Application Developers solely to incorporate the Solution API into an interface of the Device Applications and support and maintain such interface with any service offering similar functionality to the associated Supplier Platform (and not solely to interface with the associated Supplier Platform) solely for the benefit of Verizon’s Subscribers (including those Subscribers using the service offering similar functionality to the associated Supplier Platform referenced in this sentence). In all cases, Verizon shall inform Supplier in writing of any Device Application Developer to which Verizon Wireless has provided the Solution API. Verizon shall be liable for any breach by a Device Application Developer of any of the covenants and obligations of Verizon hereunder. 5.7.2 During the Term or Renewal Term, Verizon may provide written notice to Supplier that it wishes to use and sublicense the Solution API set forth in subsection 5.7.1 to Device Application Developers to incorporate the Solution API into an interface of the Device Applications and support and maintain such interface with any service offering similar functionality to the associated Supplier Platform (and not solely to interface with the Supplier Platform) solely for the benefit of Verizon Subscribers because (A) Supplier has been subject to credits for failure to meet any one service level set forth in an applicable Service Level Agreement for three (3) consecutive months where each such failure is subjected to a credit of at least $**** or (B) Supplier’s Platform (or non-Platform Software supporting a Data Service) is not within Industry-Standards (solely from a technology basis including without limitation features and functionality) in some or all material respects and there is another service offering which Verizon wishes to use and that Verizon in good faith determines such service offering to address the “Industry Standards” issues identified in the affected Platform (or non-Platform Software supporting a Data Service). If such notice is pursuant to subsection (B) and Supplier fails to meet such “Industry Standards” in all material respects within a reasonable period after the receipt of such notice but no later than the production release date of the next feature release of the Platform (or non-Platform Software supporting a Data Service) that will reasonably accommodate any industry standard issues that may arise or which the content of such feature release has not yet been finalized, then such license shall be so extended as set forth herein. For the avoidance of doubt, in the event of the extension of the license to the Solution API as described above, this shall not release Verizon of any of its other obligations under this Agreement, including but not limited any payment obligations and Supplier has the right to immediately rescind such license in the event of any uncured material breach by Verizon under this Agreement. In the event that Verizon does not give notice of its exercise of the right hereunder to Supplier within **** of the trigger of such 13 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential ****CERTAIN INFORMATION HAS BEEN OMITTED AND FILED SEPARATELY WITH THE COMMISSION. CONFIDENTIAL TREATMENT HAS BEEN REQUESTED WITH RESPECT TO THE OMITTED PORTIONS
right, Verizon shall have been deemed to waive such right with respect to such triggering event. 5.7.3 Verizon shall enter into an agreement with each Device Application Developer whereby such Device Application Developer (i) agrees to keep the Solution API and any Supplier information confidential, and (ii) disclaims all liability of Supplier with respect to the Solution API. 5.7.4 Supplier shall have no obligation to provide any maintenance or technical or product support to any Device Application Developer in the event of Section 5.7.1(b) or 5.7.2 above. Any such support provided to Verizon on behalf of a Device Application Developer or to any Device Application Developer shall be subject to additional professional service charges from Supplier as agreed upon in a Change Order. Neither Verizon nor any Device Application Developer shall have any ownership right to the Solution API. 5.7.5 Definitions. As used herein: 5.7.5.1 “Solution API” means the application programming interfaces ("API") to the Supplier Software or Platform and related documentation. 5.7.5.2 “Device Application” means a Verizon or Device Application Developer product or software application intended for installation and use on a device (such as tablet or smart phone) that incorporates the Solution API therein, which is designed for, and usable, in strict accordance within the terms of this Agreement. The Device Application is distributed to the Subscriber of the applicable device. 6. OVERALL PERFORMANCE REQUIREMENT Supplier represents, warrants and agrees that it has the responsibility, duty and obligation to provide, perform, and deliver, to the extent set forth herein, the Services and/or Software described in any Authorization Letter(s) pursuant to this Agreement and Supplier further agrees and acknowledges: 6.1 that it recognizes that the Software and Services which are to be provided under this Agreement must be delivered in compliance with the scheduled dates and requirements set forth in the Authorization Letter(s) and perform in compliance with the Specifications; and 6.2 that Supplier has and will maintain an organization staffed by qualified personnel, including “key personnel,” with the knowledge, skill and resources to perform and complete the work and that there are and will be no commitments, legal, contractual or otherwise that are in conflict with Supplier’s obligations under this Agreement and applicable Authorization Letter. 14 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential

7. HOSTING 7.1 Upon acceptance of an Authorization Letter which includes Hosting Services, Supplier shall provide, install, maintain and support a Platform, including all necessary hardware, software, and services for the deployment, integration (to the extent indicated in an Authorization Letter), maintenance and management of the Platform or Software as described in the applicable Authorization Letter and shall provide such Hosting Service to Verizon in compliance with the Security Requirements set forth in Exhibit C hereto (as may be modified or supplemented in an Authorization Letter) and the applicable Authorization Letter, including all attachments thereto. 7.2 In the event Verizon elects to terminate the Hosting Service only (such date of termination, the “Hosting Termination Date”), and either internally provide and operate through its own equipment and facilities, or provide and operate through the equipment and facilities of its third party vendor, all or any part of such Hosting Service. In the event Verizon elects to terminate the Hosting Services as described above (or the Agreement or applicable SOW terminates or expires for any reason) and subject to payment by Verizon of any applicable fees for early termination of Hosting Services as set forth in an Authorization Letter: 7.2.1 Supplier shall provide Verizon, or its third party vendor, reasonable assistance in completing the transition to the internal operation of the Hosting Services by Verizon; and 7.2.2 Supplier or its successors in interest shall furnish to Verizon or its designee that is not a competitor of Supplier, the following documentation and information related to Hosting Services: (1) documentation regarding system, database and storage administration; (2) features and technical specifications for the hosting environment; (3) detailed equipment and software configurations for servers, storage, communications and other systems supporting the Hosting Services; (4) installation and testing procedures; (5) operations and provisioning procedures; (6) maintenance procedures and diagnostics; and (7) such other documentation the parties agree is reasonably necessary to support the Hosting Services. Verizon or its designee shall use such information and documentation solely to the extent necessary to support the Hosting Services. Such information and documentation shall be provided pursuant to a mutually agreeable statement of work, which shall set forth the specific tasks to be undertaken by Supplier in connection with such transition, the fees to be paid by Verizon therefor, and the time period for completing such transition; and 7.2.3 Verizon shall have the option, to purchase from Supplier such equipment elements used by Supplier to provide the Hosting Service, to the extent they are (i) owned by Supplier and no third party limitation or restriction prohibits such purchase, (ii) dedicated to the Hosting Services and not shared or used by any other customer of Supplier and (iii) reasonably necessary or appropriate to provide the Hosting Services internally or through the facilities of its third party vendor; and 15 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential

7.2.4 The rights and obligations of the Parties under the provisions of this Section 7.2, and solely to the extent that they relate to the Hosting Service all other terms, Exhibits and addenda, shall terminate effective as of the Hosting Termination Date, provided that any obligation on the part of Verizon including the obligation to pay any Fees, in respect of the Hosting Service for periods prior to the Hosting Termination Date, and any applicable early termination charges as set forth in the Authorization Letter, shall survive the Hosting Termination Date. In addition, the respective obligations of the Parties relating to the Hosting Service that by their nature would continue beyond the Hosting Termination Date, including but not limited to the obligations to indemnify, maintain confidentiality, maintain records and permit audits, shall survive the Hosting Termination Date with respect to the Hosting Service. 8. DEVELOPMENT SERVICES 8.1 Custom Software Development/Paid Work Product Supplier will design, develop, document, test and deliver the Custom Software or Paid Work Product identified in an Authorization Letter in accordance with the Service Requirements, Milestones and other terms of that Authorization Letter. Supplier shall comply with Verizon’s reasonable requests for changes to the Service Requirements that do not, either individually or in the aggregate, require more time, cost or effort from Supplier. 8.2 Background Materials Supplier will not include any Background Materials in the Custom Software or Paid Work Product without Verizon’s prior written consent (an express identification of such Background Materials within the applicable Authorization Letter shall be acceptable as Verizon’s consent for such purpose). For all Background Material used or included in Custom Software or Paid Work Product, Supplier grants to Verizon a royalty free, non-exclusive transferable, sublicensable irrevocable worldwide license to Use such Background Material except as set forth in an Authorization Letter. As used herein, to Use the Background Material means to use, display, perform, modify, enhance, reproduce and make derivative works for any purpose. 8.3 Status of Information Supplier shall allow personnel of Verizon to visit Supplier’s place of business at reasonable times to discuss and inspect the status of the development of the Custom Software or Paid Work Product upon prior written notice and provided such visit does not adversely affect or interfere with such development. In addition, appropriate personnel of the Parties will meet at least weekly during the course of development to review the status of the development of the Custom Software or Paid Work Product. 16 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential

8.4 Documentation Documentation for Custom Software shall be provided in a machine-readable format unless another format is agreed to by Verizon. Documentation shall comply with commonly accepted industry standards with respect to content, size, legibility and reproducibility, and shall include without limitation the following, as applicable: (i) administration; (ii) features and technical specifications; (iii) detailed engineering and circuit design; (iv) installation and testing criteria; (v) operations, provisioning and translations; (vi) maintenance and diagnostics; and (vii) other documentation deemed necessary by the parties to support the installation, acceptance testing, administration, maintenance, engineering and operation of the Custom Software, and the full exercise of the ownership rights, if any, herein acquired by Verizon. 9. SECURITY 9.1 Supplier shall put in place and shall maintain physical and electronic measures and operational procedures to protect the security of each Platform, and Software in compliance with the security requirements as set forth in Exhibit C hereto as such may be supplemented or modified in the applicable Authorization Letter. 9.2 Verizon, at its sole cost, may conduct reasonable Security Audits of a Platform or Software and related facilities of Supplier used in connection with Supplier’s performance of any Services (a “Security Audit”). Such Security Audit shall be performed by Verizon itself or on its behalf by a reputable security audit company selected by Verizon at mutually agreed upon times upon reasonable notice and subject to such company agreeing in writing with Verizon to the protection of any Supplier confidential information and provided that such Security Audit does not adversely impact Supplier or any services provided by Supplier to any other customer. 9.3 Each Party shall be entitled to receive a copy of any initial or final written report or recommendations resulting from any Security Audit and, unless Supplier disputes such recommendation on the grounds its implementation would not be in accordance with industry standards applicable to providers of service or software comparable to the Services and Software, Supplier shall promptly implement such recommendations. 10. ADDITIONAL REQUIREMENTS 10.1 Service Level Agreement Supplier shall comply with all terms of the Service Level Agreement attached to the applicable Authorization Letter. 10.2 Disaster Recovery 10.2.1 Supplier’s Disaster Recovery Plan is attached hereto as Exhibit D. Supplier shall exercise such plan on no less than an annual basis. 17 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential

10.2.2 Supplier shall update the Disaster Recovery Plan as reasonably necessary during the Term to include a list of all hardware, software and communications facilities and services used by Supplier to provide the Hosting Service. Verizon shall have the right to reasonably audit Supplier’s compliance at reasonable times as Verizon deems necessary provided such audit does not adversely impact Supplier or any services provided by Supplier to any other customer. Verizon’s review of any changes to the Disaster Recovery Plan shall not in any way alter or waive any of Suppliers duties, obligations, representations or warranties under this Agreement. 10.3 Training Upon request from Verizon, Supplier shall provide training outlined in the applicable Authorization Letter upon the terms set forth in such applicable Authorization Letter. Verizon shall have the right to duplicate or reproduce (including any markings as to confidentiality and copyrights), for internal usage only, any of the training materials at no additional cost. 10.4 Branding Unless otherwise stated in the applicable Authorization Letter, nothing in this Agreement shall be construed to limit or restrict Verizon’s rights to market and have marketed a Data Service or Software as Verizon determines, using Verizon own Trademarks or the Trademarks of one or more Indirect Channel Entities; provided Verizon does not remove any applicable copyrights. 10.5 International Roaming Access All Software and Services are intended to be used to enable Verizon to provide the Data Service to Subscribers who are customers purchasing Verizon Services in the United States. However, Supplier acknowledges and agrees that Verizon may, in its sole discretion, enable Subscribers to access and use a Data Service using Wireless Devices while roaming outside the United States pursuant to international data roaming agreements that Verizon may enter into with other wireless carriers. 11. FEES/PAYMENT 11.1 Pricing During the Term of this Agreement, Verizon shall pay Supplier for Service and/or Software in accordance with each applicable Authorization Letter. All payments are due in U.S. Dollars. All charges to Verizon for Services or Software are as set forth in each applicable Authorization Letter or, for modifications to a Service or Software, in a Change Request. 11.2 Improvements Supplier and Verizon shall continue to identify areas for Supplier’s continuous improvement in cost, quality and service over the term of the Agreement. 18 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential
Supplier shall afford Verizon the ability to realize the benefit of such improvements, including price reductions to the extent the Parties mutually agree in a Change Request. Furthermore, a list of continuous improvement initiatives shall be created by the Parties. Unless otherwise set forth in this Agreement, Supplier and Verizon will meet, upon Verizon’s reasonable request, to assess opportunities to implement potential continuous improvement initiatives, such initiatives to be mutually agreed to by the parties in a Change Request. 11.3 Invoices Unless otherwise specified in an Authorization Letter , Supplier shall render invoices following the date of initial Acceptance as set forth in Section 14; provided, however, where payment is not expressly contingent on Acceptance or where payment is on a per-subscriber basis, no Acceptance shall be required. Invoices for charges specified in an Authorization Letter shall be submitted by Supplier to the address specified in the Authorization Letter. Invoices shall include, as appropriate, without limitation (i) Authorization Letter number; (ii) description of Software and Services provided; (iii) ship-to name and address; (iv) delivery method (i.e., electronic or physical); (v) date of delivery (vi) quantity shipped and billed or quantity of service units performed and billed; (vii) maintenance service details; (viii) net unit cost; (ix) discounts applied; (x) net invoice amount; (xi) contract information for invoice disputes; and such other details as Verizon may reasonably request. 11.4 Payment Terms Verizon shall remit payment to Supplier within **** of Verizon’s receipt of Supplier's undisputed invoice, unless otherwise set forth in the applicable Authorization Letter; provided, however, if Verizon disputes any charge shown on a Supplier invoice, Verizon shall notify Supplier in writing of such dispute, and shall pay when due, any undisputed amounts. Supplier will provide Verizon with notice of any nonpayment if any. Upon request, Verizon will provide reasonable support for such dispute. 11.5 Electronic Payments At Verizon’s option Supplier will do the following: Verizon may, at no additional cost to Verizon, require Supplier to accept purchase orders and submit invoices via Verizon’s electronic payment system; provided that Supplier is not charged for the use or access of such system. Any terms or conditions associated with the use of the electronic payment system shall be negotiated directly between the Supplier and the electronic payment system provider. Transactions under this Agreement using the electronic payment system shall be governed by the terms and conditions of this Agreement. 11.6 Right of Set Off Verizon shall be entitled to set off any amount Supplier owes Verizon against amounts payable under this or any other Agreement. Payment by Verizon shall not result in a waiver of any of its rights under this Agreement. Verizon shall not be obligated to pay Supplier for Services that are not fully and properly invoiced. 19 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential ****CERTAIN INFORMATION HAS BEEN OMITTED AND FILED SEPARATELY WITH THE COMMISSION. CONFIDENTIAL TREATMENT HAS BEEN REQUESTED WITH RESPECT TO THE OMITTED PORTIONS
11.7 Charges to Subscribers. Supplier acknowledges and agrees that the fees charged by Verizon to Subscribers for their use of the Data Service or Verizon Network needed to download the Software required for a Data Service, as well as the fees charged Subscribers for downloading the Software, will be determined by Verizon in its sole discretion. Supplier also acknowledges and agrees that Verizon alone will be responsible for billing Subscribers, as well as for all associated collection activity, for such fees. 12. RECORDS AND REPORTS 12.1 Supplier shall allow Verizon and its authorized agents and representatives to audit Supplier’s records (in whatever form kept) to verify Supplier’s compliance with all provisions of this Agreement provided such agents and representatives agree with Verizon to keep any such information confidential. At Verizon’s request, the auditor shall have access to Supplier’s records at reasonable times during the Term and during periods in which Supplier is required to maintain records with not less than ten (10) days prior written notice to Supplier and provided that the timing of such audit does not adversely affect Supplier or its personnel. Supplier shall maintain complete records of all charges payable by Verizon under the terms of this Agreement for the later of three (3) years after termination of the Agreement and any additional period of applicability of the Agreement to an Authorization Letter placed prior to termination. Such records shall specifically include, but are not limited to, timesheets. All such records shall be maintained in accordance with recognized accounting practices. The correctness of Supplier's billing shall be evaluated by such audits. Unless such results are reasonably disputed by Supplier in accordance with Section 39, prompt adjustments shall be made to compensate for any errors or omissions disclosed by such review or examination. If such review or examination determines that Verizon has made an overpayment in excess of seven and one-half percent (7.5%) of the amount properly due, then Supplier shall reimburse Verizon for the entire reasonable cost and expense of such review and examination. From time to time, Verizon may request Supplier to provide an Export Control Classification Number (ECCN) for products, software, reports, technology or technical data licensed, purchased or available for license or purchase under this Agreement to the extent applicable. Supplier agrees to promptly, and without additional cost to Verizon, comply with any such requests. 12.2 If Supplier is itself a Certified Minority, Woman, Service Disabled Veteran and Person with Disability Owned and Controlled Business Enterprises (MWDVBE), as defined herein, Supplier shall retain its MWDVBE certification through the term of this Agreement. If there is a change in Supplier’s certification status, Supplier shall notify Verizon, in writing, within five (5) business days of the date of such change. If the Supplier is not itself a Certified Minority, Woman, Service Disabled Veteran and Person with Disability Owned and Controlled Business Enterprises (MWDVBE), then with respect to the Supplier's compliance (as the Primary Supplier) with Minority, Woman, Service Disabled Veteran and Person with Disability-Owned Business Enterprises (MWDVBE) Utilization, Supplier agrees to maintain a plan to provide opportunities for Certified MWDVBE suppliers and use 20 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential

commercially reasonable efforts, to the extent consistent with the terms, pricing and requirements of any SOW under this Agreement to meet the requirements set forth in Exhibit E, Compliance with Certified Minority, Woman, Service- Disabled Veteran and Person with Disability-Owned and Controlled Business Enterprises (MWDVBE) Utilization. For purposes of this Section, the definitions set forth in Exhibit E shall apply. For the avoidance of doubt, failure to meet the requirements set forth in Exhibit E shall not be deemed a breach of this Agreement, so long as commercially reasonable efforts were made. 13. DELIVERY 13.1 Supplier shall make Services and Software available to Verizon no later than the date mutually agreed to in the applicable Authorization Letter (the “Delivery Dates”); provided that if Supplier misses a Delivery Date due to the failure of Verizon or its agents, representatives or contractors to reasonably meet express dependencies contained in an applicable Authorization Letter, the parties will discuss whether such Delivery Date shall be extended accordingly; provided, however, in each case, Supplier shall have no liability for such delay in the event such Delivery Date is missed due to such Verizon failure. Notwithstanding such Delivery Dates, Verizon shall have the right to determine the Commercial Service Date for a Data Service in its sole discretion. 13.2 Packaging Software (where delivery in other than electronic format is specified in an Authorization Letter) shall be packaged for shipment, at no additional charge, in commercially suitable containers, consistent with all applicable laws that provide protection against damage during the shipment, handling and storage of the Software as specified in an Authorization Letter. 13.3 Risk of Loss Supplier shall bear the risk of loss of or damage to the Software until receipt of such Software specified in an Authorization Letter. Supplier shall promptly replace such Software when media on which it is shipped is lost or damaged at no additional charge. 14. TESTING, EVALUATION AND APPROVAL 14.1 Acceptance 14.1.1 All Software and Services shall be subject to inspection and Acceptance by Verizon after delivery of the Software and/or Services to determine conformity with this Agreement, the applicable Authorization Letter and Service Requirements, as applicable, and any applicable criteria for Acceptance. If delivery of Software will be made in a series of deliverables based on Milestones, then each such deliverable shall be inspected and Accepted individually, and the procedures, obligations and other terms of this Section shall apply to each deliverable. Inspection or failure to inspect on any occasion shall not affect Verizon’s rights under the warranty provisions of this Agreement or any other rights or remedies available to Verizon. Verizon’s right to inspect and test does not relieve 21 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential

Supplier from its testing, inspection and quality control obligations. Unless an alternative Acceptance mechanism or deemed Acceptance procedure is specified in an Authorization Letter and except as provided under Section 14.1.5, Statement of Work or elsewhere in this Agreement, Software and Services shall not be deemed Accepted unless such Acceptance is in writing. 14.1.2 Except as set forth in an Authorization Letter, Verizon shall have a period of **** following delivery of the Software and/or Service within which to test the Software and/or Service for conformity with this Agreement, the applicable Authorization Letter and Verizon Service Requirements, as applicable, and any applicable criteria for Acceptance. If the Software and/or Service fails to so conform, Verizon may, provide written notice (email shall be acceptable for this purpose) to Supplier rejecting such Software and/or Service. Following such notification, Supplier shall use commercial reasonable efforts, within ****, at Supplier's risk and expense, to correct all deficiencies by repairing or replacing any non-conforming Software. If, after the cure period, the Software and/or Service still fails to perform in accordance with the applicable criteria for Acceptance and Supplier is not able to correct such deficiency, it shall require that Verizon return the impacted Software and/or Service to Supplier at Supplier’s expense. 14.1.3 If such Software and/or Service is rejected above, any one-time amounts paid to Supplier by Verizon specifically for the impacted Software release and/or Service milestone shall be refunded to Verizon within **** after return of the impacted Software and/or Service; provided, however, in no event shall this provision apply to a refund of any transaction fees related to the Platform. The purchase price for such Software and/or Service also shall be credited against any future volume commitments or applied for evaluation of attainment of volume discounts under this Agreement applicable to such Software and/or Service. 14.1.4 Verizon has the right to subject the initial release of the Software and/or Service, and each subsequent Software release containing new functionality or enhancements intended for commercial production, to an operational soak period as part of the Acceptance testing. Soak period means using the Software and/or Service in a productive operation mode for ****. If the Software and/or Service does not perform according to the Service Requirements during the soak period, Supplier, at no additional charge, shall provide technical support personnel, to perform tuning services in order to meet the Service Requirements. If such tuning efforts are unsuccessful (i.e., the Software or Service will not perform to Service Requirements) after a reasonable period of time, in addition to its other remedies at law, equity or under this Agreement, (i) Verizon may return the Software release which was subjected to the soak period, and Supplier shall refund all monies paid for the applicable Software or Service release that was subjected to the soak period (provided, however, in no event shall this provision apply to a refund of any transaction fees related to the Platform) or (ii) Verizon, retaining all rights and remedies including those under (i), may extend the soak period 22 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential ****CERTAIN INFORMATION HAS BEEN OMITTED AND FILED SEPARATELY WITH THE COMMISSION. CONFIDENTIAL TREATMENT HAS BEEN REQUESTED WITH RESPECT TO THE OMITTED PORTIONS

and tuning-related services until such time as Verizon agrees is required for the Software and/or Service, as the case may be, to meet the Service Requirements. 14.1.5 If the Software and/or Service successfully passes Acceptance testing (including the operational soak period) Verizon shall timely issue its written notice that the Software and/or Service has successfully completed such test procedures and Acceptance; provided, however if no notice is provided by Verizon within the applicable period, such Software and/or Service shall be deemed accepted. 14.2 Nonconformance After Commercial Service Date After Commercial Service Date and Acceptance, if a Service or Software does not conform to the Service Requirements, Verizon shall be entitled to the remedies set forth in the applicable Service Level Agreement. 15. REPRESENTATIONS AND WARRANTIES Supplier represents and warrants that: 15.1 In performing Services and providing Software, Supplier will comply with the descriptions and representations which appear herein and in the applicable Service Requirements which shall include, with respect to any Apps, the App Store Developer Agreement applicable with respect to such App. Without limiting the preceding sentence, or the applicable Service Level Agreement, Supplier agrees to disclose and report all Unscheduled Outages, as defined in the applicable Service Level Agreement, in accordance with such Service Level Agreement and acknowledges that its failure to do so may degrade service that Verizon may be obligated to provide Subscribers, may cause adverse publicity regarding the Verizon Service, or jeopardize the security of the Verizon Network. 15.2 Its employees will perform Services in accordance with all applicable laws, codes, ordinances, orders, rules and regulations of local, state, and federal governments and agencies and instrumentalities, including, but not limited to, applicable wage and hour, economic and trade sanctions, bribery of foreign officials, safety and environmental laws, and all applicable standards and regulations of appropriate regulatory commissions and similar agencies. 15.3 All Services and Software furnished by Supplier shall be performed and provided (i) in a diligent, efficient and skillful manner, and (ii) in accordance with industry standards in the field. 15.4 All Software and Custom Software furnished by Supplier shall be free of Errors for a period of **** (or such greater period referenced in an Authorization Letter) following Acceptance of such Software or Custom Software. If within **** (or such aforementioned greater period) from the Acceptance of Software and/or Custom Software any Error exists or arises, then, in each such case, upon receipt of written notice of such Error from Verizon, Supplier will use commercial reasonable efforts to repair or remedy such Error at Supplier's sole cost and expense 23 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential ****CERTAIN INFORMATION HAS BEEN OMITTED AND FILED SEPARATELY WITH THE COMMISSION. CONFIDENTIAL TREATMENT HAS BEEN REQUESTED WITH RESPECT TO THE OMITTED PORTIONS
15.5 Supplier, including its employees, agents and contractors, has obtained and will maintain for the Term of this Agreement, any Permits (as such term is defined in Section 30) reasonably necessary for the performance of Services. 15.6 Supplier owns the Software and Background Materials (other than third party components of the Software) and has the right to license the same to Verizon under the terms of this Agreement. As to Software and Background Materials to which Supplier does not have title, Supplier represents and warrants that it has rights in the Software and Background Materials sufficient to permit the license of the Software to Verizon and that Software has full right, power and authority to license the Software and Background Materials and other rights granted hereunder to Verizon. 15.7 Services and Software provided or performed by Supplier under this Agreement do not and will not give rise to or result in any infringement or misappropriation of any third party patent, copyright, trade secret, or any violation of any other intellectual property right of any third party. 15.8 Forward and Backward Compatibility Except as set forth in an Authorization Letter, Supplier represents and warrants that, for a period of **** following the commercial release of any new supported Wireless Device (such timeframe with respect to each release, the “Rolling Window”), new versions of Software other than Custom Software with respect to which Verizon has waived in writing Supplier’s obligations under this Section 15.8 (Verizon acknowledges that execution of an SOW that expressly excludes support for Custom Software shall be deemed such waiver and Custom Software may require additional fees to maintain compatibility as provided in an applicable Authorization Letter), shall be forward and backward compatible, contain materially similar functionality to and be substantially compatible with such Wireless Device and their operating environment(s). If set forth in an Authorization Letter, new versions of Software, that do not otherwise compromise or break the functionality of the Software on Wireless Devices released prior to the Rolling Window, are not required to incorporate all new incremental feature enhancements contained in such new Software release. The Rolling Window shall apply to any Wireless Device commercially released after **** and supported by the Platform. In the event Supplier deploys a server side Software change that causes Supplier to breach the above warranty in this Section 15.8 with respect to Wireless Device client Software, Supplier shall upgrade the Software used on the affected Wireless Device at no additional fee, provided Verizon is current on its Maintenance payments. 15.9 No Viruses 15.9.1 Supplier represents and warrants to Verizon that Software does not contain or will not contain any Self-Help Code or any Unauthorized Code. Supplier shall remove promptly any such Self-Help Code or Unauthorized Code in the Software of which it is notified or may discover. 15.9.2 Supplier also represents and warrants that there are no copy protections or similar mechanisms within the Software, which will, either now or in the 24 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential ****CERTAIN INFORMATION HAS BEEN OMITTED AND FILED SEPARATELY WITH THE COMMISSION. CONFIDENTIAL TREATMENT HAS BEEN REQUESTED WITH RESPECT TO THE OMITTED PORTIONS

future, interfere with the grants made in this Agreement. Furthermore, Supplier represents and warrants that unless otherwise noted in the applicable Documentation or (a) requested in writing by Verizon and Verizon approves Supplier’s response, or (b) Supplier advises Verizon in writing that it is necessary to perform valid duties under this Agreement and authorized in writing by Verizon, Software shall not: (i) contain hidden malicious files; (ii) replicate, transmit or activate itself without control of an authorized person operating computer equipment on which it resides; (iii) alter, damage or erase any data or computer programs without control of an authorized person operating the computer equipment on which it resides; and (iv) contain no encrypted imbedded key, node lock, time out or other function, whether implemented by electronic, mechanical or other means, which restricts or may restrict Use or access to any programs or data developed under this Agreement, based on residency on a specific hardware configuration, frequency or duration of Use, or other limiting criteria (collectively “Illicit Code”). Should any Software be found by Verizon or Supplier to contain Illicit Code, Supplier shall immediately commence the removal, at Supplier’s sole cost, of such Illicit Code. Notwithstanding anything elsewhere in this Agreement to the contrary, In the event that Verizon or any Subscriber has been damaged in any material respect by the access or use of such Illicit Code, or if Supplier activates such Illicit Code at any time, Supplier shall be in default of this Agreement, and no cure period shall apply. It is agreed that a breach of the above representation and warranty may cause irreparable harm and injury and Verizon shall be entitled, in addition to any other rights and remedies it may have at law or in equity, to seek an injunction enjoining and restraining Supplier from doing or continuing to do any such act and any other violations or threatened violations of the Agreement. In addition to any other remedies available to it under this Agreement, Verizon reserves the right to pursue any civil and/or criminal penalties available to it against the Supplier. 15.10 Offshore Restrictions 15.10.1 Except with Verizon’s advance written consent, in no event shall Confidential Information regarding or pertaining to Verizon’s systems, infrastructure, employees, or customers be stored, transmitted, or accessed at, in, through or from a site located outside the United States nor made available to any person who is located outside the United States unless such Confidential Information relates solely, directly and independently (i) to Verizon employees or customers located outside of the United States, or (ii) to voice or data communications of Verizon or its customers that originate and terminate outside the United States, or (iii) to Verizon systems and/or infrastructure dedicated to the provision of Verizon’s voice or data services outside the United States or, (iv) to be otherwise necessary for storage or access outside the United States in connection with security, back-up, disaster recovery, or related purposes as required by Verizon services specifications, security and/or technical requirements. This subsection shall not apply to Verizon Wireless Customer Data which shall be solely governed by the provisions of Subsection 15.10.3. 25 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential

15.10.2 Exceptions to 15.10.1 above will be granted, in Verizon’s sole discretion, (i) in writing; (ii) on a project-specific or statement-of-work- specific basis; (iii) following a review of the particular project or statement of work in accordance with the policies of the relevant Verizon business unit governing the placement of work with resources located outside the United States; (iv) subject to any conditions imposed by Verizon on the access to systems or data by such resources as a result of such review; and (v) in advance of the commencement of any work by such resources on the relevant project or statement of work. 15.10.3 Notwithstanding subsection 15.10.1and 15.10.2 above, unless Supplier secures Verizon Wireless’ further, prior written consent, in no event (i) shall Supplier provide, direct, control, supervise, or manage any voice or data communication of Verizon Wireless customers that occurs between United States locations (or the United States portion of any international communication that may originate or terminate within the United States) from a location outside of the United States, nor (ii) shall Verizon Wireless Customer Data be stored, transmitted, or accessed by Supplier, from, at, in, or through a site located outside the United Stated without Verizon Wireless’ prior written consent. “Verizon Wireless Customer Data” shall include (a) any subscriber information, including, without limitation, name, address, telephone phone number or other personal information of the Verizon Wireless subscriber; (b) any call- associated data, including without limitation, the telephone number, internet address or other similar identifying designator associated with a communication; (c) any billing records; (d) the time, date, size, duration of a communication or physical location of equipment used in connection with a communication; or (e) the content of any Verizon Wireless customer communication. This section is not intended to limit Subscriber’s access to Data Services from outside of the United States as permitted pursuant to Section 10.5, and Supplier shall not be in breach of this Section due to such permitted international roaming by Subscribers. 15.10.4 Nothing in this Section is intended to nor shall it operate in derogation of any requirement imposed on Verizon by a governmental body or agency outside the United States. 15.11 Supplier shall remove from the project, at Verizon’s request, any person furnished by Supplier who, in Verizon’s reasonable opinion, is incapable, uncooperative or otherwise unacceptable in the execution of the services to be provided under this Agreement; provided compliance with such request does not violate any law or regulation. 15.12 Warranty Disclaimer. EXCEPT FOR THOSE WARRANTIES EXPRESSLY STATED IN THE AGREEMENT OR APPLICABLE AUTHORIZATION LETTER, SUPPLIER HEREBY DISCLAIMS ALL OTHER WARRANTIES, WHETHER EXPRESS OR IMPLIED, ORAL OR WRITTEN, WITH RESPECT TO THE PLATFORM, SOFTWARE AND SERVICES INCLUDING, WITHOUT LIMITATION, ALL 26 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential

IMPLIED WARRANTIES OF TITLE, NON-INFRINGEMENT, QUIET ENJOYMENT, ACCURACY, INTEGRATION, MERCHANTABILITY OR FITNESS FOR ANY PARTICULAR PURPOSE AND ALL WARRANTIES ARISING FROM ANY COURSE OF DEALING, COURSE OF PERFORMANCE OR USAGE OF TRADE. 16. ESCROW 16.1 Maintenance of Escrow Agreement. Promptly after the Effective Date, Supplier shall enter into an Escrow Agreement with an escrow agent approved by Verizon in writing (the “Escrow Agent”) to secure Verizon’s rights hereunder and to be effective as of the Effective Date (the “Escrow Agreement”), such Escrow Agreement to be approved by Verizon. The Escrow Agreement shall be an agreement separate from, but supplemental to, this Agreement. Such Escrow Agreement shall be established and maintained for the benefit of Verizon and its Affiliates, and should such Escrow Agreement terminate or otherwise expire during the Term, the Parties shall immediately enter into a new Escrow Agreement with an independent escrow agent mutually satisfactory to Supplier and Verizon in accordance with the provisions of this Section 16. 16.2 Escrow Deposits. Upon execution of the Escrow Agreement, Supplier shall deposit copies of the then-current Escrow Materials to the escrow service provider, subject to the terms and conditions of the Escrow Agreement, which deposit shall be promptly and routinely supplemented by Supplier and otherwise kept current so as to accurately reflect the Source Code for the then current version of the Software under license to Verizon (including Releases or Updates provided to Verizon hereunder as well as any other material upgrade or modification of or enhancement thereto), and the same shall be part of the Escrow Materials. Supplier shall designate a mutually acceptable neutral third party who, at the expense and request of Verizon made from time to time, shall audit the materials deposited with the escrow agent for purposes of determining whether Supplier has fulfilled its deposit obligations. Supplier will promptly correct any deficiency disclosed by the audit. 16.3 Release Conditions. Release of the Escrow Materials to Verizon shall be granted on the terms and conditions (including for notice and redeposit) set forth in the Escrow Agreement and as otherwise set forth herein, but in any event whenever: 16.3.1 Supplier indicates to Verizon that it is reasonably likely to materially breach this Agreement with respect to the continued provision of Maintenance Services or other maintenance and/or support expressly required by this Agreement and the same is not remedied within **** after written notice from Verizon; 16.3.2 Supplier applies for or consents to the appointment of or the taking of possession by a receiver, custodian, trustee or liquidator of itself or of all 27 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential ****CERTAIN INFORMATION HAS BEEN OMITTED AND FILED SEPARATELY WITH THE COMMISSION. CONFIDENTIAL TREATMENT HAS BEEN REQUESTED WITH RESPECT TO THE OMITTED PORTIONS

or a substantial part of its property; makes a general assignment for the benefit of creditors; commences a voluntary case under the Federal Bankruptcy Code or fails to contest in a timely or appropriate manner or acquiesces in writing to any petition filed against it in an involuntary case under such Bankruptcy Code or any application filed against it for the appointment of a receiver, custodian or trustee or for the reorganization, dissolution or liquidation of itself or all or a substantial part of its property. 16.4 License. Unless other release license rights are specified in an applicable Authorization Letter, in the event of a release of the Escrow Materials to Verizon pursuant to the Escrow Agreement, Supplier shall be deemed to have granted to Verizon a non-transferable, non-exclusive, perpetual, irrevocable, enterprise wide, worldwide license and right to Use and modify the released Software and Source Materials and to create derivative works thereof under the terms and conditions of this Agreement solely to continue to support the Software consistent with the Maintenance and Support provided under this Agreement, subject to Verizon’s payment of the applicable fees set forth below. The Parties agree that any use by Verizon of any Escrow Materials pursuant to this Agreement and/or any Escrow Agreement will be subject to (a) payment by Verizon of any License Fees set forth in an Authorization Letter less the component of such fees attributable to maintenance and support equal to **** of such License Fees plus an amount attributable to added requirements of Verizon equal to **** of such License Fees (collectively a reduction of **** of such License Fees) and (b) all of the terms, restrictions and conditions of the Agreement, as amended and the following conditions and obligations: Verizon will (i) treat the source code (and those Escrow Materials that would otherwise be Confidential Information) as Confidential Information; (ii) use password protection to limit access to source code to authorized employees, agents and contractors of Verizon who require access to perform their duties under this Agreement, as amended; and (iii) make no copies of the source code in machine-readable or human-readable form except as reasonably required to perform the activities permitted under this Agreement. Upon such Release Condition, Supplier shall have no further obligation for maintenance and support of such Software or providing Hosting Services. Notwithstanding the foregoing, the fees set forth in (a) above for use of the Escrow Materials shall not apply in the event of a termination of this Agreement by Verizon due to a material breach by Supplier. Should Verizon’s Use of the Source Materials involve Use or copying of copyrighted material or the practice of any invention covered by a patent, Supplier shall not assert such copyright, patent or other right in intellectual property against Verizon. 16.5 Bankruptcy. The obligations of Supplier under this Section 16 (Source Code Escrow) shall extend to any trustee in bankruptcy, receiver, administrator or liquidator appointed for Supplier, to Supplier as debtor-in-possession (collectively, the “Trustee”) and to any other successor in interest to Supplier. Without limiting the generality of the foregoing, upon written request of Verizon, Supplier shall not interfere with the rights of Verizon as provided in this Agreement or the Escrow 28 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential ****CERTAIN INFORMATION HAS BEEN OMITTED AND FILED SEPARATELY WITH THE COMMISSION. CONFIDENTIAL TREATMENT HAS BEEN REQUESTED WITH RESPECT TO THE OMITTED PORTIONS
Agreement to obtain the Escrow Materials from the Trustee, the escrowee or any other person or entity having possession thereof, and shall, if requested under the conditions specified in the Escrow Agreement for release of the Escrow Materials, cause a copy of such Escrow Materials to be made available to Verizon. Notwithstanding anything in this Agreement to the contrary, Verizon reserves all rights available to it under Section 365(n) of the Federal Bankruptcy Code, 11 U.S.C. § 365(n) or any equivalent or successor provision thereto and such rights as may be available under other applicable laws. 16.6 Dispute Resolution. Supplier may dispute in good faith the existence of the release conditions described in Section 16.3 and such disputes will be subject to final and binding arbitration by a three-arbitrator panel wherein each party shall select an arbitrator, and those two arbitrators shall jointly select a third, and the panel’s written decision must be provided within **** of the date such arbitration claim is submitted. The panel will be required to furnish, promptly upon conclusion of the arbitration, a written decision, setting out the reasons for the decision. The arbitration decision will be final and binding on the Parties, and the decision may be enforced by either Party in any court of competent jurisdiction. The arbitration will be conducted in New York, NY under the then current Commercial Dispute Resolution procedures of the American Arbitration Association ("AAA"). Each Party will bear its own expenses and an equal share of the expenses of the third arbitrator and the fees, if any, of the AAA, unless the arbitrator rules otherwise as detailed above. The effectiveness of the license described in Section 16.4 (and any release of the Escrow Materials) shall be delayed until such disputes are resolved in Verizon’s favor by the arbitrator/panel. 16.7 Survival. The obligations set forth in this Section shall survive and remain in effect until the later of (i) all obligations of Supplier to provide maintenance and support for the Software to Verizon, including to provide Maintenance Services, whether pursuant to this Agreement or after the expiration or termination of this Agreement, or (ii) termination or expiration of any separate agreement between the Parties with respect to maintenance and support for the Software. 16.8 Definitions. For purposes of this Section 16: 17.6.1 “Escrow Agreement” means an agreement executed by Supplier and Verizon which is separate from, but supplemental to, this Agreement and which sets forth the terms and conditions governing release of the Escrow Materials to Verizon. 16.8.2 “Escrow Materials” means the then-current Source Code for the Software,, all tools and other software required to translate or convert the deposited Source Code to executable code (e.g. software compilers, linkers, assemblers, translators and interpreters) that are not readily 29 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential ****CERTAIN INFORMATION HAS BEEN OMITTED AND FILED SEPARATELY WITH THE COMMISSION. CONFIDENTIAL TREATMENT HAS BEEN REQUESTED WITH RESPECT TO THE OMITTED PORTIONS

available to Verizon commercially off- the-shelf, and any Custom Software obtained through this Agreement. 17. TERMINATION 17.1 Supplier shall be in default if Supplier fails to perform any of its material obligations under this Agreement , and such failure to perform shall continue for a period of **** after Supplier's receipt of Verizon's written notice thereof, then, in addition to all other rights and remedies under this Agreement at law or in equity or otherwise, Verizon shall have the right, upon written notice, to immediately cancel any or all affected Orders or, at Verizon’s option, to terminate this Agreement, without any obligation or liability to Supplier for said termination or cancellation. 17.2 This Agreement may additionally be terminated, by written notice only, as follows: 17.2.1 Unless otherwise expressly provided in such Authorization Letter, Verizon may terminate any or all Authorization Letters issued hereunder without cause, effective upon **** notice, upon written notice to Supplier and, in such event, Supplier shall receive payment only in accordance with Section 17.4 hereof. 17.2.2 Supplier may terminate any affected Authorization Letter if Verizon fails to make timely payments of those portions of invoices that are not disputed in good faith as required hereunder, and any such failure is not remedied within **** after receipt of written notice by Supplier stating its intention to terminate such Authorization Letter. 17.2.3 By either party, effective immediately, upon written notice to the other party, if any of the following events occurs: 17.2.3.1 The other party files a voluntary petition in bankruptcy. 17.2.3.2 The other party is adjudged bankrupt. 17.2.3.3 A court assumes jurisdiction of the assets of the other party under a federal reorganization act. 17.2.3.4 A trustee or receiver is appointed by a court for all or a substantial portion of the assets of the other party. 17.2.3.5 The other party becomes insolvent or suspends its business. 17.2.3.6 The other party makes an assignment of its assets for the benefit of its creditors except as required in the ordinary course of business. 17.3 Upon termination of this Agreement, Supplier shall deliver to Verizon, and Verizon shall own, all Custom Software and Paid Work Product created by 30 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential ****CERTAIN INFORMATION HAS BEEN OMITTED AND FILED SEPARATELY WITH THE COMMISSION. CONFIDENTIAL TREATMENT HAS BEEN REQUESTED WITH RESPECT TO THE OMITTED PORTIONS

Supplier (subject to any Background Materials of Supplier incorporated therein) at and prior to the time of such termination to the extent owned by Verizon under this Agreement or any Authorization Letter and paid for by Verizon, including source code and Documentation, whether or not completed. Supplier also shall deliver to Verizon all Background Materials incorporated in such Custom Software or Paid Work Product not then in the possession of Verizon; but in no event shall Verizon’s rights to any Background Materials be deemed to permit Verizon to access the Platform operated by Supplier after such termination (subject to Section 17.6). Supplier shall, except as required by law or this Agreement, also return to Verizon all Verizon Confidential Information and Verizon will return to Supplier all Supplier Confidential Information. 17.4 Effect of Termination. Upon termination of this Agreement by Verizon for convenience, Supplier shall immediately curtail all activities hereunder upon the effective date set forth in the notice of such termination. Upon such termination, Verizon’s sole liability to Supplier will be the payment of (i) all amounts due for Services satisfactorily performed up to the effective date of termination, (ii) any termination fees or other charges set forth in an Authorization Letter and (iii) respecting Development Services, all amounts due Supplier for Software Milestones or work Accepted before the date of termination, plus payment for the next uncompleted Milestone on a time and materials basis based on number of hours worked (no hours prior to the execution of such Authorization Letter shall be included) multiplied by $****, capped at **** of the payment due for such Milestone under the applicable Authorization Letter; provided, however, in the event an Authorization Letter includes termination fees or charges, such stated termination fees or charges shall be in lieu of any other partial payments . Except as set forth above, in no event will Verizon be liable to Supplier either for compensation or for damages of any kind or character whatsoever, whether on account of the loss by Supplier of present or prospective profits on sales or anticipated sales, or expenditures, investments or commitments, made in connection with the establishment, development or maintenance of Supplier’s business, or on account of any other cause or thing whatsoever 17.5 Effect on Licenses. In no event shall termination of this Agreement (other than by Supplier pursuant to Section 17.2.2) impair Verizon’s right, title and interest to Custom Software or Paid Work Product acquired and paid for by Verizon, or other Supplier materials (including Background Materials or Supplier-retained Work Product) that are licensed on a perpetual, irrevocable or post-termination basis hereunder. The irrevocable nature of paid-for such licenses shall not preclude Supplier from seeking injunctive relief to prevent the reoccurrence or continuing of a breach of this Agreement by Verizon but such injunction may not restrict or limit Verizon’s use of the Custom Software or Paid Work Product within the scope of the license granted herein provided Verizon has fully paid for such Custom Software or Paid Work Product. 17.6 Upon expiration and/or termination of this Agreement or any Authorization Letter for any reason (except for termination by Supplier resulting from breach by Verizon under Section 17.2.2, in which case Supplier may demand prepayment for such services and any other amounts due hereunder), and at the request of Verizon, Supplier shall (a) for a period not to exceed **** after the date of termination (the “Transition Period”), continue to provide 31 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential ****CERTAIN INFORMATION HAS BEEN OMITTED AND FILED SEPARATELY WITH THE COMMISSION. CONFIDENTIAL TREATMENT HAS BEEN REQUESTED WITH RESPECT TO THE OMITTED PORTIONS

Services and Software to enable Verizon to utilize its Data Service (subject to the continued payment of undisputed payments by Verizon pursuant to the terms of this Agreement or as otherwise agreed by the parties) and (b) use reasonable efforts to assist Verizon to ensure a seamless migration without interruption to Subscribers (collectively, the “Transition Services”) on mutually agreed pricing and other terms but in no event shall Supplier be required under this subsection (b) to license its Platform to Verizon or such third party as part of the Transition Services. Without limiting the foregoing obligations, to the extent that any services are required, in addition to and beyond the scope of the Transition Services, to effect such transition to Verizon or another application service provider, the parties will mutually agree upon further terms (including fees) regarding the scope and schedule of such additional services. If Verizon does not request Transition Services, Supplier will cease providing the Service(s) at the time termination becomes effective. 17.7 The foregoing rights are in addition to, and not in limitation of, any other remedy a party may have at law or equity. 18. INFRINGEMENT 18.1 Supplier shall indemnify, defend and hold harmless Verizon, its parents, subsidiaries and Affiliates, its OEMs (subject to the limitations in Section 18.5) and its and their respective directors, officers, employees, agents, successors and assigns ("IP Indemnified Parties") from and against any claims, demands, lawsuits, liabilities, loss, cost or expenses (including, but not limited to, reasonable fees and disbursements of counsel and court costs), judgments, settlements and penalties of every kind ("IP Claims") arising from or relating to any actual or alleged infringement or misappropriation of any patent, trademark, copyright, trade secret or any actual or alleged violation of any other intellectual property or proprietary rights arising from or in connection with the Services (including related products furnished hereunder by Supplier) or Software provided under this Agreement. Notwithstanding anything to the contrary contained in this Agreement (including, but not limited to, Section 1), the provisions of this Section 8, shall govern the rights of Indemnified Parties with respect to indemnification for IP Claims. 18.2 The procedures, limitations and restrictions set forth in Section 31 (Indemnification) shall apply in the case of IP Claims hereunder. 18.3 Without limitation of Sections 18.1 and 18.2, if sale, use or if applicable, distribution, of the products or Services becomes subject to an IP Claim, Supplier shall, at Supplier’s option and Supplier’s expense: 18.3.1 Procure for Verizon the right to use the Services or Software (including related products furnished hereunder); 18.3.2 If 18.3.1 is not possible modify the Services or Software (including related products furnished hereunder) so they become non-infringing; 32 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential
18.3.3 If neither 18.3.1 or 18.3.2 is possible replace the Services or Software (including related products furnished hereunder) with substantially equivalent, non-infringing products and/or Services; or 18.3.4 If none of the above, are commercially feasible (for the purposes of this Section 18.3.4, the cost of the remedy shall be deemed “commercially feasible” if the costs of implementation thereof are less than the amount paid by Verizon to Supplier hereunder during the prior twelve months prior to such date for such impacted Service or Software), Supplier shall terminate the Services or Software (including related products furnished hereunder) and refund the purchase price paid therefor. 18.4 Exclusions. The obligations under Section 18.1 shall not apply with respect to any claim based upon (i) any use of the Software or Services not in accordance with this Agreement or the applicable Application Letter, if such infringement results solely from such use not in accordance with this Agreement or the applicable Application Letter, (ii) use of any Software or Services in an application or environment or on a platform or with devices for which it was not designed or contemplated in a Specification or Authorization Letter or otherwise authorized by Supplier, (iii) alterations, modifications or enhancements of the Software not created by or on behalf of Supplier where the unmodified Software would have avoided the claim; (v) combination of Software with software or other materials not provided or specified by or through Supplier, where the combination itself causes the infringement; (v); that portion of any Software which implements an IP Indemnified Party's (including an OEM’s) requirements where there was no non-infringing way to implement such requirement or (iv) IP Indemnified Party's continuing allegedly infringing activity after a reasonable period (which shall in no event be less than **** with respect to claims regarding Apps, and **** for all other claims) after being provided without charge Software modifications (without degradation of function or performance) that would have avoided the alleged infringement. 18.5 The indemnification obligations directly in favor of OEMs shall only apply where the Supplier’s technology has been pre-loaded on to such OEM’s device by mutual agreement. Further, for the avoidance of doubt, Supplier acknowledges and agrees that each OEM is an intended third party beneficiary of the indemnification obligations hereunder and, provided such OEM (as a precondition) makes no voluntary admission in respect of any IP Claim, grants to Supplier the exclusive right to defend and settle any IP Claim and affords such assistance to Supplier (at Supplier's cost) in the defense and settlement of such IP Claim as Supplier may reasonably require, then OEM shall be entitled to enforce this indemnity directly against Supplier. 19. CONFIDENTIAL INFORMATION The non-disclosure provisions set forth as Exhibit F shall apply to this Agreement. 33 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential ****CERTAIN INFORMATION HAS BEEN OMITTED AND FILED SEPARATELY WITH THE COMMISSION. CONFIDENTIAL TREATMENT HAS BEEN REQUESTED WITH RESPECT TO THE OMITTED PORTIONS

20. OWNERSHIP 20.1 Retention of Title by Verizon 20.1.1 Title to all materials and property Verizon provides to Supplier in connection with this Agreement shall remain in Verizon or, if applicable, its licensors or lessors. Without limitation of the foregoing, all Verizon Content, all Subscriber Data, all Usage Data, all Web Site style and design guides provided by Verizon, all Verizon Trademarks, and any alterations and/or modifications to the foregoing shall be and remain the proprietary information of Verizon, or, as the case may be, its Content Providers, its Subscribers or other third parties having rights therein. 20.1.2 Any materials or property Verizon provides Supplier, and any materials or property of Verizon or its Subscribers or Indirect Channel Entities that otherwise comes into Supplier’s possession or control in connection with a Data Service under this Agreement shall be used only in the performance of this Agreement, unless otherwise authorized in writing by Verizon. Supplier shall adequately protect all such material and property, and shall deliver or return it to Verizon or otherwise dispose of such individual and property as directed by Verizon. Supplier shall be responsible for any loss of or damage to tangible materials or tangible property owned by Verizon, or its licensors or lessors while in Supplier's possession or control. 20.2 Ownership Rights 20.2.1 The Platform and Background Materials (and any corrections, enhancements or modifications thereto but excluding Custom Software or Paid Work Product) shall be owned by Supplier. 20.2.2 For the purposes of this Agreement, “Work Product” shall mean all designs, models, prototypes, drawings, data storage media, listings, deliverables, technical data, inventions, improvements, discoveries, computer software (including firmware), and other forms of technology or intellectual property made, conceived, developed or actually or constructively reduced to practice by Supplier in connection with or pursuant to the terms and conditions of this Agreement, whether solely or jointly with others, and which are associated with, refer to, are suggested by, or result from any services which Supplier may perform pursuant to this Agreement, or from any information obtained by Supplier from Verizon or in discussions and meetings with employees of Verizon or any of its Affiliates including any reports to be prepared by Supplier for Verizon under this Agreement. For the avoidance of doubt, Work Product shall not include the Platform, Background Materials or any Documentation associated with the foregoing. 20.2.3 Rights in Work Product: 20.2.3.1 Subject to the last sentence of Section 20.2.2, Supplier hereby agrees that (i) Custom Software, and (ii) other creative 34 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential
works that VZ specifically pays for and is identified in an Authorization Letter as a Paid Work Product (“Paid Work Product”), are works made for hire exclusively for Verizon under the patent or copyright laws of the United States and shall become and remain the exclusive property of Verizon, and Verizon shall have the rights to use such for any purpose without any additional compensation to Supplier. In the event any Custom Software or Paid Work Product produced under this Agreement shall not be deemed to be a work made for hire exclusively for Verizon under the patent or copyright laws of the United States, Supplier hereby grants and assigns to Verizon all right, title and interest in and to (including the right to reproduce, modify, display, produce derivative works of, translate, publish, sell, use, dispose of, and to authorize others so to do, and the right to patent or copyright and to register such patent or copyright in Verizon’s or its nominee's name) all Custom Software or Paid Work Product, subject to Section 20.2.1. Supplier further agrees to assist Verizon in every proper way to protect Custom Software or Paid Work Product, including, but not limited to, signing patent and copyright applications, oaths or declarations, and assignments in favor of Verizon relating to the Custom Software or Paid Work Product, as well as such ancillary and confirmatory documents as may be required or appropriate to insure that such title is clearly and exclusively vested in Verizon, within the United States and in any and all foreign countries. Supplier further agrees to assist and cooperate with all efforts to enforce the rights of Verizon in such property against any third parties. 20.2.3.2 (a) Ownership of all Work Product that is not Custom Software or Paid Work Product shall be retained by Supplier (“Supplier-retained Work Product”). With respect to such Supplier-retained Work Product, Supplier grants to Verizon a nonexclusive, perpetual, fully paid up, royalty free, worldwide, irrevocable license under such Supplier-retained Work Product to make/have made, use, sell, have sold and otherwise provide Verizon products (through one or more intermediaries) to Verizon’s end-user customers. For the avoidance of doubt, the foregoing license rights to Supplier-retained Work Product shall not apply or extend to Verizon a license to Background Materials or to the Platform. (b) With respect to Custom Software or Paid Work Product consisting of/including improvements or enhancements to Supplier’s Background Materials (“Verizon-Owned Improvements to Background Materials”), such Verizon-Owned Improvements to Background Materials must be expressly identified as such in the applicable Authorization Letter in accordance with Section 20.2.6. 20.2.4 Supplier grants to Verizon a royalty-free, nonexclusive, transferable, sublicensable, and irrevocable license during the Term to any and all Background Materials which are incorporated in any Custom Software, 35 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential
Paid Work Product or other materials licensed to Verizon hereunder (provided, with respect to such other licensed materials, such license to incorporated Background Materials shall be coterminous with the license to such other licensed materials) under this Agreement to Verizon by Supplier, provided that such license shall only be to the extent that Supplier has, or prior to completion of final settlement of this Agreement, may acquire, the right to grant such license without becoming liable to pay compensation to others solely because of such grant. For the avoidance of doubt, but without limitation of the foregoing, Supplier retains ownership of all right, title and interest in and to, including any and all Intellectual Property Rights it may have, in Background Materials. 20.2.5 Supplier warrants and represents that it has or will have the right, through written agreements with all employees performing Services under or in connection with this Agreement, to secure for Verizon the rights called for in this Section. Further, in the event Supplier uses any subcontractor, consultant or other third party to perform any of the Services contracted for by this Agreement, Supplier agrees to enter into such written agreements with such third party, and to take such other steps as are or may be reasonably required to secure for Verizon the rights called for in this Section. 20.2.6 Identification Requirements. The parties shall identify Custom Software and Paid Work Product in each applicable Authorization Letter, which shall contain the following provisions to state the Parties’ intent as to the use of such Work Product: “OWNERSHIP OF WORK PRODUCT: For Custom Software, Paid Work Product or Verizon-Owned Improvements to Background Materials of Supplier: [LIST/DESCRIBE, IF ANY] CHOOSE 1: (a) Exclusive to Verizon. (b) Non-Exclusive. Verizon grants to Supplier a nonexclusive, perpetual, fully paid up, royalty free, worldwide, irrevocable license under such Improvements to Background Materials to make/have made, use, sell, have sold and otherwise provide Supplier products (through one or more intermediaries) to Supplier customers. 21. SUBSCRIBER DATA AND CONTENT 21.1 Subscriber Privacy Supplier shall (i) protect the privacy of Subscribers to the full extent legally required, (ii) promptly implement and comply with all policies and practices adopted by Verizon concerning the collection, storage, or use of Subscriber Data to the extent such policies have been provided in writing to Supplier and (iii) treat 36 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential
Subscriber Data as “Confidential Information” in accordance with Section 20 of this Agreement. As between the Parties, Verizon shall have the sole right to adopt and communicate to Subscribers statements about and descriptions of such policies and practices or any breach thereof. 21.2 Ownership of Data As between Supplier and Verizon, Verizon owns all right, title, and interest, including copyright and other proprietary rights, in CPNI, Subscriber Data and Usage Data, whether collected by Verizon or Supplier. 21.3 Use of Data In the event Services hereunder require Supplier access to and/or use of any CPNI, Subscriber Data or Usage Data, such shall be used only in the performance of Services hereunder and only to the extent necessary to provide such Services. Supplier shall have no right to record, monitor, reproduce, disclose, sub-license, re-sell or otherwise distribute all or any portion of CPNI, Subscriber Data or Usage Data to any person in any form or any manner other than as necessary or appropriate in providing Services hereunder. 21.4 Use of Content Except to the extent required to meet the Service Requirements, Supplier will not record, monitor or disclose any Subscriber’s use of any Content unless instructed to do so in writing by Verizon, or as required by law, regulation, or court order or as necessary to cooperate with a lawful order or demand of law enforcement officials. 21.5 Certain Confidential Information For greater certainty, and without limiting the terms of Exhibit F, all CPNI, Subscriber Data and Usage Data shall be Confidential Information of Verizon under the terms of Exhibit F. 21.6 Return or Destruction Upon the expiration or earlier termination of this Agreement Supplier shall deliver to Verizon all copies of Content, CPNI, Subscriber Data and Usage Data in the possession or control of Supplier and deliver a certificate of an officer certifying that Supplier has retained no copies thereof other than copies required to be retained under applicable law. Alternatively, Verizon shall have the right to instruct Supplier to delete and destroy, in a nonrecoverable manner, all copies of such information, and to witness and supervise such deletion and destruction, directly or using appropriately qualified agents designated by Verizon. Notwithstanding anything to the contrary in this Agreement or Exhibit F, for so long as any CPNI, Subscriber Data and Usage Data remains in the possession or control of Supplier, it shall be deemed “customer information” of Verizon for purposes of Section 2 of Exhibit F. 37 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential
21.7 No Advertising Except as otherwise provided in an Authorization Letter, Supplier shall not place or display, allow third parties to place or display, or otherwise enable or allow transmission to Subscribers via Platform of any advertisements, announcements, or other messages without the prior written consent of Verizon. 21.8 Unsolicited Commercial Messages Supplier shall use commercially reasonable efforts to ensure that no unauthorized third parties are able to gain access to and/or utilize a Platform to generate and send content of any kind, including, but not limited to, unsolicited commercial messages. For purposes of this Section, “commercially reasonable efforts” include, by way of example and not limitation, the prompt removal by Supplier of any content it learns violates this Section, with written notice to Verizon of such removal(s). 22. USE OF TRADEMARKS 22.1 Grant to Verizon: Supplier hereby grants Verizon a non-exclusive, limited- term, non-transferable, revocable right and license to use, reproduce, publish, perform and display the Supplier Trademarks in connection with the development, use, reproduction in promotional and marketing materials, and electronic and printed advertising, publicity, newsletters and mailings about the Data Services. Verizon hereby acknowledges Supplier's exclusive ownership of and title to the Supplier Trademarks and the goodwill attaching thereto. Verizon agrees that the use of Supplier Trademarks will conform with usage guidelines that Supplier provides in writing to Verizon from time to time. 22.2 Grant to Supplier. 22.2.1 License. 22.2.1.1 Subject to the terms and conditions of this Agreement, Verizon hereby grants to Supplier a limited, nonexclusive, nontransferable, royalty-free right and license to use the Verizon Marks solely in connection with connection with providing the Services. 22.2.1.2 Except as provided in 22.2.1.1 above, Supplier shall not use, nor permit any other person or entity to use, the Verizon Marks in any manner, including, without limitation, as part of a corporate name, trademark, service ▇▇▇▇, domain name, trade dress or logo. 22.2.1.3 Supplier shall have no right to grant sublicenses of the Verizon Marks. 22.2.2 Quality Standards. 38 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential
22.2.2.1 Supplier agrees that the nature and quality of all use by Supplier of the Verizon Marks shall conform to such reasonable guidelines and standards as are provided in writing from time to time by Verizon. 22.2.2.2 Supplier shall submit to Verizon for review and approval, at least **** prior to proposed use, all materials, in which the Verizon Marks are used. Subsequent changes to previously submitted materials still in the approval process will be approved within ****. Supplier hall not publish, distribute or use any such materials, in which the Verizon Marks are used without the prior written approval of the following representative of Verizon: ****, email ****. 22.2.2.3 Notwithstanding the foregoing, Supplier may designate at the time of submission that the requested approval is for multiple/repetitive, identical uses on the same medium. Supplier may request approval for such multiple/repetitive, identical use for a period not to exceed the end of the term of this Agreement. 22.2.2.4 Verizon reserves the right, in its sole discretion and without cause, to refuse to approve any proposed Supplier use of the Verizon Marks. 22.2.2.5 Ownership and Goodwill. Supplier acknowledges that, as between Verizon and Supplier, Verizon’s affiliate Verizon Trademark Services LLC (“VTS”) is the sole and exclusive owner of rights in the Verizon Marks, and Supplier undertakes not to challenge the validity of the Verizon Marks or VTS’s registration and ownership of the Verizon Marks, and agrees that it will do nothing inconsistent with such ownership. Supplier further acknowledges and agrees that all use of the Verizon Marks by Supplier and all goodwill generated by and developed therefrom shall inure to the benefit of and be on behalf of VTS. Supplier agrees that nothing in this Agreement shall give Supplier any right, title or interest in or to the Verizon Marks other than the right to use the Verizon Marks in connection with the Licensed Use in the manner contemplated by this Agreement and only for so long as this Agreement is in force. 23. PUBLICITY AND DISCLOSURE Each party agrees not to provide copies of this Agreement, or otherwise disclose the terms of this Agreement, to any third party without the prior written consent of the other party, except as required by law. Except as required by law, each party further agrees to submit to the contacts below, for written approval, all advertising, sales promotion, press releases and other publicity matters relating to the product furnished and/or the Service performed pursuant to this Agreement, when a name or ▇▇▇▇ or the name or ▇▇▇▇ of the other party or any of its partners or Affiliates is mentioned or language from which the connection of 39 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential ****CERTAIN INFORMATION HAS BEEN OMITTED AND FILED SEPARATELY WITH THE COMMISSION. CONFIDENTIAL TREATMENT HAS BEEN REQUESTED WITH RESPECT TO THE OMITTED PORTIONS

said name or ▇▇▇▇ ▇▇▇ be inferred or implied. Such requests shall be sent to each of the following: If to Verizon: If related to Verizon Wireless products or services, to Vice President -- Corporate Communications Verizon Wireless ▇▇▇ ▇▇▇▇▇▇▇ ▇▇▇ ▇▇▇▇▇▇▇▇ ▇▇▇▇▇▇▇ ▇▇▇▇▇, ▇▇▇ ▇▇▇▇▇▇ ▇▇▇▇▇ If related to Verizon Wireline products or services, to Vice President -- Media Relations Verizon Telecom ▇▇▇ ▇▇▇▇▇▇▇ ▇▇▇ ▇▇▇▇▇▇▇▇ ▇▇▇▇▇▇▇ ▇▇▇▇▇, ▇▇ ▇▇▇▇▇ If related to Verizon Business products or services, to Vice President -- Media Relations Verizon Business ▇▇▇ ▇▇▇▇▇▇▇ ▇▇▇ ▇▇▇▇▇▇▇▇ ▇▇▇▇▇▇▇ ▇▇▇▇▇, ▇▇ ▇▇▇▇▇ If to Supplier: Synchronoss Technologies, Inc. ▇▇▇ ▇▇▇▇▇▇▇▇ ▇▇▇▇▇▇▇▇▇ ▇▇▇▇▇▇▇▇▇▇▇, ▇▇ ▇▇▇▇▇ Attention: President With a copy to Supplier’s General Counsel at the same address. 24. COMPLIANCE WITH LAWS 24.1 Supplier represents and warrants (i) that it and, to the best of its knowledge, its directors, shareholders, officers, employees, agents and all permitted subcontractors are currently in compliance and (ii) that it and its directors, shareholders, officers, employees, agents and all permitted subcontractors will remain in compliance with, the provisions of all applicable federal, state and local laws, including rules, regulations and orders decree or direction of the U.S. or applicable foreign jurisdictions (collectively “laws”) in performance of this Agreement, , including but not limited to any laws pertaining: 24.1.1 to the employment of labor, hours of labor, health and safety, payment of wages, payment of taxes, employment eligibility status and verification (I- 9); in this regard, Supplier shall not discriminate against any employee or 40 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential

applicant for employment because of race, color, religion, disability, sex, national origin, age, physical or mental disability, veteran status or other unlawful criterion, and it shall comply with all applicable laws against discrimination. (If applicable, the Equal Opportunity Clauses set forth in 41 C.F.R. §§60-1.4(a), 60-250.5(a), and 60-741.5(a) are incorporated by reference herein.); 24.1.2 to the safeguarding, protection, privacy, security, encryption, unauthorized disclosure, breach notification and disposal of personal or similar information used, maintained, and/or accessed on Verizon’s behalf including, without limitation, the Standards for Protection of Personal information of the Residents of the Commonwealth of Massachusetts 201 CMR17:00; California Civil Code §1798.82 and the Fair and Accurate Credit Transactions Act of 2003, Public Law 108-159; 24.1.3 to directly or indirectly, making, offering, causing to be made, accepting, requesting, suggesting, directing or otherwise inducing any bribe, payment, loan, commission, hospitality, gift of money, kick-back, inducement or anything of value or other advantage (individually or collectively “Bribery”) to any official, employee, agent or instrumentality of any government, including legislative, administrative or judicial positions, or any public international organization or any other person, company or legal entity to gain any advantage for Verizon or Supplier, or which is in violation of any economic or trade sanctions, in connection with any transaction relating to this Agreement that could result in a violation of any laws relating to Bribery, including without limitation the Foreign Corrupt Practices Act and the U.K. ▇▇▇▇▇▇▇ ▇▇▇ ▇▇▇▇ (“U.K. Bribery”). Notwithstanding any other provisions in this Agreement, Verizon may suspend performance or terminate this Agreement immediately upon written notice, if Supplier breaches any of the terms set forth in sections above. Following notice of termination, Verizon shall not be responsible for any payments due under the Agreement, and shall not be required to complete any order or take any other action pursuant to this Agreement, if it has reasonable basis to believe that such payment, completion of order, or other action would violate any applicable law, including but not limited to the Foreign Corrupt Practices Act, or the UK Bribery. In the event of an unauthorized disclosure of personal or similar information or any other violation of the foregoing pertaining to Verizon, Supplier shall provide notice of same by e-mail to ▇▇▇▇▇▇▇▇.▇▇▇▇▇▇@▇▇▇▇▇▇▇.▇▇▇ within forty-eight (48) hours, and to the notice addressee set forth in the Notices section of this Agreement by the means set forth therein. Supplier shall also procure any required permits or certificates necessary to perform its obligations under this Agreement. 24.2 Software furnished shall comply, to the extent applicable, with the requirements of the Federal Communications Commission’s Rules and Regulations, as may be amended, including those sections concerning the labeling of such Software and the suppression of radiation to specified levels to the extent applicable. If the Software generates interference harmful to radio communications, and such Software was installed in accordance with such Rules and Regulations, then 41 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential

Supplier shall provide to Verizon methods for suppressing the interference. If the interference cannot be reasonably suppressed, Supplier shall accept return of the Software, refund to Verizon the price paid for the Software and bear all expenses for removal and shipment of such Software. Nothing herein shall be deemed to diminish or otherwise limit Supplier’s obligations under Section 31, Indemnification or any other rights or remedies available to Verizon, whether at law or in equity. 24.3 Supplier represents and warrants to Verizon that at the time of delivery, the Platform delivered, or Software delivered, hereunder shall be “CALEA Compliant”, meaning that they will comply with the provisions of the Communications Assistance for Law Enforcement Act (Pub L. 103-414, Title 1, October 25, 1994, 108 Stat 4279, as amended), as well as any regulations implementing the provisions of the law. . 24.4 Notwithstanding Section 24.1, it shall not be considered a material breach of this Agreement if a Party is not in compliance with an Applicable Law if such non- compliance is not material to a Party’s performance under this Agreement. 25. FORCE MAJEURE Neither Party shall be responsible for any delay or failure in performance of any part of this Agreement to the extent that such delay is caused by reason of acts of God, wars, revolution, civil commotion, acts of public enemy, embargo, acts of government in its sovereign capacity, or any other circumstances beyond the reasonable control and to the extent not involving any fault or negligence of the Delayed Party ("Condition"). If any such Condition occurs, the Party delayed or unable to perform ("Delayed Party"), upon giving prompt notice to the other Party, shall be excused from such performance on a day-to-day basis during the continuance of the impacts of such Condition (and the other Party shall likewise be excused from performance of its obligations on a day-to-day basis during the same period); provided, however, that the Party so affected shall use its best reasonable efforts to avoid or remove such Condition, and both Parties shall proceed immediately with the performance of their obligations under this Agreement whenever such causes are removed or cease. Labor difficulties, including without limitation, strikes, slowdowns, work stoppage, picketing or boycotts, shall not constitute a Condition that excuses a party from performance of its obligations under this Agreement. In the event of such labor difficulties affecting a party, the other party shall use all lawful means to perform Services or meet obligations agreed to under this Agreement. If the Condition continues for more than ****, then the Party affected may terminate this Agreement or any Authorization Letter. 26. ASSIGNMENT The rights, obligations, and other interests of Supplier shall not be assigned by Supplier, in whole or in part, without the prior written consent of Verizon and any purported assignment of same shall be void and ineffective; provided, however, no consent shall be required in the event of the sale of all of the capital stock or 42 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential ****CERTAIN INFORMATION HAS BEEN OMITTED AND FILED SEPARATELY WITH THE COMMISSION. CONFIDENTIAL TREATMENT HAS BEEN REQUESTED WITH RESPECT TO THE OMITTED PORTIONS

substantially all of the assets to another party. provided, that such acquiring third party: (a) agrees to be bound by all of the terms and conditions of this Agreement, and (b) meets none of the following criteria: i. Such acquiring third party is a competitor of Verizon or is owned by a competitor of Verizon; ii. Such acquiring third party does not have substantially equal or greater financial wherewithal as compared to Supplier; or iii. Verizon has been in litigation with such entity in the past over one or more of the following topics: Intellectual Property Rights, confidential information, data protection, or a material breach of a services agreement. 26.1 If Verizon sells, exchanges or otherwise disposes of all or a portion of the assets of, or Verizon’s interest in, any business unit in which Services are used, then Verizon shall have the right to assign to such third party all applicable licenses, warranties, maintenance schedules and rights granted under this Agreement with respect to such Service; provided that the third party agrees to be bound by all obligations of Verizon to Supplier that pertain to the Service. Notwithstanding the foregoing, Verizon shall have the right to assign this Agreement to any Affiliate.]] 27. SUBCONTRACTING Supplier shall not use subcontractors to perform the Services under this Agreement except by prior written consent of Verizon. Requests by Supplier to Verizon to use subcontractors shall be in writing and shall specify the Services to be subcontracted and the identity of the proposed subcontractors. It shall be Supplier’s responsibility to update Verizon as it adds or deletes subcontractors and to ensure that the subcontractors it uses are in all cases approved by Verizon. Supplier accepts full responsibility for the acts and omissions of subcontractors and of persons either directly or indirectly employed by them in connection with performing Services hereunder to the same extent as Supplier is responsible for the acts and omissions of persons directly employed by Supplier. In the event Verizon approves the use of a Subcontractor, for all subcontractors, including, without limitation, any application provider or Content provider, that directly or indirectly furnish hardware, facilities, software, data files, or services that are elements of, or support, the Hosted Services (“Third Party Providers”), Supplier shall contract with such Third Party Providers (other than Terremark or any other affiliate of Verizon) on terms and conditions that are the same as, or no less stringent and beneficial to Verizon than the terms and conditions of Sections 5, 19, 20, 21, 24.1.2 (if the Subcontractor will have access to Massachusetts customer information described in such Section) and 26 and the applicable SLA; and further as and for an inducement to Verizon to enter into this Agreement, Supplier shall make Verizon a third party beneficiary in all respects under such contracts between or among Supplier and such Third Party Providers in order to 43 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential
pass through to Verizon all rights and remedies against such Third Party Providers as may be beneficial to Verizon. Verizon’s rights and remedies under all such Third Party Provider contracts shall be supplemental to its rights and remedies against Supplier. 28. TAXES 28.1 Verizon shall, as required by law, pay all state and local sales and use tax or other similar tax (each, a "Tax"), which is directly and solely attributable to purchases by Verizon from Supplier for consideration under this Agreement. Supplier shall ▇▇▇▇ such Tax to Verizon in the amount required by law, separately stating the amount and type of the billed Tax on the applicable invoice; Verizon shall pay such billed amount of Tax to Supplier; and Supplier shall remit such billed amount of Tax to the appropriate tax authorities as required by law; provided, however, that Supplier shall not ▇▇▇▇ to or otherwise attempt to collect from Verizon any Tax with respect to which Verizon provides Supplier with (i) an exemption certificate prepared in accordance with applicable law, (ii) a direct pay number, or (iii) other evidence, reasonably acceptable to Supplier, that such Tax does not apply. Except as provided in this Section 28.1, Supplier shall bear the costs of all import and export duties and other governmental fees of whatever nature (other than taxes) with respect to all Software and Services supplied under this Agreement. For the avoidance of doubt, Supplier shall be solely responsible for any taxes, tax-like charges or tax-related or other surcharges determined by Supplier's income, net worth, franchise or property. Supplier will bear any and all financial responsibility for interest, and penalties resulting from its failure to comply with applicable law. 28.2 Supplier shall be responsible for any sales, use, excise, value added, service, consumption, property, franchise, income, or other taxes and duties based upon or measured by Supplier’s cost in acquiring goods or services furnished or used by Supplier in the Software and services supplied under this Agreement. 28.3 Supplier shall reasonably cooperate with Verizon so as to minimize the tax liability of Verizon, including, without limiting the generality of the foregoing, liability for Tax to be billed and collected under Section 28.1. Such cooperation shall include, without limiting the generality of the foregoing: (i) the delivery of Software and Documentation from Supplier to Verizon via electronic transmission; (ii) the separate statement of Tax charges on all invoices (including, without limiting the generality of the foregoing, charges for installation, assembly, configuration, freight, insurance and shipping); (iii) the maintenance and invoicing of separate prices for Software and Services; (iv) providing Verizon, upon request, with a written opinion as to (a) the percentage of the value of the Software or Services supplied under this Agreement, (b) the percentage breakdown of value among such categories of Software as Verizon may identify in its request, and (c) such supporting documentation and information with respect to such opinion as Verizon may request; and (v) upon request from Verizon, certifying in writing whether and, if applicable, to what extent, any particular Software is custom or pre-written. 28.4 Supplier shall cooperate with all reasonable requests of Verizon in connection with any contest or refund claim with respect to taxes. If applicable law places 44 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential

the responsibility on Supplier to collect a Tax from Verizon and Supplier fails to do so, Verizon will not be responsible for any interest or penalties associated with Supplier’s failure to invoice such Tax solely due to its error. If Supplier incorrectly (in the reasonable opinion of Verizon) bills and collects Tax from Verizon and the taxing authority requires that any refund from the taxing authority be sought by the billing party, then, upon request from Verizon (together with reasonable supporting documentation), Supplier shall seek the refund and remit to Verizon the amount of the refund actually obtained, together with interest, if any, actually received, promptly upon receiving such refund and interest, if any, from the taxing authority. If the Supplier agrees with a tax authority to waive the Supplier’s statute of limitations as to its audit period, Verizon will not be responsible for any portion of tax audit assessments on Supplier beyond Supplier’s original applicable statute of limitations, nor, will Verizon be responsible for any portion of tax audit assessments on Supplier for any period for which Verizon’s statute of limitations is closed due to expiration or audit settlement. 28.5 If any payment to be made in respect of any invoice is subject, under the law of any foreign tax jurisdiction, to any withholding tax, notwithstanding any provision of this Agreement to the contrary, Verizon shall make payment to Supplier of the amount owing on the invoice, less a deduction for the withholding tax, and shall account to the relevant tax authority for the withheld tax. Payments of the net sum to Supplier and the withholding tax to the relevant tax authority shall constitute, for purposes of this Agreement, full settlement of the amount owing under the invoice. Verizon will, upon written request from Supplier and at Supplier’s expense, furnish any necessary evidence that may reasonably be required to establish the payment of the withholding tax to the relevant tax authority. 29. PERMITS Unless otherwise specifically provided for in this Agreement, Supplier (including any employees, agents and contractors) shall obtain and keep in full force and effect, at its expense, any permits, licenses, consents, approvals and authorizations (“Permits”) necessary for the performance of Services. Upon request, Supplier must submit to Verizon evidence of any Permits required for Supplier to perform Services in a given location. 30. WORK RULES AND ACCESS REQUIREMENTS 30.1 Supplier shall comply with Verizon security rules to the extent provided to Supplier or with respect to which Supplier has actual or reasonable constructive notice as well as all governmental security regulations including, but not limited to U.S. governmental regulations governing security clearances. 30.2 Supplier shall permit reasonable access to employees or subcontractors (for purposes of this Section, Verizon shall be responsible for such Verizon subcontractors as if they were Verizon employees) of Verizon during normal working hours to its facilities to the extent reasonably required in connection with the Service. 45 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential

30.3 Supplier shall provide its employees, subcontractors, and agents and work vehicles with identification in accordance with current generally applicable Verizon supplier requirements 30.4 If Supplier is given access, whether on-site or through remote facilities, to any Verizon computer or electronic data storage system in order for Supplier to accomplish the Services called for in this Agreement, Supplier shall limit such access and use solely to perform Services within the scope of this Agreement, shall not without the prior written authorization of Verizon export or transmit any computer system, electronic file, software or other electronic services, or data therein contained, to entities or locations other than those specified in this Agreement and shall not access or attempt to access any computer system, electronic file, software or other electronic services other than those specifically required to accomplish the work required under this Agreement and only as permitted in this Agreement. Supplier shall limit such access to those of its employees who are qualified and required, subject to Verizon requiring written authorization, to have such access in connection with this Agreement, and shall strictly follow all Verizon’s security rules for use of Verizon’s electronic resources. All user identification numbers and passwords disclosed to Supplier and any information obtained by Supplier as a result of Supplier’s access to and use of Verizon’s computer and electronic data storage systems shall be deemed to be, and shall be treated as, Verizon Confidential Information under applicable provisions of this Agreement. Verizon reserves the right to monitor such actions by Supplier and Supplier agrees to cooperate with Verizon in the investigation of any apparent unauthorized access by Supplier to Verizon’s computer or electronic data storage systems or unauthorized release of Confidential Information by Supplier. 30.5 If Supplier is given such access to any Verizon computer or electronic storage system, or if Supplier otherwise exchanges electronic messages or communications with Verizon (including but not limited to Verizon accessing any of Supplier’s data bases or systems on-site or remotely), or if Supplier furnishes software or other electronic transmissions to Verizon, (i) Supplier shall not transmit or introduce any virus, worm or other malicious code to Verizon or into its network, computers, electronic storage systems or other systems (the foregoing shall not apply where Subscriber Data as transmitted by Verizon to Supplier contains such a virus, worm or other malicious code) and (ii) any Software provided to Verizon by Supplier for use by Supplier or Verizon shall (a) contain no hidden files; (b) not replicate, transmit, or activate itself without control of a person operating computing equipment on which it resides; (c) not alter, damage, or erase any data or computer programs without control of a person operating the computing equipment on which it resides unless such practice is consistent with Specifications or Service Requirements; (d) contain no encrypted imbedded key unknown to Verizon, node lock, time-out or other function, whether implemented by electronic, mechanical or other means, which restricts or may restrict use or access to any programs or data developed under this Agreement, based on residency on a specific hardware configuration, frequency of duration of use, or other limiting criteria (“Illicit Code”) unless such practice is consistent with Specifications or Service Requirements. 46 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential

30.6 Verizon reserves the right to reasonably request at any time and for any reason that specific employees, subcontractors, and agents of Supplier be removed from and not assigned by Supplier to perform Services for Verizon, and Supplier acknowledges, agrees and understands that Supplier will immediately comply with such request by Verizon. 30.7 Background Checks. 30.7.1 For each of the employees that Supplier wishes to assign to perform Services for Verizon, Supplier shall certify to Verizon that it has conducted (or caused to be conducted) a background check as described herein (collectively referred to as “background checking”) to the extent permitted by applicable law. For purposes of this Section, “employee” shall include Supplier’s employees and any of Supplier’s contract personnel; and “assign” shall include training for Services to be provided to Verizon, unless otherwise agreed to by Verizon. 30.7.1.1 Where permitted by law, the criminal history check shall consist of a federal and state check for felony criminal convictions (or the equivalent thereof under relevant law) in all locations where the assigned employee has resided, has been employed, or has attended school in the immediately preceding seven (7) years, and a check of U.S. Government Specially Designated National (OFAC) and export denial lists. This criminal history check shall include, to the extent available and permitted by law, a check for outstanding warrants and a check for pending felony charges in all such locations. Statewide county searches shall be performed in all states where such search mechanism is available without requiring specialized data (such as fingerprints or DNA), and the National Criminal File database shall also be searched. 30.7.1.2 The employee will be checked against the National/State Sex Offender Registry (▇▇▇▇://▇▇▇.▇▇▇▇▇▇▇▇▇▇▇▇▇▇.▇▇/ with no state selected) or the equivalent, to yield a national and all-states search. 30.7.1.3 The name to which employee’s Social Security Number is attributed shall be verified. 30.7.1.4 The employee’s citizenship, most recent country of permanent residence, and legal right to work in the jurisdiction in which the employee will be performing Services for Verizon shall be verified. 30.7.2 For any period of time encompassed in the foregoing background check requirement when the employee was resident outside of the United States, such background checking shall be conducted by a reputable investigative agency that conducts background checking in the relevant country(ies) for transnational technology firms comparable to Verizon, utilizing database checking, field checking and interviews as needed to 47 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential

the extent permitted by applicable law. The criminal convictions check shall include the equivalent, under relevant non-US law, of those convictions described in 30.7.1 to the extent permitted by applicable law 30.7.3 Supplier shall comply with all applicable laws in conducting the background check specified in this Section 30.7 including but not limited to, where required, securing from each employee who provides Services to Verizon such employee’s written consent to perform the background checking specified in this Section 30.7 and to disclose the results thereof to Verizon upon Verizon’s request to the extent permitted by applicable law. Without limitation of the foregoing, Supplier will make all written disclosures to and obtain written consent from each employee to obtain consumer reports as defined in and required by the Fair Credit Reporting Act to the extent permitted by applicable law. Supplier shall provide such results and written consent to Verizon upon request from Verizon. Supplier may be required to recertify on an annual basis that such Background Checks were performed for any employee who has performed Services and was not included in the prior certification. 30.7.4 Without prior review with and consent of Verizon, Supplier shall not assign any employee to provide Services to Verizon if such employee: 30.7.4.1 has been convicted of a felony (or the equivalent thereof under relevant law) within the last seven (7) years which, following a review under applicable law and applying the guidelines set forth in Exhibit G, Supplier concludes the circumstances of which are directly job-related to the assignment at Verizon and therefore makes the employee unsuitable for that assignment at Verizon, or for whom a warrant is outstanding, or for whom a felony charge is currently pending, or is on a U.S. Government Specially Designated National or export denial list. The foregoing shall not apply to a minor traffic violation (a moving traffic violation other than reckless driving, hit and run, driving to endanger, vehicular homicide, driving while intoxicated or other criminal offense involving gross negligence, recklessness, intentional or willful misconduct while operating a motor vehicle), to a conviction that has been legally expunged, or to a conviction for a misdemeanor that occurred while the employee was under the age of twenty-one years; or 30.7.4.2 is on the national or any state Sex Offender Registry which, following a review under applicable law and applying the guidelines set forth in Exhibit G, Supplier concludes the circumstances of which are directly job-related to the assignment at Verizon and therefore makes the employee unsuitable for that assignment at Verizon 30.7.4.3 does not have the legal right to work in the jurisdiction in which the employee will be performing Services for Verizon. 48 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential

30.7.5 Supplier shall certify to Verizon that Supplier has caused the foregoing background checking to be performed for each employee assigned to provide Service for Verizon within **** of the Effective Date; further, upon request, Supplier shall annually certify no later than the anniversary of the Effective Date that it has met the foregoing background checking requirements for all employees then assigned to provide Service for Verizon. Such certifications shall be sent via electronic mail to Verizon’s in accordance with the Notice provision in the Agreement. 31.8 Supplier agrees to comply with Verizon's Supplier Code of Conduct located at ▇▇▇▇://▇▇▇▇▇.▇▇▇▇▇▇▇.▇▇▇/▇▇▇▇▇▇, which may be updated from time to time to the extent Verizon notifies Supplier in writing of such update. 31. INDEMNIFICATION 31.1 Supplier shall defend, indemnify and hold harmless Verizon, its parents, subsidiaries and Affiliates, and its and their respective directors, officers, partners, members, employees, agents, successors and assigns (“Indemnified Parties”) from and against any claims, demands, lawsuits, damages, liabilities, loss, costs or expenses (including, but not limited to, reasonable fees and disbursements of counsel and court costs), judgments, settlements and penalties of every kind (“Claims”), that may be made: (a) by anyone for injuries (including death) to persons or damage to tangible property, including theft, resulting in whole or in part from the acts or omissions of Supplier or those persons furnished by Supplier, including its subcontractors (if any); (b) by persons furnished by Supplier and its subcontractors (if any) under Worker's Compensation or similar acts; (c) by anyone in connection with or based upon Services or Software (including products furnished hereunder) provided by Supplier and its subcontractors, if any, or contemplated by this Agreement, including Claims regarding the adequacy of any disclosures, instructions or warnings related to any such Services; (d) under any federal securities laws or under any other statute, at common law or otherwise arising out of or in connection with the performance by Supplier contemplated by this Agreement or any information obtained in connection with such performance and (e) for any breach by Supplier of Section 15.9.1. The foregoing indemnification shall apply whether Supplier or an Indemnified Party defends such Claim and whether the Claim arises or is alleged to arise out of the sole acts or omissions of the Supplier (and/or any subcontractor of Supplier) or out of the concurrent acts or omissions of Supplier (and/or any subcontractor of Supplier) and any Indemnified Parties. Supplier further agrees to bind its subcontractors, if any, to similarly indemnify, hold harmless, and defend the Indemnified Parties. 31.2 Verizon will provide Supplier with prompt, written notice of any written Claim covered by this indemnification and will cooperate appropriately with Supplier in connection with Supplier’s evaluation of such Claim. Promptly after receipt of such request, Supplier shall assume the sole control and defense of such Claim. Supplier shall not settle or compromise any such Claim or consent to the entry of any judgment without the prior written consent of each Indemnified Party and without an unconditional release of all claims by each claimant or plaintiff in favor of each Indemnified Party. 49 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential ****CERTAIN INFORMATION HAS BEEN OMITTED AND FILED SEPARATELY WITH THE COMMISSION. CONFIDENTIAL TREATMENT HAS BEEN REQUESTED WITH RESPECT TO THE OMITTED PORTIONS

32. INSURANCE 32.1 Supplier shall secure and maintain at its expense during the term of this Agreement: 32.1.1 Commercial General Liability insurance (including, but not limited to, premises-operations, products/completed operations, contractual liability, independent contractors, personal and advertising injury) with limits of at least $****, combined single limit for each occurrence and $**** general aggregate. 32.1.2 Commercial Automobile Liability insurance with limits of at least $**** combined single limit for each accident covering all owned, non-owned hired and leased vehicles. 32.1.3 Workers' Compensation insurance, in compliance with the statutory requirements of the state(s) of operation and Employer's Liability insurance with limits of not less than $**** each accident/disease/policy limit. 32.1.4 A combination of primary and excess/umbrella liability policies will be acceptable as a means to meet the limits specifically required hereunder. THE REQUIRED MINIMUM LIMITS OF COVERAGE SHOWN ABOVE, HOWEVER, WILL NOT IN ANY WAY RESTRICT OR DIMINISH SUPPLIER’S LIABILITY UNDER THIS AGREEMENT. 32.1.5 Professional Liability/Errors and Omissions insurance, with limits of not less than $**** each claim. 32.2 Supplier represents and warrants that it will obtain upon or prior to the effective date of the agreement a policy or policies of insurance from an insurer(s) that (i) is licensed, authorized or permitted to do business in the state(s) where service is to be provided, and (ii) has a Best’s Rating “A- VII” or better. Supplier shall deliver a Certificate of Insurance on which Verizon Communications Inc., its subsidiaries and Affiliates are named as additional insureds and listed as a Certificate Holder to the following address: **** Verizon Sourcing LLC One Verizon Way Mailcode **** Basking Ridge, NJ USA 07920 or via Verizon’s vSource supplier portal. Supplier’s insurer or its authorized representative shall provide no less than **** prior written notice of intent to non- renew, cancellation or material adverse change, except **** notice for nonpayment of premium shall apply. 32.3 Supplier shall waive its rights of subrogation against Verizon for all claims, as permitted by law. 50 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential ****CERTAIN INFORMATION HAS BEEN OMITTED AND FILED SEPARATELY WITH THE COMMISSION. CONFIDENTIAL TREATMENT HAS BEEN REQUESTED WITH RESPECT TO THE OMITTED PORTIONS

32.4 Supplier agrees that Supplier's policy is primary and non-contributory with any insurance or program of self-insurance that may be maintained by Verizon. 32.5 Supplier is responsible for determining whether the above minimum insurance coverages are adequate to protect its interests. The above minimum coverages do not constitute limitations upon Supplier’s liability. 32.6 Self-Insure. Should Supplier elect to self-insure any portion of the insurance required to be maintained, Supplier shall maintain a senior unsecured credit rating from Standard & Poor’s, ▇▇▇▇▇’▇ of at least BBB- or Baa2 or commensurate rating respectively. If Supplier’s senior unsecured credit rating falls below either of these thresholds during the term of this Agreement, Supplier will procure insurance for the risks it is self-insuring as soon as possible but no later than **** from the date of such event. If Supplier does not have a senior unsecured credit rating described above, a minimum net worth of $**** will be required to self-insure and shall be maintained throughout the term of this Agreement. If Supplier’s net worth falls below $****during the term of this Agreement Supplier will procure and maintain insurance for the risk it is self- insuring as soon as possible. 33. RELATIONSHIP OF PARTIES In providing any Services or Software under this Agreement, Supplier is acting solely as an independent contractor and not as an agent of any other Party. Persons furnished by the Supplier shall be solely the employees or agents of the Supplier and shall be under the sole and exclusive direction and control of such Party. They shall not be considered employees of Verizon for any purpose. Supplier shall be responsible for compliance with all laws, rules and regulations involving its respective employees or agents, including (but not limited to) employment of labor, hours of labor, health and safety, working conditions and payment of wages. Supplier shall also be responsible, respectively, for payment of taxes, including federal, state, and municipal taxes, chargeable or assessed with respect to its employees or agents, such as social security, unemployment, worker's compensation, disability insurance and federal and state income tax withholding. Neither Party undertakes by this Agreement or otherwise to perform or discharge any liability or obligation of the other Party, whether regulatory or contractual, or to assume any responsibility whatsoever for the conduct of the business or operations of the other Party. Nothing contained in this Agreement is intended to give rise to a partnership or joint venture between the Parties or to impose upon the Parties any of the duties or responsibilities of partners or joint venturers. 34. NOTICES With the exception of invoices pursuant to Section 11 (Fees/Payment); requests for publicity consent under Section 23 (Publicity and Disclosure), and MWDBVE matters under Exhibit E (Primary Supplier Commitment), Notices concerning this Agreement shall be in writing and shall be given or made by means of telegram, facsimile transmission, certified or registered mail, express mail or other 51 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential ****CERTAIN INFORMATION HAS BEEN OMITTED AND FILED SEPARATELY WITH THE COMMISSION. CONFIDENTIAL TREATMENT HAS BEEN REQUESTED WITH RESPECT TO THE OMITTED PORTIONS
overnight delivery service, or hand delivery, proper postage or other charges paid and addressed or directed to the respective Parties as follows. A notice that is sent by facsimile shall also be sent by one of the other means set out by this Section: To Supplier: Synchronoss Technologies, Inc. ▇▇▇ ▇▇▇▇▇▇▇▇ ▇▇▇▇. ▇▇▇▇▇▇▇▇▇▇▇, ▇▇ ▇▇▇▇▇ Attention: President Fax: **** With a copy to: Synchronoss Technologies, Inc. ▇▇▇ ▇▇▇▇▇▇▇▇ ▇▇▇▇. ▇▇▇▇▇▇▇▇▇▇▇, ▇▇ ▇▇▇▇▇ Attention: General Counsel Fax: **** To Verizon: Verizon ▇▇▇ ▇▇▇▇▇▇▇ ▇▇▇ ▇▇▇▇▇▇▇ ▇▇▇▇▇, ▇▇ ▇▇▇ ▇▇▇▇▇ Attention: **** With a copy to: Verizon Sourcing LLC ▇▇▇ ▇▇▇▇▇▇▇ ▇▇▇ ▇▇▇▇▇▇▇ ▇▇▇▇▇, ▇▇▇ ▇▇▇▇▇▇ ▇▇▇▇▇ Attention: Vice President and Deputy General Counsel - Sourcing Fax: **** Notices for change in ownership, change in name of firm, or change in mailing address must be given by each party by mailing to the other party within **** of such change. Notices for change in ownership must include the names of all new owners or officers, registered agent for service of process and state of incorporation or organization. 35. NONWAIVER Either party’s failure to enforce any of the provisions of this Agreement or any Authorization Letter, or to exercise any option, shall not be construed as a waiver of such provisions, rights, or options, or affect the validity of this Agreement. 36. SEVERABILITY If any provision of this Agreement shall be invalid or unenforceable, then such invalidity or unenforceability shall not invalidate or render unenforceable the entire Agreement. The entire Agreement shall be construed as if not containing the particular invalid or unenforceable provision or provisions, and the rights and obligations of the Parties shall be construed and enforced accordingly. 52 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential ****CERTAIN INFORMATION HAS BEEN OMITTED AND FILED SEPARATELY WITH THE COMMISSION. CONFIDENTIAL TREATMENT HAS BEEN REQUESTED WITH RESPECT TO THE OMITTED PORTIONS
37. LIMITATION OF LIABILITY EXCEPT FOR CLAIMS UNDER SECTION 19 (CONFIDENTIAL INFORMATION), IN NO EVENT SHALL EITHER PARTY BE LIABLE TO THE OTHER PARTY, ITS EMPLOYEES, SUBCONTRACTORS, AND/OR AGENTS, OR ANY THIRD PARTY, FOR ANY INDIRECT, INCIDENTAL, SPECIAL, CONSEQUENTIAL, PUNITIVE DAMAGES, OR LOST PROFITS FOR ANY CLAIM OR DEMAND OF ANY NATURE OR KIND, ARISING OUT OF OR IN CONNECTION WITH THIS AGREEMENT OR THE PERFORMANCE OR BREACH THEREOF. THE AGGREGATE LIABILITY OF EITHER PARTY FOR ALL CLAIMS MADE IN ANY CALENDAR YEAR UNDER OR IN CONNECTION WITH THIS AGREEMENT, IRRESPECTIVE OF THE BASIS OF CLAIM (WHETHER WARRANTY, TORT (INCLUDING NEGLIGENCE) OR OTHERWISE) SHALL BE LIMTED TO ****. ****. The Parties acknowledge that the fees paid hereunder reflect the foregoing allocation of risk. 38. DISPUTE RESOLUTION 38.1 The Parties desire to resolve certain disputes, controversies and claims arising out of this Agreement without litigation. Accordingly, except in the case of a suit, action or proceeding to compel either Party to comply with the dispute resolution procedures set forth in this Section the Parties agree to use the following alternative procedure with respect to any dispute, controversy or claim arising out of or relating to this Agreement or its breach. The term "Dispute" means any dispute, controversy or claim to be resolved in accordance with the dispute resolution procedure specified in this Section. 38.2 At the written request of a Party, each Party shall appoint a knowledgeable, responsible representative to meet and negotiate in good faith to resolve any Dispute arising under this Agreement. The Parties intend that these negotiations 53 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential
be conducted by non-lawyer, business representatives. The discussions shall be left to the discretion of the representatives. Upon agreement, the representatives may utilize other alternative dispute resolution procedures such as mediation to assist in the negotiations. Discussions and correspondence among the representatives for purposes of these negotiations shall be treated as confidential information developed for purposes of settlement, shall be exempt from discovery and production, and shall not be admissible in any lawsuit without the concurrence of all Parties. Documents identified in, or provided with, such communications, which are not prepared for purposes of the negotiations are not so exempted and may, if otherwise admissible, be admitted in evidence in the lawsuit. 38.3 If the negotiations do not resolve the Dispute within **** of the initial written request, the Parties may pursue their available remedies at law or in equity. 39. ORDER OF PRECEDENCE All quotations, Authorization Letters, Change Orders, acknowledgments, and invoices issued pursuant to this Agreement shall be subject to the provisions contained in this Agreement. In the event of any conflict between a specific term or condition of this Agreement and a specific term or condition contained in an Authorization Letter or Change Order, the specific term or condition of the Authorization Letter or applicable Change Order shall control and take precedence where the Agreement provides that this Agreement is subject to such Authorization Letter or Change Order or where it is stated in a clear and unambiguous matter in the Authorization Letter or Change Order that the specific term or condition of the Exhibit is in conflict with the Agreement and takes precedence. The terms and conditions of this Agreement and its Exhibits will control over any additional, conflicting or inconsistent terms contained in any Authorization Letter, Change Order, quotation, acknowledgment or invoice, unless agreed in writing by authorized representatives of the Parties; provided that, the following provisions, as they to Services or Software ordered pursuant to a particular Authorization Letter, can be changed by language contained in that Authorization Letter or Change Order: (i) the quantity, (ii) special quoted price, (iii) payment terms, (iv) warranty period, or (v) delivery date. 40. SECTION HEADINGS The headings of the several sections are inserted for convenience of reference only and are not intended to be a part of or to affect the meaning or interpretation of this Agreement. 41. SURVIVAL OF OBLIGATIONS The respective obligations of the Parties under this Agreement that by their nature would continue beyond the termination, cancellation or expiration, shall survive any termination, cancellation or expiration, including, but not limited to, obligations to indemnify, insure and maintain confidentiality. 54 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential ****CERTAIN INFORMATION HAS BEEN OMITTED AND FILED SEPARATELY WITH THE COMMISSION. CONFIDENTIAL TREATMENT HAS BEEN REQUESTED WITH RESPECT TO THE OMITTED PORTIONS

42. CHOICE OF LAW AND JURISDICTION The construction, interpretation and performance of this Agreement shall be governed by and construed in accordance with the laws of the State of New York without regard to any conflicts of law principles that would require the application of the laws of any other jurisdiction and subject to the exclusive jurisdiction of the federal or state courts in New York. The Parties hereby consent to the exclusive jurisdiction of the courts in the State of New York and agree to accept the service of process of such courts such that any suit brought by either Party against the other Party for claims arising out of this Agreement shall be brought in the Supreme Court of the State of New York, New York County, and/or, if applicable, the United States District Court for the Southern District of New York. The application of the United Nations Convention on Contracts for the International Sale of Goods is specifically excluded from this Agreement. 43. GIFTS AND GRATUITIES AND CONFLICTS OF INTEREST 43.1 Supplier certifies that, to the best of Supplier’s knowledge and belief, no economic, beneficial, employment or managerial relationship exists between Supplier and any employee of Verizon, or between Supplier and any relative of an employee of Verizon, that would tend in any way to influence such employee in the performance of his or her duties on behalf of Verizon in connection with the awarding, making, amending or making determinations concerning the performance of this or any other agreement. 43.2 The exchange or offering of any money, gift item, personal service, entertainment or unusual hospitality by Supplier to Verizon is expressly prohibited. This prohibition is equally applicable to both Parties’ officers, employees, agents or immediate family members. Any violation of this provision constitutes a material breach of this Agreement. 55 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential
44. ENTIRE AGREEMENT This Agreement together with its exhibits constitutes the entire agreement between the Parties and cancels all contemporaneous or prior agreements, whether written or oral, with respect to the subject matter of this Agreement. No modifications shall be made to this Agreement unless in writing and signed by authorized representatives of the Parties 45. SIGNATURES IN WITNESS WHEREOF, the Parties hereto have caused this Agreement to be executed by their duly authorized officers or representatives. VERIZON SOURCING LLC SYNCHRONOSS TECHNOLOGIES, INC. By: /s/ ▇▇▇▇ ▇. ▇▇▇▇ By: /s/ ▇▇▇▇▇▇▇ ▇. ▇▇▇▇▇▇ Name: ▇▇▇▇ ▇. ▇▇▇▇ Name: ▇▇▇▇▇▇▇ ▇. ▇▇▇▇▇▇ Title: EVP & CAO Title: CEO Date: 12/20/13 Date: 12/16/13 56 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential
EXHIBIT A – FORM OF AUTHORIZATION LETTER Date Contact Name Supplier Name Address City, State Re: This Application Service Provider Agreement between Verizon and _____________________ (“Supplier”) Verizon Contract No. Authorization Letter Number: Dear __________________: This authorization is pursuant to the terms and conditions of the above-referenced agreement (the “Agreement”). The services to be performed are described in the attached “Statement of Work” (Schedule 1) (“Project”). The schedule of pricing is set forth in the attached Statement of Work. The Verizon Project Leader will be: __________________________________ Invoices shall be billed on a monthly basis and addressed to: Verizon [INSERT APPROPRIATE ADDRESS] ______________________ _______________________ Attn: _________________________ The payment terms shall be as defined in the Agreement. Supplier shall not issue its invoice for the Project until the earlier of Verizon’s written acceptance of the Project or the expiration of the acceptance period set forth in the Statement of Work. The Services will be performed at the Verizon facilities located at ____________. Travel time to and from this location will not be billable. Out-of-pocket expenses, authorized in advance by Verizon, will be billed to Verizon in accordance with the Agreement. The maximum amount authorized under this letter is $___________ (“Amount Authorized”). Services authorized by this letter will commence on _______________ and will continue until _____________, subject to the earlier of 1) completion of the Project; or 2) termination of Services under the Agreement. The Verizon Project Leader will specify standards and/or other constraints to be applied to work being performed. 57 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential
Supplier will provide the Verizon Project Leader with a weekly status report indicating hours worked by day and status of assigned tasks. Please indicate your acceptance of this Authorization Letter by having it signed by an authorized representative of Supplier and return a fully executed original and a copy of your insurance certificate to ________________________ at the address stated above with copies to ______________. Sincerely, (Name) Verizon (Title) Agreed to and accepted by Supplier: BY: ____________________________ NAME: ____________________________ TITLE: ____________________________ DATE: ____________________________ 58 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential

EXHIBIT B – CHANGE REQUEST FORM CHANGE REQUEST FORM CUSTOMER PROVIDED INFORMATION Originator’s Name: Date: Telephone: Email: Customer Name: Application Name: Description of Problem or Desired Changes (Attach Additional sheets as Necessary): Recommended Action/Solution (Attach Additional sheets as Necessary): TO BE COMPLETED BY SUPPLIER Functional Areas Affected: Application Development Production Operations Project Management Office Network Engineering QA Legal Data Base Management Other Content Management Marketing Written description of the work Supplier anticipates performing in order to effectuate such change(s) requested: Schedule for commencing and completing such work: 59 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential
The number of person hours expected to be expended and the costs to Customer associated with such change(s): Analysis/Evaluation/Comments: Reviewed/Verified By: Project Manager _________________________ Date: ________________ Business Unit Manager _________________________ Date: ________________ Other _________________________ Date: ________________ Change Management Team Target Release Date: Recommendation: Work Defer Close Agreed to and accepted by Supplier: Agreed to and accepted by Verizon: BY: ____________________________ BY: ____________________________ NAME: ____________________________ NAME: ____________________________ TITLE: ____________________________ TITLE: ____________________________ DATE: ____________________________ DATE: ____________________________ 60 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential
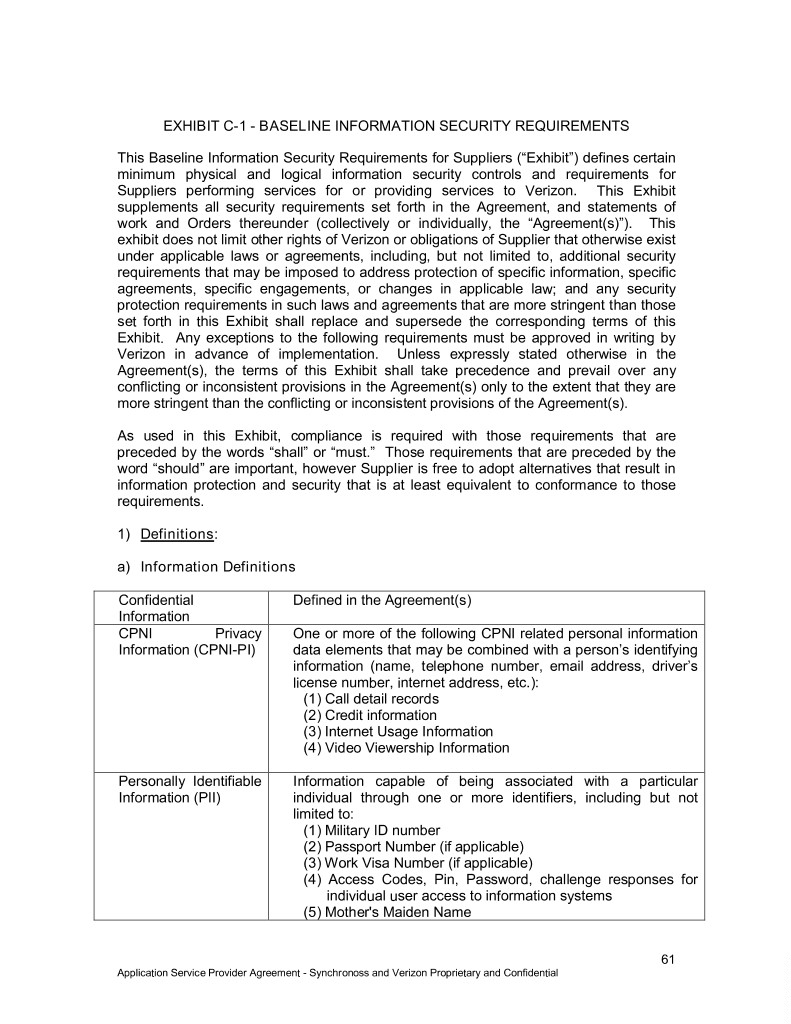
EXHIBIT C-1 - BASELINE INFORMATION SECURITY REQUIREMENTS This Baseline Information Security Requirements for Suppliers (“Exhibit”) defines certain minimum physical and logical information security controls and requirements for Suppliers performing services for or providing services to Verizon. This Exhibit supplements all security requirements set forth in the Agreement, and statements of work and Orders thereunder (collectively or individually, the “Agreement(s)”). This exhibit does not limit other rights of Verizon or obligations of Supplier that otherwise exist under applicable laws or agreements, including, but not limited to, additional security requirements that may be imposed to address protection of specific information, specific agreements, specific engagements, or changes in applicable law; and any security protection requirements in such laws and agreements that are more stringent than those set forth in this Exhibit shall replace and supersede the corresponding terms of this Exhibit. Any exceptions to the following requirements must be approved in writing by Verizon in advance of implementation. Unless expressly stated otherwise in the Agreement(s), the terms of this Exhibit shall take precedence and prevail over any conflicting or inconsistent provisions in the Agreement(s) only to the extent that they are more stringent than the conflicting or inconsistent provisions of the Agreement(s). As used in this Exhibit, compliance is required with those requirements that are preceded by the words “shall” or “must.” Those requirements that are preceded by the word “should” are important, however Supplier is free to adopt alternatives that result in information protection and security that is at least equivalent to conformance to those requirements. 1) Definitions: a) Information Definitions Confidential Defined in the Agreement(s) Information CPNI Privacy One or more of the following CPNI related personal information Information (CPNI-PI) data elements that may be combined with a person’s identifying information (name, telephone number, email address, driver’s license number, internet address, etc.): (1) Call detail records (2) Credit information (3) Internet Usage Information (4) Video Viewership Information Personally Identifiable Information capable of being associated with a particular Information (PII) individual through one or more identifiers, including but not limited to: (1) Military ID number (2) Passport Number (if applicable) (3) Work Visa Number (if applicable) (4) Access Codes, Pin, Password, challenge responses for individual user access to information systems (5) Mother's Maiden Name 61 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential
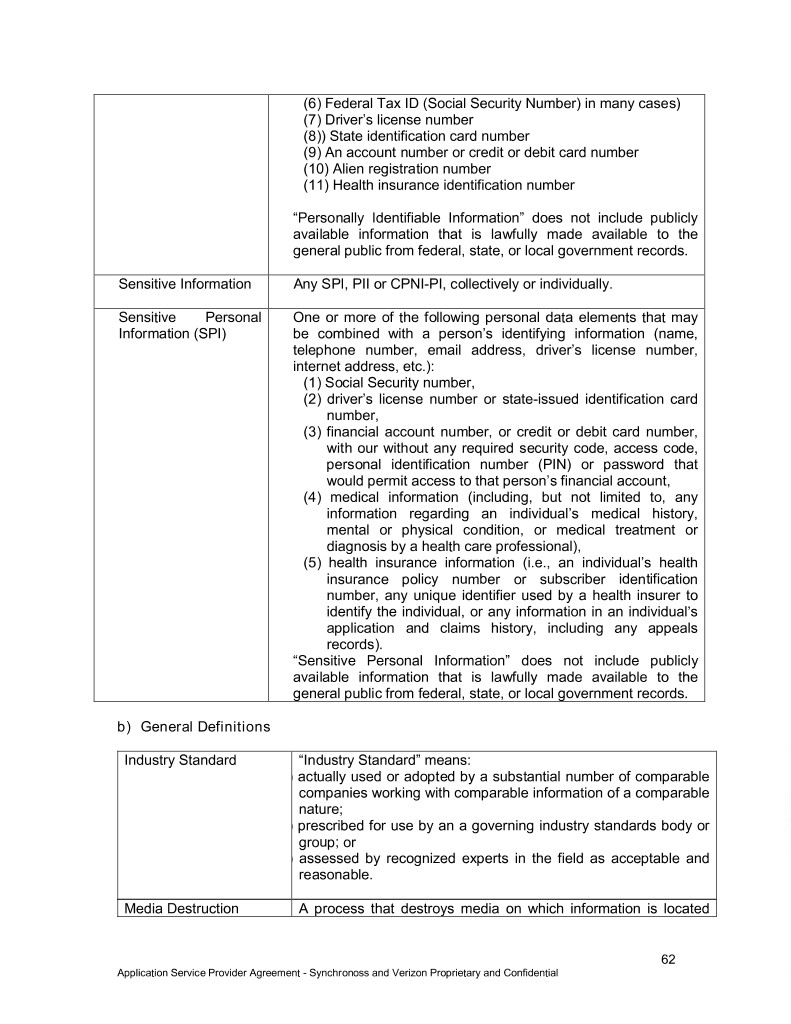
(6) Federal Tax ID (Social Security Number) in many cases) (7) Driver’s license number (8)) State identification card number (9) An account number or credit or debit card number (10) Alien registration number (11) Health insurance identification number “Personally Identifiable Information” does not include publicly available information that is lawfully made available to the general public from federal, state, or local government records. Sensitive Information Any SPI, PII or CPNI-PI, collectively or individually. Sensitive Personal One or more of the following personal data elements that may Information (SPI) be combined with a person’s identifying information (name, telephone number, email address, driver’s license number, internet address, etc.): (1) Social Security number, (2) driver’s license number or state-issued identification card number, (3) financial account number, or credit or debit card number, with our without any required security code, access code, personal identification number (PIN) or password that would permit access to that person’s financial account, (4) medical information (including, but not limited to, any information regarding an individual’s medical history, mental or physical condition, or medical treatment or diagnosis by a health care professional), (5) health insurance information (i.e., an individual’s health insurance policy number or subscriber identification number, any unique identifier used by a health insurer to identify the individual, or any information in an individual’s application and claims history, including any appeals records). “Sensitive Personal Information” does not include publicly available information that is lawfully made available to the general public from federal, state, or local government records. b) General Definitions Industry Standard “Industry Standard” means: ) actually used or adopted by a substantial number of comparable companies working with comparable information of a comparable nature; ) prescribed for use by an a governing industry standards body or group; or ) assessed by recognized experts in the field as acceptable and reasonable. Media Destruction A process that destroys media on which information is located 62 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential
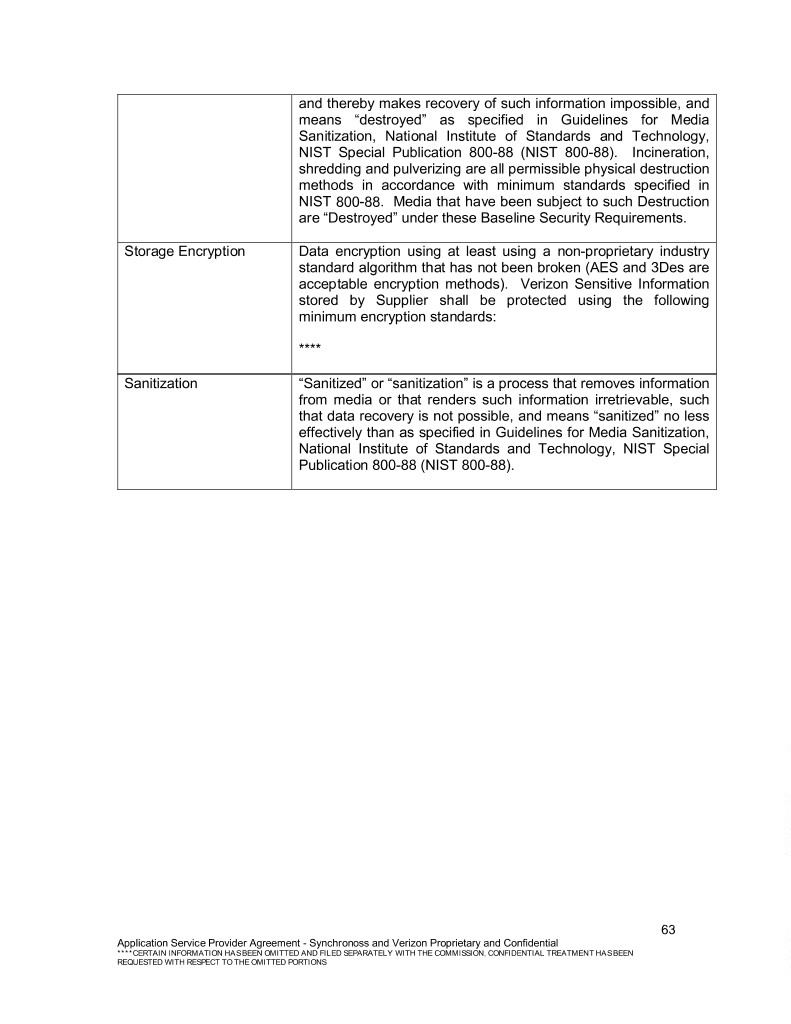
and thereby makes recovery of such information impossible, and means “destroyed” as specified in Guidelines for Media Sanitization, National Institute of Standards and Technology, NIST Special Publication 800-88 (NIST 800-88). Incineration, shredding and pulverizing are all permissible physical destruction methods in accordance with minimum standards specified in NIST 800-88. Media that have been subject to such Destruction are “Destroyed” under these Baseline Security Requirements. Storage Encryption Data encryption using at least using a non-proprietary industry standard algorithm that has not been broken (AES and 3Des are acceptable encryption methods). Verizon Sensitive Information stored by Supplier shall be protected using the following minimum encryption standards: **** Sanitization “Sanitized” or “sanitization” is a process that removes information from media or that renders such information irretrievable, such that data recovery is not possible, and means “sanitized” no less effectively than as specified in Guidelines for Media Sanitization, National Institute of Standards and Technology, NIST Special Publication 800-88 (NIST 800-88). 63 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential ****CERTAIN INFORMATION HAS BEEN OMITTED AND FILED SEPARATELY WITH THE COMMISSION. CONFIDENTIAL TREATMENT HAS BEEN REQUESTED WITH RESPECT TO THE OMITTED PORTIONS
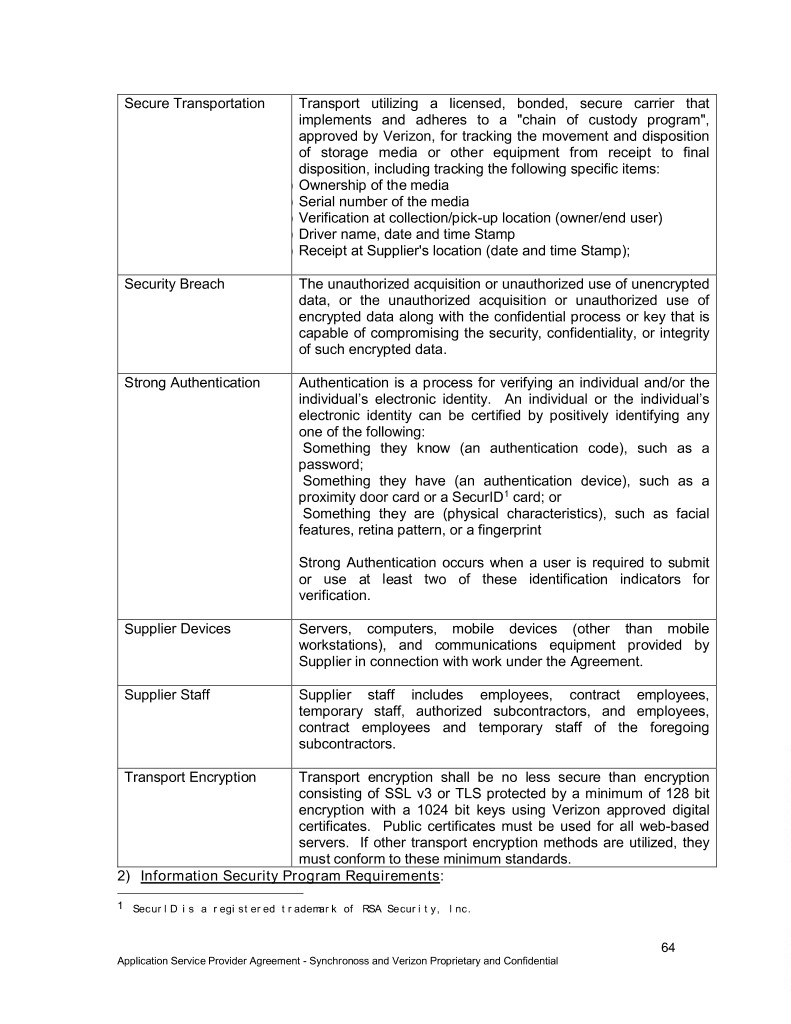
Secure Transportation Transport utilizing a licensed, bonded, secure carrier that implements and adheres to a "chain of custody program", approved by Verizon, for tracking the movement and disposition of storage media or other equipment from receipt to final disposition, including tracking the following specific items: ) Ownership of the media ) Serial number of the media ) Verification at collection/pick-up location (owner/end user) ) Driver name, date and time Stamp ) Receipt at Supplier's location (date and time Stamp); Security Breach The unauthorized acquisition or unauthorized use of unencrypted data, or the unauthorized acquisition or unauthorized use of encrypted data along with the confidential process or key that is capable of compromising the security, confidentiality, or integrity of such encrypted data. Strong Authentication Authentication is a process for verifying an individual and/or the individual’s electronic identity. An individual or the individual’s electronic identity can be certified by positively identifying any one of the following: Something they know (an authentication code), such as a password; Something they have (an authentication device), such as a proximity door card or a SecurID1 card; or Something they are (physical characteristics), such as facial features, retina pattern, or a fingerprint Strong Authentication occurs when a user is required to submit or use at least two of these identification indicators for verification. Supplier Devices Servers, computers, mobile devices (other than mobile workstations), and communications equipment provided by Supplier in connection with work under the Agreement. Supplier Staff Supplier staff includes employees, contract employees, temporary staff, authorized subcontractors, and employees, contract employees and temporary staff of the foregoing subcontractors. Transport Encryption Transport encryption shall be no less secure than encryption consisting of SSL v3 or TLS protected by a minimum of 128 bit encryption with a 1024 bit keys using Verizon approved digital certificates. Public certificates must be used for all web-based servers. If other transport encryption methods are utilized, they must conform to these minimum standards. 2) Information Security Program Requirements: 1 SecurID is a registered trademark of RSA Security, Inc. 64 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential

Supplier is required to maintain an information security program that at minimum includes the following: a) One or more designated qualified employees must be responsible to maintain the Supplier information security program. b) Supplier must maintain written information security policies and standards that address all information security requirements contained in the Agreement(s); that are at minimum consistent in all material respects with the requirements of this Exhibit and with applicable Industry Standards; and that support the confidentiality, integrity and availability of Supplier systems, information and business operations and the confidentiality, integrity and availability of Verizon Sensitive Information and Confidential Information. In addition, such policies and standards must conform to all applicable data protection laws and regulations. c) Supplier executive management must endorse information security polices and standards; d) Supplier Staff must receive periodic training (at least annually) to understand Supplier’s security policies, and must acknowledge their adherence to Supplier’s security policies. Written certification of the periodic training and of the acknowledgement of information security policies by Supplier employees and permitted contractors must be maintained by supplier for inspection by Verizon upon reasonable request. e) Non-compliance with Supplier’s information security policies must result in meaningful discipline. f) Supplier Information Security program must include periodic education and awareness messages to Supplier Staff that consist of relevant and timely information to sensitize such staff to the importance of security for Sensitive Information and Confidential Information, complying with applicable use requirements and limitations, the proper use of Supplier’s security systems, and the requirements of Supplier’s information security program. g) Supplier must review its security measures on an ongoing basis, at least annually and whenever there is a material change in business practices that may implicate the security or integrity of records containing Sensitive Information. Such review will identify and assess reasonably foreseeable internal and external risks to the security, confidentiality and/or integrity of any electronic, paper or other records containing Sensitive Information. h) Supplier must regularly monitor its security measures to identify and assess reasonably foreseeable risks to the security, confidentiality and/or integrity of Sensitive Information and to ensure that its information security program is operating in a manner reasonably calculated to prevent unauthorized access to or unauthorized use of Sensitive Information, and to ensure that the security program continues to comply with applicable laws. Supplier will promptly notify Verizon of any findings of deficiencies in its security program and of its plans mitigating such deficiencies, and Supplier will upgrade its information security safeguards as necessary to minimize the risks associated with those deficiencies. 65 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential

i) Supplier must, no less often than annually, audit each computer (PC or workstation) that is connected to the Verizon corporate network or to Verizon servers to verify that each such computer has the antivirus and firewall capabilities and the periodic updates thereto required in this Exhibit. Supplier must immediately remedy any non-conforming computer before it is reconnected with the Verizon corporate network or a Verizon server. Supplier must maintain the results of such audits, including records of non-conformities found and their remediation, for no less than three years, and provide those results to Verizon on request. j) Supplier must flow down to all permitted subcontractors the obligation to comply with this Exhibit. 3) Physical Security Requirements (Suppliers conducting information processing of Verizon Sensitive Information at Supplier Premises) a) Personnel Security i) To the extent Supplier Staff are provided access to Verizon computers, systems, servers, systems and resources (“Verizon Resources”) in order to perform services for Verizon, Supplier must ensure that such staff are notified that they are not entitled to privacy protection if they access such Verizon Resources, and that access to and communications with Verizon Resources may be monitored by Verizon. b) Facilities Access Control i) Supplier must have controls in place to allow only authorized individuals into Supplier facilities where Verizon Sensitive Information and/or Confidential Information is stored or is accessible. ii) Facility access control systems must be secured from tampering, circumvention or destruction. iii) Facility access control systems must be maintained at all times in functional order and must be updated or changed if they become compromised or ineffective (for example, if keys are stolen, the locks should be changed). iv) Facility access controls must be Industry Standard, and should include some or all of the following elements: (1) Issuance of employee or contractor identification badges; (2) Use of smartcards or other electronic or physical identity verification systems (pin/key access locks, biometrics, etc.); (3) Use of dedicated security personnel who control access to the Supplier’s facilities; (4) 24x7 main lobby security guard station; (5) Locks on all ground floor windows; (6) Alarmed locks on all external doors; and (7) Use of CCTV on all entrances and entrances to data computing facilities, to include ninety (90) days of video storage. 66 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential
v) Visitors accessing the facility must be managed in accordance with the following practices: (1) Visitors to Supplier facilities must be registered in a visitor log. The log should document the visitor’s name, the firm represented, and the employee authorizing physical access on the log. The log should be retained for inspection by Verizon for a minimum of three months, unless otherwise restricted by law. (2) Visitors should be issued temporary identification badges specific to the length of the expected visit in the facility. Visitor identification badges must be returned upon the visitor’s departure. (3) Temporary visitor identification should be noticeably different from Supplier’s normal employee and contractor identification. (4) Supplier must inform employees of the approved formal policies for granting access to visitors at Supplier facilities. (5) Any visitor to a Supplier facility that accesses areas where Verizon Sensitive Information and/or Confidential Information is stored, processed or transmitted must be accompanied and supervised at all times by a Supplier employee who is specifically authorized to access confidential Verizon data. (6) Prior to granting a visitor to a Supplier facility access to any computer, server or system containing Verizon Sensitive Information and/or Confidential Information, access by each such visitor must be approved in writing by the designated Verizon contact, and the visitor must be positively identified as the person for whom Verizon has given such approval. (7) Under no circumstances may visitors be left unattended in an area where they have physical access to equipment that handles Verizon Sensitive Information and/or Confidential Information. c) Facilities Access Monitoring: i) The Supplier should utilize appropriate levels of monitoring equipment in public areas of their facilities to ensure the auditing of Supplier facility entry and exit activity can be performed. ii) For all Supplier access control and monitoring installations, appropriate safeguards and retention of records should be implemented to ensure the integrity of the systems and the availability of the records if the need arises. d) Separate Information Processing Environments At a minimum, the following physical security and access controls must be implemented and maintained throughout the terms of the engagement: i) Verizon Sensitive Information and/or Confidential Information must not be processed on servers that are accessible in general business areas of Supplier’s facility and must be isolated in dedicated information processing areas with independent physical, monitoring, environmental and health and human safety systems (referred to as a “Computer Room”). 67 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential
ii) Access to any information processing area where Verizon Confidential and/or Sensitive information is processed must be restricted to authorized Supplier personnel only. iii) Supplier must implement physical access policies and procedures to ensure that physical access is revoked when it is no longer needed or appropriate (for example, immediately removing access for separated employees or removing access for employees who are no longer authorized to access Verizon Confidential and/or Sensitive Information). Removal of Physical Access should occur in a timely manner not to exceed 24 hours. iv) Supplier must employ technical and organizational mechanisms to prevent unauthorized copying of Sensitive Information within Information Processing Environments. These mechanisms shall include disabling/restricting local ports so as to prevent downloading of data onto removable USB drives, MP3 players or similar devices, restrictions on uploading or file transfer from the facility to unauthorized recipients, and a prohibition on the use of cameras (excluding CCTV security unit) and other screen capture devices. e) Computer Room Physical Security Requirements Computer room facilities where Verizon Sensitive Information and/or Confidential Information is stored, processed or transmitted must implement the following information security controls: i) All computer room doors must be secured to prevent unauthorized access into the room. ii) Each computer room door must have signs on both sides indicating it is to be closed and locked with a contact to notify if it is found unsecured. iii) Supplier Staff must be instructed to immediately report unsecured doors. iv) Supplier must implement a reliable process of designating staff access to Computer Rooms. v) Supplier Staff should only be authorized to enter a Computer Room for a legitimate business need and a record of the individual’s identity, justification and duration of access should be maintained. vi) A separate electronic access control system utilizing strong authentication should be installed on Computer Room doors that will only allow authorized personnel access to the room, unless access to the room is controlled 24 hours a day, 7 days a week, by a guard. (1) The access control system must be secured against tampering. (2) The access control system must log the entry and exit of staff for each time the door is opened. Entry and exit logs should contain a reliable time stamp, room location and identification of the person who gained access or exited the room. (3) The access control system should alert security staff in the event that a secured door has been open beyond a reasonable amount of time (for example, by being propped open and unattended). 68 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential

vii) Supplier should periodically review access records to ensure that access controls are being enforced effectively. Any discrepancies or unauthorized access must be investigated immediately by Supplier information security personnel and reported to the Verizon Sponsor. viii) Supplier should periodically review CCTV video storage to ensure that access controls are being enforced effectively to prevent unauthorized entry. Any unauthorized access must be investigated immediately by Supplier information security personnel and Supplier must provide Verizon notice of such breach of security in accordance with this Exhibit. f) Asset Disposal and Reclamation i) Upon conclusion or termination of Supplier’s work for Verizon, at Verizon’s option Supplier must either: (1) Sanitize or Destroy all copies of all Verizon information maintained under the Agreement or an applicable Order or Statement of Work (collectively, “work agreement”), including all backup and archival copies, or (2) return to Verizon all copies of all Verizon information maintained under work agreement, as well as all backup and archival copies. ii) When no longer required for performance under the Agreement and prior to disposition, recycle, or resale, electronic and non-electronic (hardcopy) media containing Verizon Sensitive Information and/or Confidential Information shall be rendered unreadable and unrecoverable by Sanitization or Destruction. iii) All non-electronic media containing Verizon Sensitive Information and/or Confidential Information must be Destroyed utilizing a cross cut shredder. iv) All electronic media containing Verizon Sensitive Information and/or Confidential Information shall be destroyed or rendered unusable when such information is no longer required for performance under this agreement and prior to disposition, recycle or resale, using methods that prevent access to information stored in that type of media. At minimum, media containing Verizon Sensitive Information and/or Confidential Information shall be “sanitized” in accordance with NIST Special Publication 800-88. Although Verizon prefers that data be disposed of in a manner consistent with “Destruction”, at a minimum, electronic media that at any point contains Verizon Confidential and/or Sensitive Information must be disposed in a manner consistent with “Sanitization” requirements in the NIST standard. Additionally the following minimum standards must be met: (1) All tape must be incinerated or degaussed with a degausser that meets the performance standards provided by the US National Security Agency (NSA) which can be found at ▇▇▇▇://▇▇▇.▇▇▇.▇▇▇/▇▇/_▇▇▇▇▇/▇▇▇▇▇▇▇▇▇▇/▇▇▇/▇▇▇_▇▇▇-▇▇▇- 9-12.PDF. (2) When Sanitizing magnetic or flash media, the preferred method of Sanitization is to perform a Secure Erase (to be used only for ATA Drives and SCSI drives, where technically feasible - available from the University of San Diego CMRR, at 69 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential

▇▇▇▇://▇▇▇▇.▇▇▇▇.▇▇▇/▇▇▇▇▇▇/▇▇▇▇▇▇/▇▇▇▇▇▇▇▇▇▇▇.▇▇▇▇▇). Alternatively, if Secure Erase is technically inappropriate or is not used, a minimum of a three pass block erasure shall be utilized that removes the data from magnetic disk media by sequentially overwriting all addressable locations in the following manner, and then verifying the same by a disk read: (i) overwriting with a random pattern; (ii) overwriting with binary zeros; and (iii) overwriting with binary ones. The National Institute of Standards and Technology and Federal Agencies Security Practices initiative (FASP) have specified the Active KillDisk software, ▇▇▇▇://▇▇▇.▇▇▇▇▇▇▇▇.▇▇▇/▇▇▇▇▇▇.▇▇▇, as a compliant sanitization tool for IDE, SCSI and ATA drives. (3) Optical Disk media must be destroyed. (4) Removal of non-functional electronic storage media: Non- functional electronic storage media (e.g., a failed drive) may not be capable of Sanitization, and therefore must be either returned to Verizon or Destroyed. When removing non-functional electronic storage media from a Verizon or Supplier facility, Supplier may Destroy the media onsite prior to removal as specified herein. If the electronic storage media are not Sanitized or Destroyed, and must be removed from the Verizon or Supplier premises without such sanitization or destruction, Supplier shall utilize Secure Transportation to a Verizon or other disposal site. Supplier shall track disposition of the media (e.g., Destroyed by Supplier, Sanitized by Supplier, conveyed to a Verizon-authorized third party for Destruction, etc.) and provide to Verizon a Certificate of Sanitization (COS) and/or Certificate of Destruction (COD) upon completion of the Sanitization, or Destruction. v) Required Records: Supplier shall maintain records at the serial number level for four years of all receipts and disposition which identify the media (or computing assets) being processed. All records pertaining to the disposition of each of the media or computing assets must be available for audit and verification by Verizon during this four year period. The Supplier must provide reports monthly to Verizon g) Shipment of Sensitive Information: i) Non-Electronic Sensitive Information: Whenever possible, Sensitive Information in non-electronic form should be converted to electronic form for secure transmission in accordance with this Exhibit, and all non-electronic hard copies Destroyed as specified in this Exhibit. If such conversion is impracticable, Sensitive Information in non-electronic hardcopy form must be shipped in the United States using U.S. Postal Service Registered Mail with return receipt, or the substantial equivalent thereof by a licensed overnight courier or delivery service. Any shipment of Sensitive Information in non- electronic (hardcopy) form between a United States and foreign point must be specifically pre-approved by Verizon in writing and must be shipped in accordance with such instructions as Verizon provides in its approval. 70 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential

ii) Electronic Media containing Sensitive Information: If electronic media containing Sensitive Information are shipped, the Sensitive Information must be encrypted using Storage Encryption unless shipped in accordance with the Secure Transportation requirements herein. 4) Logical Security Requirements (Suppliers conducting information processing of Verizon Information) a) Logical Access Control Supplier must develop logical access controls for all computing systems handling Verizon Confidential and/or Sensitive Information. Logical Access controls must include: i) The assured enforcement of authentication controls to limit access to information systems to only those individuals who are currently active and who are authorized to access a given information system. ii) A secure and reliable method of enforcing authorization controls which limit access to Verizon Sensitive Information and Verizon Confidential Information to only previously-authorized Supplier Staff. iii) Use of the “principle of least privilege” model for access, enabling Supplier personnel to access only such information and resources as are necessary when they perform under the Agreement for the role assigned to the authorized user, iv) A process of controlling User IDs and other identifiers to ensure they are unique among users and are not shared. Note: Sensitive Personal Information must not be used as an authentication or an authorization mechanism to obtain a password, or for log in rights or for access to any application, system, website or database owned or operated by Verizon or on Verizon’s behalf. The last four digits of a Social Security number, passwords, PINs, challenge responses and/or access codes are permitted to be used for such purposes in conjunction with other data. v) A process which will immediately terminate access by an employee or contractor who no longer requires access to perform under the Agreement (e.g., a terminated or reassigned employee/contractor). vi) Periodic review of access, authorization and other applicable monitoring logs on all systems to ensure the access control and authentication systems are performing as expected. vii) Processes that utilize industry standard password selection and aging procedures to limit opportunities for compromise of password security. Such password procedures should include but not be limited to the following: (1) A process to ensure that no user or information system may utilize Supplier-supplied default account passwords. (2) A secure method of assigning and selecting passwords or other unique identity validation values, such as biometric registration values or the issuance of one-time-password token devices. 71 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential
(3) Limit repeated access attempts by locking out the user ID after not more than six (6) attempts with a thirty (30) minute minimum lockout duration (4) Verification of user identity before password resets; (5) All passwords must be have first-time passwords set to a unique value for each user and change immediately after the first use; (6) Inactive accounts must be disabled after 90 days; (7) Password must be changed at least every ninety (90) days; (8) Passwords must be at least eight (8) characters and must include letters and numbers; (9) Supplier must require users to submit passwords that are different than any of the last four (4) passwords the individual has used; (10) If a session has been idle for more than fifteen (15) minutes, require the user to re-enter the password to reactivate the terminal. (11) Control and encrypt with a 1-way hash, data security passwords to ensure that such passwords are kept in a location and/or format that does not compromise the security of the data they protect. b) Access Logging and Monitoring i) Supplier must maintain electronic logs of persons accessing Verizon Confidential and/or Sensitive Information depicting the details of the access and transactional changes made. ii) Logs must be maintained for inspection by Verizon for a minimum of ninety (90) days. iii) Logs shall be stored centrally on Supplier owned or controlled systems that cannot be altered by users or privileged users. iv) At a minimum logs shall capture the following information for all access to Verizon Confidential and/or Sensitive Information: (1) Unique user ID; (2) Login/Logout time; (3) System/data set accessed; (4) Failed login attempts; (5) Activity (for privileged users such as data base administers, system administrators, etc.) including changes to permissions, changes to data, etc.) v) Access logs shall be reviewed by Supplier at least daily and provided to Verizon for inspection upon reasonable request. Alternatively, log parsing tools which automatically generate alerts based on information security rules 72 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential

may be utilized provided that alerts are reviewed and appropriate action is taken, at least daily. c) Network and Communications Security The Supplier must develop and implement network and communications security policies, procedures and technology to control and detect potential network and communications information security system issues and failures. At a minimum, Supplier must have: i) Firewall controls at appropriate points in the Supplier network to control the ingress and egress of communications and data to environments containing Verizon Sensitive Information and/or Confidential Information. At a minimum, Network Firewalls must protect all connections to open, public networks. System Security Patches and updates for Firewalls must be implemented in a timely manner not to exceed 30 days following release. ii) Supplier must employ industry standard intrusion detection systems (IDS) for any environment into which Sensitive Information will be placed. (1) Network IDS must be placed on network connection points between the Supplier environment containing the Verizon Confidential and/or Sensitive Information and other network environments. Alternatively, Host- Based IDS may be placed on all computing assets storing, processing or transmitting Verizon Confidential and/or Sensitive Information. (2) IDS must be configured with business rules appropriate to the environment and must be configured to generate alerts immediately. (3) Signatures and software for IDS must be kept current and up to date. (4) IDS alerts must be reviewed at least daily by trained security personnel. iii) System Segmentation (1) Information systems storing, processing or transmitting Sensitive Information must be logically isolated from systems that handle other companies’ information. For example, Supplier must use separate database server instances for the processing of Verizon data or must use separate virtual operating system images than those used or accessed by other companies who the Supplier may also service. (2) At no time may Verizon Sensitive Information and/or Confidential Information be housed on a server shared by companies other than the contracting Supplier. For example, a shared web server that is used by several companies and maintained by an Internet Service Provider must not be used to house Verizon data. This requirement also applies to “cloud-based” services. (3) Internet-facing web servers must be dedicated to this task, and must not host internal (intranet) applications for the Supplier. 73 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential
iv) Transport Encryption for all electronic communications that contain Sensitive Personal Information, and Transport Encryption for Verizon Confidential and/or Sensitive Information that traverses networks outside of the direct control of the Supplier or Verizon (including, but not limited to, the Internet, WI-FI and mobile phone networks). v) Transport encryption of all data containing Sensitive Information to be transmitted wirelessly. vi) Policies, procedures and appropriate technology solutions to ensure all systems receive and apply the most current security updates on a regular basis. vii) No remote access to Sensitive Information, from home or other location that is not at the premises of the Supplier or Verizon shall be permitted without the specific authorization of Verizon, and such authorization will be conditioned on measures that maintain the security of such Sensitive Information and that prevent unauthorized access thereto, or unauthorized copying or retention thereof. All remote access to Sensitive Information must require Strong Authentication and Encrypted transmissions. viii) Logical Security Requirements when connecting Supplier controlled devices to Verizon Networks (1) All Supplier Devices to be used to connect to the Verizon Network must be either provided by Verizon or alternative must be owned or leased by the Supplier (personally-owned equipment may not be used to perform work for Verizon). (2) Supplier personnel accessing Verizon networks must not have any concurrent access to other non-Verizon networks from their workstation(s) while connected to Verizon’s Network unless that access is through the Verizon Network. (3) All computing device remote access to the Verizon Network must utilize approved Verizon Virtual Private Networks including Client-based access, transport encryption and strong authentication. (4) Supplier Devices must not traverse any unencrypted wireless networks while attaching to the Verizon network. All wireless connections should utilize transport encryption utilizing WPA2 in enterprise or PSK mode at a minimum (WEP encryption is not permitted). d) Information Systems and Device Management i) General Requirements (1) All Supplier Devices used to store, process or transmit Verizon Confidential and/or Sensitive Information, and/or to provide information services to Verizon in connection with work under the Agreement, must either be provided by Verizon or alternatively, must be owned or leased by the Supplier (personally-owned equipment may not be used to perform work for Verizon). 74 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential

(2) All assets controlled by Supplier used to perform work for Verizon must be tracked using an inventory management system including the following information. a. Name, location, retention schedule, and Verizon-assigned data classification level (as described in the Verizon Data Classification in Section 6 of CPI-810) of the information asset such as a database or file system. b. A knowledgeable individual owner of each information asset (the default owner of an information asset is its creator) c. Computer systems (i.e. Servers – Host Name/IP Address) that house Verizon data d. Storage encryption status for any Sensitive Information (both at rest and on any back up media). (3) All Supplier Devices used to perform work for Verizon should be centrally managed by the Supplier. (4) All Supplier Devices used to perform work for Verizon must be managed for the application of operating system and applicable software patches. Critical operating system and software security patches must be installed in a timely manner not to exceed one (1) month following release for public availability. (5) All Critical Security Patches for workstations shall be installed within 7 days of publication from the software or hardware vendor. (6) All Supplier Devices shall have current antivirus software installed (if technically feasible) and configured to check for updates on a daily basis at a minimum. (7) All Supplier Devices that connect to the Internet shall have a personal firewall or its equivalent enabled and configured to only allow connections to authorized business applications. By default, the personal firewall must use a default deny rule that blocks inbound traffic that is not specifically allowed in the course of a specific communication (8) All Supplier mobile computing devices (notebook computers, PDAs, etc.) and portable storage devices (portable drives, flash drives, thumb drives, optical disc media, etc.) used to store or process Verizon Sensitive Information and/or Confidential Information must have “whole disc” or other device Storage Encryption enabled for internal as well as peripheral and removable media. Encryption keys for mobile computing devices and portable storage devices must be kept in escrow and sufficiently protected by the Supplier to enable forensic recovery of data on any protected device. Whole disk Encryption should be implemented with a Pre-Boot authorization configuration. (9) Supplier personnel must not communicate, store or process any Verizon confidential data on any email, storage or processing 75 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential

repository that is outside of the direct ownership and control of Supplier. For example, the use of personal web email accounts, web-based backup services, Internet-based document editing or public cloud-based computing services are prohibited without express written permission from the Verizon Sponsor. (10) Sensitive Information data should not be stored or used in testing or other non-production environments. If this use is required, an authorized exception permitting such use must granted in writing by Verizon, and such data must either be (a) masked so that it no longer meets the definition of Sensitive Information, or (b) protected using controls against unauthorized access, copying or viewing that are comparable to those required for the protection of Sensitive Information in production environments. ii) Data Storage Requirements (1) Data Obfuscation a. All Sensitive Personal Information and Personally Identifiable Information at rest must be encrypted using Storage Encryption. CPNI-PI should also be encrypted using Storage Encryption. Storage Encryption of the device on which such information is stored will satisfy these requirements. b. Data Replacement (e.g. SAFE) or field level masking may be acceptable methods of obfuscation. Such methods must be approved in writing by Verizon prior to implementation. (2) Encryption Key Management a. Supplier shall implement key and seed management procedures that enable Verizon Confidential or Sensitive Information to be retrieved if the person who encrypted such data is unable or unwilling to decrypt the data. b. Keys and seeds shall be properly protected, using either physical procedures including very limited access control, separation of duties and logging/monitoring key access or encryption no less robust than is required for Supplier’s own most highly confidential or Sensitive Personal Information and not accessible by unauthorized personnel. c. Additionally, Supplier shall require split keys for all key encryption such that one person does not have the full key for any data encrypted at rest. Generally, Encryption Keys should also be encrypted. d. Supplier shall maintain a written and tested process for key rotation on a periodic basis (at least annually) or in event of compromise (does not apply to keys for data stored in offsite backup). iii) Data Backup Requirements 76 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential
(1) Verizon Sensitive Information and/or Confidential Information must be backed up on separate tapes/drives than data belonging to or accessed by other companies. (2) Backups must be encrypted with Storage Encryption that accommodates key escrow by supplier (3) Backup media must be physically secured against theft or tampering and must implement physical controls that comply with all applicable state and federal requirements. (4) Chain of custody records must be maintained for all backup media containing Verizon Sensitive Information and/or Confidential Information moving to offsite storage of backups (5) Supplier must ensure that all backup media is tracked and must ensure that contractual data destruction requirements can be met. 5) Coding Practices a) Supplier must disclose to Verizon all open source code utilized to develop custom code and provide Verizon an opportunity to review all such open source code prior to its utilization within or with custom developed code. b) Supplier shall implement peer review throughout the development process and make use of code review tools to ensure secure coding and to identify malicious code or code misconfigurations. 6) Business Continuity Planning/Disaster Recovery (BCP/DR) for Suppliers performing Information Processing at Supplier Locations a) So that the business processes may be quickly re-established following a disaster or outage, Supplier must maintain an updated inventory of all critical production systems and supporting hardware, applications and software, projects, data communications links, and critical staff at both primary and secondary sites. b) To the extent Verizon has contracted for BCP/DR services from Supplier, Supplier must ensure preparation, maintenance, and regular test of a BCP/DR plan that ensures that all critical computer and communication systems will be available in the event of emergency or a disaster, and meet service level and recovery time and recovery point objectives. c) To the extent Verizon has contracted for BCP/DR services from Supplier, BCP/DR plans must be tested at least annually, and all test results must be periodically reported to Verizon. d) Any emergency event-related disruption of business activities must be reported forthwith to a designated Verizon contact. 7) Notification of Breach of Security a) Supplier must maintain an internal or third-party professional security service with the capability of investigating, responding to and mitigating any potential or actual security incidents within Supplier’s area of operations that involves Verizon Sensitive Information and/or Confidential Information throughout the period of 77 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential

time in which Supplier maintains such information in its systems or facilities (or those of permitted subcontractors). b) The supplier’s incident response team must have documented formal procedures that comply with Industry Standards and applicable laws addressing investigation and response to information security incidents. The procedures must include documentation describing the steps taken to correct discovered breaches. c) Supplier’s information security policies and procedures must require the immediate reporting of suspected or actual violations of policy to an appropriate Supplier security contact. d) Supplier must establish and maintain an easily understandable procedure for Supplier Staff to report security incidents to an appropriate Supplier security contact, and for such information to be reported to a designated Verizon contact. e) Supplier must as soon as practicable, not to exceed two hours following discovery of an unauthorized disclosure or security breach, notify and update Verizon via electronic mail to ▇▇▇▇▇▇▇▇.▇▇▇▇▇▇@▇▇▇▇▇▇▇.▇▇▇ such of such disclosure or breach, with confirmation sent to the contract notice addressee set forth in the Agreement by the means set forth therein, of: i) Any Security Breach or other actual or threatened unauthorized access or release of Verizon Sensitive Information or Confidential Information or to the systems holding or providing access to such Verizon information. ii) Any occurrences of viruses and malicious code, not mitigated by deployed detection and protection measures, on any workstation or server used to provide services under the Agreement or applicable statement of work or Order thereunder. f) Following notification to Verizon in accordance with the previous subsection, or notification to Supplier by Verizon of a security incident or breach that Verizon reasonably believes was caused by Supplier, Supplier must: provide regular updates to Verizon; investigate the incident or potential breach of security; report the results of such investigation to Verizon; cooperate with Verizon in any Verizon investigation of the breach and the effects thereof; allow Verizon to inspect Supplier computers that Verizon reasonably believes caused or were involved in the breach; and implement corrective measures to prevent future breaches. g) Notwithstanding its notification(s) to Verizon, Supplier must comply with all applicable notification requirements imposed by law, including but not limited to notification requirements under federal and state laws protecting privacy. 8) Audit Compliance and Verizon’s Right to Audit Supplier Operations a) Supplier must be prepared to provide necessary confirming documentation in support of Verizon’s external audits (such as ▇▇▇▇▇▇▇▇-▇▇▇▇▇ or PCI) upon Verizon’s request pursuant to the terms of the Agreement. b) Supplier must permit Verizon to audit its security controls periodically, not more than once per calendar year or other period specified in the Agreement, and reasonably cooperate with Verizon in such audit. c) Supplier must provide copies of relevant security policy, process, and procedure documents to Verizon for review and audit purposes upon request. Verizon may 78 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential

review and recommend reasonable changes, and Supplier must amend the policies or respond with mitigating controls and responses within a reasonable time period for mutually agreed to changes. 79 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential

EXHIBIT C- 2 – VERIZON WIRELESS NETWORK SECURITY REQUIREMENTS 1. DEFINITIONS The terms defined in this Section shall have the meanings set forth below whenever they appear in this Exhibit, unless the context in which they are used clearly requires a different meaning or a different definition is described for a particular Section or provision: 1.1. “Confidential Information” shall mean: Verizon customer data and proprietary network information, data pertaining to Verizon systems, networks, services, and the security controls implemented on those systems and networks, data pertaining to Verizon employees, Verizon proprietary and/or trade secret information, and any other information or data labeled as confidential or proprietary under the terms of the Agreement. 1.2. “Industry-standard” shall mean: an accepted set of best practices that are (1) used or adopted by a substantial number of companies that are engaged in a similar type of business (“comparable companies”) to manage information of a similar type; (2) prescribed for use by a governing industry standards body or group; or (3) established by recognized experts in the field as being acceptable and reasonable. 1.3. “Penetration Test” shall mean: part of the Risk Assessment Process whereby highly skilled, experienced and trained person(s), known as “white-hat hackers”, engage in a coordinated and planned attack on computer systems and networks to discover potential vulnerabilities and ensure the logical controls can withstand deliberate attempts to be circumvented. 1.4. “Program” shall mean: the documented and exercised processes and procedures for accomplishing common objectives and monitoring such accomplishment, which may be updated from time to time. 1.5. “Risk Assessment Process” and “Risk Assessment” shall mean: a documented and exercised process used to identify the risks to system security and determine the probability of occurrence, the resulting impact, and identify additional safeguards or modifications that would eliminate and/or adequately mitigate this impact. 1.6. “Risk Management Program” shall mean: the documented and exercised process for identifying, controlling, and mitigating information system related risks. It includes Industry-standard qualitative and/or quantitative Risk Assessment Process; cost-benefit analysis; and the selection, implementation, testing, and evaluation of safeguards, including a determination of steps required to meet the four security goals of Security Assurance. 1.7. “Security Assurance” shall mean: grounds for confidence that the four security goals (i.e., integrity, availability, confidentiality, and accountability) have been adequately met by a specific computer system. “Adequately met” includes (1) functionality that performs correctly, (2) sufficient protection against unintentional errors (by users or software), and (3) sufficient resistance to intentional penetration or bypass. 80 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential

1.8. “Threat-source” shall mean: either (1) intent and method targeted at the intentional exploitation of a Vulnerability or (2) a situation and method that may accidentally trigger a Vulnerability. 1.9. “Threat Analysis” shall mean: the examination and documentation of threat-sources against system Vulnerabilities to determine the potential threats applicable to a specific computer system in a particular operational environment. 1.10. “Vulnerability” (or “Vulnerabilities” in the plural) shall mean: a flaw or weakness in computer system functionality, design, implementation, internal controls, or security procedures that could be exercised (accidentally triggered or intentionally exploited) and result in a security breach or a violation of the system’s security policy. 2. GENERAL REQUIREMENTS 2.1. This Security Requirements Exhibit (“Exhibit”) is applicable to all relevant aspects of Supplier’s performance under the Agreement , including without limitation the development, offering, use and/or maintenance of any service, software or other product there under, and any future releases, versions, updates, enhancements and modifications thereto (“Software” or “Hardware”, as the case may be). 2.2. Supplier will at all times implement and maintain Industry-Standard administrative, physical and technical security controls, which will be followed in all relevant aspects of Supplier’s performance under the Agreement. Such controls will be sufficient in nature and scope to protect (1) the confidentiality, integrity and availability of Verizon’s Confidential Information as well as (2) the availability and integrity of Verizon’s service, network and operations. 2.3. Supplier shall comply with the administrative, physical and technical security controls as described in this Exhibit and in Verizon’s Security Standards & Policies (“Verizon Policies”). Supplier shall request from Verizon all revised and additional Verizon Policies applicable to Supplier’s Software and Hardware before execution of each new work order. 2.4. Notwithstanding anything to the contrary, for such changes or additions to Verizon Policies applicable to Supplier’s Software and Hardware, the parties shall review such documentation for change and exceptions that impact the Software or Hardware. A Change Request may be required for implementation by Supplier of any such changes to the Verizon Policies. 2.5. For each given Authorization Letter, Verizon Policies applicable to the Software and Hardware supporting the Platform under such Authorization Letter shall be set forth in an exhibit to the Authorization Letter as well as any exceptions to this Exhibit or other terms and conditions agreed upon by the Parties pertaining to Verizon Policies or the Information Security Policy. 3. CONFIDENTIAL INFORMATION 3.1. Supplier warrants that Verizon’s Confidential Information shall only be used for the purposes specified under the Agreement. Supplier’s obligation to 81 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential

protect Verizon’s Confidential Information in accordance with the provisions of this Exhibit shall survive indefinitely. Upon expiration or termination of the Agreement, Supplier shall promptly return and/or securely destroy all Verizon Confidential Information except as required by law. 3.2. Supplier shall take appropriate measures to secure Verizon Confidential Information, both during transit and in storage by using Industry-standard mechanisms for protection (e.g., encryption). This protection shall also include all forms of portable media (e.g. flash/usb drive, laptop, CD, DVD, Blu-ray, portable hard drive, cell/smart phone, MP3 player and etc.) 4. INFORMATION SECURITY POLICIES AND PROGRAM Supplier shall implement and maintain a comprehensive and Industry-standard Risk Management Program, including without limitation the following: 4.1.1. Supplier shall have an information security policy which describes the security and privacy controls that Supplier currently implements in its operations to comply with all applicable Verizon Policies and this Exhibit (“Information Security Policy”). Supplier shall establish and maintain a Risk Management Program to implement its Information Security Policy, which shall include without limitation the following: 4.1.1.1. A Risk Assessment Process which shall ensure that Supplier’s operating environment, development environment, systems, applications, networks and procedures are regularly evaluated to identify and remediate security Vulnerabilities. 4.1.1.2. A Program for intrusion and security breach detection, prevention and incident response. 4.1.1.3. A Program for configuration management of systems, network and applications. 4.1.1.4. A Program for the implementation and administration of logical access control(s) to data, systems and network. 4.1.1.5. A Program for the implementation and administration of physical access control(s) to facilities and data. 4.1.1.6. Supplier shall, at minimum, annually review the Risk Management Program using an internal or external auditor to assess compliance with the requirements under its Information Security Policy. 5. SECURE DEVELOPMENT LIFECYCLE Supplier’s controls associated with the development, pre-production testing and delivery of any and all Software and Hardware shall include, without limitation, Supplier’s obligation to: 5.1. Implement Industry-standard security controls for its operating environment, systems, networks and all facilities in which the Software is being developed and/or hosted. 82 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential
5.2. Develop, implement, and comply with Industry-standard secure coding best practices. 5.3. Establish processes, including as appropriate, using Vulnerability source code scanners, operating system security benchmarking tools, web application scanners or other tools or techniques, or information acquired through Industry-standards organizations, to assess the Software or Hardware for security Vulnerabilities prior to production release. 5.4. Follow Industry-standard practices to mitigate and protect against all known and reasonably predictable security Vulnerabilities, including but not limited to: (1) unauthorized access, (2) unauthorized changes to system configurations or data, (3) disruption, degradation, or denial of service, (4) unauthorized escalation of user privilege, (5) service theft, and (6) unauthorized disclosure of Confidential Information. 5.5. Supplier must ensure all security features and configurations survive any update, modification or upgrade to Software and Hardware or are replaced with features and configurations that meet the requirements of this Exhibit, unless prior written consent is obtained from Verizon. 6. SECURITY ASSURANCE Supplier shall maintain a Risk Assessment Process which demonstrates the Security Assurance of Supplier’s Software and Hardware. This Process shall include, but is not limited to: 6.1. Supplier must, at Verizon’s cost, coordinate and conduct a Risk Assessment of its Software and Hardware using a Certified Verizon third- party security testing vendor. This Risk Assessment must be completed **** prior to the initial delivery of Supplier Software and Hardware, respectively or as otherwise agreed upon by the Parties in writing. Supplier shall thereafter, at Verizon’s cost and discretion, repeat this Risk Assessment at the earlier of (1) every major version release or (2) annually for all Software and Hardware deployed in the Verizon network or hosted by Supplier. This Risk Assessment shall include the following: 6.1.1. A Threat Analysis of the Software and Hardware 6.1.2. A Penetration Test of the Software and Hardware 6.1.3. A Risk Assessment of the administrative, technical, logical and physical security controls of the pertinent operating environment, systems, networks, and facilities where Software and Hardware is hosted, if hosted by Supplier. 6.2. Supplier must resolve all high and medium risk Vulnerabilities identified in the Risk Assessment Process prior to production release except as otherwise specified by Verizon in writing. At Verizon request, Supplier shall provide to Verizon a documented resolution timeline **** before production release for all remaining Vulnerabilities to be remediated post production. This document shall include the date by which each Vulnerability will be remediated. 83 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential ****CERTAIN INFORMATION HAS BEEN OMITTED AND FILED SEPARATELY WITH THE COMMISSION. CONFIDENTIAL TREATMENT HAS BEEN REQUESTED WITH RESPECT TO THE OMITTED PORTIONS
6.3. Verizon may request a copy of the scope of work from the above third- party Risk Assessment Process (Section 6.1). Supplier shall deliver this document to Verizon within **** of the initial request. 7. SECURITY BREACH AND INCIDENT RESPONSE 7.1. Supplier shall establish and maintain documented escalation processes for any security breaches and incident responses, including procedures for notifying Verizon within twenty-four (24) hours after a security breach is discovered where such breach may negatively affect Verizon’s reputation, Confidential Information, systems, network, services, data, assets, and/or customers. 7.2. Supplier shall not notify any other parties that an actual or suspected security breach affects Verizon without prior written consent by Verizon, except to the extent required by law. 7.3. Supplier shall cooperate and provide information as required by Verizon and any authorized consultants, contractors, attorneys, or other third parties hired by Verizon to investigate a security breach of Supplier’s operating environment. 7.4. In the event of a security breach affecting Verizon, Supplier must issue a post mortem report to Verizon within forty-eight (48) hours of breach discovery that includes (1) the identification of all Verizon information potentially compromised by such breach; (2) the actions taken by Supplier to mitigate damage caused by the breach; and (3) safeguards implemented to prevent a recurrence of such breach. 8. RIGHT TO RISK ASSESSMENT 8.1. Verizon, at its sole cost, reserves the right to perform a Risk Assessment of Supplier Software and Hardware. At the discretion of Verizon, the Risk Assessment may occur on an annual basis, or upon each new release of Software and/or Hardware and may include without limitation, Vulnerability assessments and Penetration Tests of: (1) the Software and/or Hardware; (2) the underlying infrastructure and operational environment in which the Software and/or Hardware is running or hosted; (3) network and facilities related to the operation or maintenance of the Software and/or Hardware; and (4) Supplier’s administrative, technical and/or physical controls related to such Software and/or Hardware. For Risk Assessments or Penetration Tests that require Supplier’s involvement, resources, facilities or systems, the parties will mutually agree as to (1) the extent of Supplier’s involvement; (2) those resources, facilities or systems of Supplier’s that would be required; and (3) the schedule for such Risk Assessment or Penetration Tests. 8.2. Verizon’s asserted right to conduct its own Risk Assessment shall in no way replace or substitute for Supplier’s own Risk Assessment Process or the requirements contained within this Exhibit. At the discretion of Verizon, 84 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential ****CERTAIN INFORMATION HAS BEEN OMITTED AND FILED SEPARATELY WITH THE COMMISSION. CONFIDENTIAL TREATMENT HAS BEEN REQUESTED WITH RESPECT TO THE OMITTED PORTIONS

a third party security vendor may be used to conduct such Verizon Risk Assessment. 85 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential
9. VULNERABILITY MANAGEMENT Supplier shall implement and maintain a comprehensive and Industry-standard Vulnerability Management Program. Supplier shall maintain dedicated employee(s) to monitor pertinent channels of public vulnerability disclosure (e.g. the NIST National Vulnerability Database) which affect Supplier Software or Hardware. This Program shall include, but is not limited to (1) the underlying platform (e.g., operating system, database product, web server and etc.); (2) all third-party and (3) open- source software included as part of Supplier Software and Hardware. This Program shall include, but is not limited to: 9.1. Supplier shall provide dedicated employee(s) to liaison with the Verizon Vulnerability Management personnel. 9.2. Supplier shall resolve identified Vulnerabilities in Supplier Hardware and Software at Supplier expense. 9.3. For Supplier Software or Hardware within the Verizon network and managed by Verizon, Supplier shall deliver to Verizon a regression tested patch within **** from the date the Vulnerability was initially disclosed or the date Supplier was notified by Verizon. 9.4. For Supplier Software or Hardware hosted within the Verizon network and managed by Supplier, Supplier shall implement in production a regression tested patch within **** from the date the Vulnerability was initially disclosed or the date Supplier was notified by Verizon. 9.5. For Supplier Software or Hardware hosted externally to the Verizon Network, Supplier Shall implement in production a regression tested patch within **** from the date the Vulnerability was initially disclosed or the date Supplier was notified by Verizon. 86 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential ****CERTAIN INFORMATION HAS BEEN OMITTED AND FILED SEPARATELY WITH THE COMMISSION. CONFIDENTIAL TREATMENT HAS BEEN REQUESTED WITH RESPECT TO THE OMITTED PORTIONS

EXHIBIT C-3 CLOUD SECURITY REQUIREMENTS Production / Non-Production Segregation of Cloud Duties: Production and non- production cloud environments shall be kept separate to prevent unauthorized access or changes to information assets, particularly in the case of Cloud and virtualization administrators with privileged access. Wireless Security. Policies and procedures shall be established and mechanisms implemented to protect access to cloud architectures from unauthorized wireless access, including the following: 1) Firewalls implemented and configured to restrict unauthorized traffic 2) Essential security settings enabled with strong encryption for authentication and transmission, replacing vendor default settings (e.g., encryption keys, passwords, SNMP community strings, etc.). 3) Logical and physical user access to wireless access points restricted to authorized personnel 4) The capability to detect the presence of unauthorized (rogue) wireless network devices for a timely disconnect from the network Shared Networks and/or Applications. Access to systems with shared infrastructure shall be restricted to authorized personnel in accordance with security policies, procedures and standards. Networks and/or applications shared with external entities shall have a documented plan detailing the compensating controls used to separate network traffic and application access between organizations. Clock Synchronization. A standard NTP time source must be used to synchronize the system clocks of all cloud-based information processing systems within the organization or explicitly defined security domain to facilitate tracing and reconstitution of activity timelines. Mobile Code. Mobile code (i.e. code shared between cloud and client devices or software) shall be authorized before its installation and use, and the configuration shall ensure that the authorized mobile code operates according to a clearly defined security policy. All unauthorized mobile code shall be prevented from executing. GDSVF&H\3541367.2 87 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential
EXHIBIT D - DISASTER RECOVERY PLAN GDSVF&H\3541367.2 88 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential
EXHIBIT E – COMPLIANCE WITH MINORITY, WOMAN-OWNED, AND SERVICE- DISABLED VETERAN BUSINESS ENTERPRISES (MWDVBE) UTILIZATION Primary Supplier Commitment A. Supplier Commitment. 1. The Supplier (hereinafter “Primary Supplier”) agrees to provide opportunities for suppliers identified and Certified as a Minority, Woman, and Service-Disabled Veteran - owned and controlled Business Enterprises (hereinafter “MWDVBE”), in accordance, at a minimum, with the terms and conditions of this Exhibit. 2. In addition, if the scope of this Agreement includes the provision of products or performance of services for or in conjunction with a Verizon Federal government agreement, the then-current Federal Acquisition Regulations (FAR) requirements regarding MWDVBE subcontracting and reporting shall also apply. 3. In the event that a change in ownership results in a change of Supplier or subcontractor’s status as a Certified MWDVBE, Supplier shall notify Verizon in writing within **** of such change. B. Definitions. 1. Certified - Currently certified as MWDVBE by an authorized certifying body, such as the National Minority Supplier Development Council (NMSDC) or its affiliate regional councils, the Women’s Business Enterprise National Council (WBENC) or its affiliate regional councils, the California Public Utility Commission (CPUC) Clearinghouse, or other similar local, state, or federal certifying body. 2. Control - Having overall fiscal/legal responsibility and exercising the power to make policy decisions. 3. Owned - At least fifty-one percent (51%) of the business or, in the case of a publicly owned business, at least fifty-one percent (51%) of the stock is owned by a minority, woman or service-disabled veteran. Transfer of ownership to or purchase of an existing business by a minority, woman, or service-disabled veteran by a non-minority who remains actively involved in the operation of the business does not qualify as a MWDVBE. 4. Minority–owned Business Enterprise (MBE) - A business concern in which at least fifty-one percent (51%) of the ownership and control is held by individuals who are members of a minority group and of which at least fifty-one percent (51%) of the net profits accrue to members of a minority group. Such persons include, but are not limited to, Black Americans, Hispanic Americans, Asian Pacific Americans (persons with origins from Japan, China, the Philippines, Vietnam, Korea, Samoa, Guam, the former U.S. Trust Territory of the Pacific Islands (Republic of Palau, the Commonwealth of the Northern Mariana Islands, Republic of the ▇▇▇▇▇▇▇▇ Islands, Federated States of Micronesia) Laos, Cambodia (Kampuchea), Taiwan, Burma, Thailand, Malaysia, Indonesia, Singapore, Brunei, Macao, Hong Kong, Fiji, Tonga, Kiribati, Tuvalu, or Nauru); Subcontinent Asian Americans (persons with origins from India, Pakistan, ▇▇▇▇▇▇▇▇▇▇, ▇▇
▇▇▇ ▇▇▇▇▇, Bhutan, the Maldives Islands or Nepal); Native Americans (American Indians, Eskimos, Aleuts, and Native Hawaiians); and members of other groups designated by the U. S. Small Business Administration as minorities. 5. Women-owned Business Enterprise (WBE) - A business concern which is at least fifty-one percent (51%) owned and controlled by a woman or women; or, in the case of any publicly owned business, at least fifty-one percent (51%) of the stock is owned by a woman or by women. Such women's business enterprise shall further be classified as either minority or non-minority women-owned business, depending upon the greater portion of ownership. 6. Vietnam Era Veteran-owned Business Enterprise (VBE) - A business concern that is at least fifty-one percent (51%) owned and controlled, or in the case of a publicly owned business, at least fifty-one percent (51%) of the stock is owned, by an owner or owners who are veterans of the U.S. military, ground, navel, or air service, any part of whose service was during the period August 5, 1964 through May 7, 1975, who (1) served on active duty for a period of more than one hundred and eighty (180) days and were discharged or released with other than a dishonorable discharge, or (2) were discharged or released from active duty because of a service-connected disability. “Vietnam-Era Veteran” also includes any veteran of the U.S. military, ground, navel, or air service who served in the Republic of Vietnam between February 28, 1961 and May 7, 1975. 7. Service-disabled Veteran-owned Business Enterprise (SDVBE) - (1) A business concern that is (a) at least fifty-one percent (51%) owned by one or more service-disabled veterans or, in the case of any publicly owned business, at least fifty-one percent (51%) of the stock of which is owned by one or more service-disabled veterans or, in the case of a veteran with a permanent and severe disability, the spouse or permanent caregiver of such veteran. (2) “Service-disabled veteran” means a veteran, as defined in 38 U.S.C. 101(2), with a disability that is service- connected as defined in 38 U.S.C. 101(16). 8. Persons with Disabilities-owned Business Enterprise (DBE) - a business concern that is at least fifty-one percent (51%) owned and controlled, or in the case of a publicly owned business, at least fifty-one percent (51%) of the stock of which is owned by an owner or owners who are disabled as defined by the Americans With Disabilities Act (ADA). This classification can also include agencies that employ fifty-one percent (51%) or more disabled persons. C. Supplier Diversity Utilization Plan. 1. The Primary Supplier shall submit a Supplier Diversity Utilization Plan (“Plan”) for approval by Verizon prior to the execution of this Agreement. The Plan must include a statement that the Primary Supplier will (i) achieve the MWDVBE Percent Commitment as defined in Section E, below, entitled “Primary Supplier MWDVBE Percent Commitment,” and (ii) report results utilizing the reporting method described below in Section D, entitled “Reporting.” 90 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential

2. The list of MWDVBE suppliers to be used by the Primary Supplier in its (Contract-Specific) Plan form shall constitute the following: (a) A representation by the Primary Supplier to Verizon in regard to the MWDVBE supplier(s) that (a) it intends to use the firm for the work specified in the Plan; (b) on the basis of information known to it and after reasonable inquiry, it believes such MWDVBE supplier(s) to be technically and financially qualified to perform the work specified, and that the firm is available to perform the work; and (c) the MWDVBE supplier(s) identified is currently Certified as an MWDVBE by an authorized certifying body. (b) A commitment that the Primary Supplier will enter into a contract with each such MWDVBE supplier (or approved substitutes) in accordance with its Plan. (c) A commitment by the Primary Supplier that it will not substitute a MWDVBE supplier listed in its Plan without prior written notification to Verizon. Unless the Primary Supplier has a reasonable belief that use of a designated MWDVBE supplier will potentially cause personal injury or damage to property, or that such MWDVBE Supplier has engaged in illegal or unethical behavior, no substitution(s) of MWDVBE supplier(s) designated on the Plan form may be made without notifying Verizon in writing, citing the specific reason(s) for substitution. D. Reporting. 1. The Primary Supplier shall report quarterly MWDVBE expenditures by using the “Prime Supplier MWDVBE Quarterly Report” and reporting format specified on the Verizon website at ▇▇▇▇://▇▇▇▇▇.▇▇▇▇▇▇▇.▇▇▇/▇▇▇▇▇▇▇▇▇/. For assistance with such reporting, contact Verizon Supplier Diversity at ▇▇▇@▇▇▇▇▇▇▇.▇▇▇. 2. The Prime Supplier MWDVBE Quarterly Report shall include a) MWDVBE expenditures specific to Verizon contracts (herein, "Direct Expenditures"); and b) Verizon's prorated share of the Primary Supplier’s non-contract specific MWDVBE expenditures (herein, "Indirect Expenditures"). Verizon's prorated share of such Indirect Expenditures for the applicable calendar quarter shall be equal to the percentage derived from the following formula: Sales to Verizon / Sales to all customers. 3. Such reports shall be submitted by no later than thirty (30) days following the end of each calendar quarter. 4. This report is intended to provide a mechanism to monitor the Prime Supplier’s compliance and progress in achieving its MWDVBE commitments as set forth in this Exhibit. 5. The Primary Supplier will provide: (a) A list of the name(s) and address(s) of the Certified MWDVBE suppliers the Primary Supplier has identified to be used in support of this Agreement; 91 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential
(b) A description of the products/services or scope of work performed by MWDVBE suppliers; and (c) The percentage or volume of contract work performed by each such firm. E. Primary Supplier MWDVBE Percent Commitment. The Primary Supplier shall engage the services of Certified MWDVBE suppliers for an amount equivalent to at least seven percent (7%) of dollars spent under this Agreement during the first year of the Term. F. Primary Supplier Compliance; Standards and Remedies. 1. Compliance Standards. Verizon has the right to determine compliance by the Primary Supplier with the Plan and the MWDVBE Percent Commitments (hereinafter collectively the “MWDVBE Commitments”) established in this Exhibit. Verizon may determine that the Primary Supplier is achieving its MWDVBE Commitments by examining reports received from the Primary Supplier, performing on-site inspections, conducting progress meetings regarding work required by the Agreement, contacting involved MWDVBE suppliers, or through other Verizon actions taken in the ordinary course of administering the Agreement. 2. Updates. An annual update of the Primary Supplier’s Plan will be required to ensure compliance with this Agreement’s provision for continuous year-over-year improvement. 3. Commitments Not Achieved. In the event that the Primary Supplier’s MWDVBE Commitments hereunder are not achieved and the Primary Supplier cannot demonstrate to the reasonable satisfaction of Verizon that commercially reasonable efforts were made to accomplish such MWDVBE Commitments, such failure shall constitute default by the Primary Supplier, and Verizon reserves the right and shall have the option to invoke the termination provisions of this Agreement. Such documentary evidence of commercially reasonable efforts shall include but are not limited to a) advertisement in general circulation media, trade publications and small business media soliciting the performance of services of Certified MWDVBE suppliers related to the field of business regarding the products and/or services which are the subject matter of this Agreement; b) written notification to Certified MWDVBE suppliers requesting proposals specific to the products provided for and/or services performed under this Agreement; and c) written acknowledgment that the Certified MWDVBE suppliers’ interest in providing such products and/or performing such services is under consideration. The foregoing rights are in addition to, and not in limitation of, any other remedy Verizon may have at law or in equity. Verizon may also require that, upon request, the Primary Supplier submit additional documentation and information concerning the Primary Supplier’s performance in achieving its MWDVBE Commitments and compliance with its Plan. 4. Cure Period for Commitments Not Achieved. Should the Primary Supplier continue to fail in achieving the MWDVBE Commitments of this Agreement, including as amended, after having been given notice of such failure to meet its MWDVBE Commitments, and failing to cure such 92 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential
MWDVBE Commitments within thirty (30) days of receiving such notice by achieving its requirements, the Primary Supplier shall be in default and no further cure shall be permitted. 5. Supplier Report Card. In addition, the Primary Supplier’s ability to achieve its MWDVBE Commitments shall reflect upon and shall contribute to the Primary Supplier’s overall grade on the Supplier Report Card or other performance measurement(s). 93 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential

EXHIBIT F- NONDISCLOSURE AGREEMENT 1. To facilitate discussions, meetings and the conduct of business between the parties with respect to this Agreement, it may be necessary for one party to disclose confidential information to the other. All information of any type or character that is either disclosed to the other party or with which the other party comes into contact shall be considered as the confidential information of the disclosing party including without limitation technical, customer, personnel and/or business information in written, graphic, oral or other tangible or intangible form (“Confidential Information”). Such Confidential Information may include proprietary material as well as material subject to and protected by laws regarding secrecy of communications or trade secrets. 2. Each party acknowledges and agrees as follows: a. All Confidential Information acquired by either party from the other shall be and shall remain the exclusive property of the source; b. To inform the receiving party, in advance of any disclosure of Confidential Information, in non-confidential and non-proprietary terms, of the nature of the proposed disclosure, and to afford the receiving party the option of declining to receive the Confidential Information; c. Information which is disclosed orally shall not be considered Confidential Information unless it is reduced to writing or to a written summary which identifies the specific information to be considered as Confidential Information, and such writing is provided to the receiving party at the time of disclosure or within thirty (30) days; d. To receive in confidence any Confidential Information; to use such Confidential Information only for purposes of work, services or analysis related to the matter of mutual interest described above and for other purposes only upon such terms as may be agreed upon between the parties in writing; e. To limit access to such Confidential Information to a party’s employees, contractors, and agents who (i) have a need to know the Confidential Information in order for such party to participate in the matter of mutual interest described above; and (ii) have also entered into a written agreement with the receiving party which provides the same or greater protections to any Confidential Information provided hereunder. Upon request, Supplier shall provide a copy of such agreements to Verizon; and f. At the disclosing party's request, to return promptly to the disclosing party or to destroy any copies of such Confidential Information that is in written, graphic or other tangible form, and provide to the disclosing party a list of all such material destroyed. 94 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential

3. These obligations do not apply to Confidential Information which, as shown by reasonably documented proof: a. Was in the other's possession prior to receipt from the disclosing party; or b. Was received by one party in good faith from a third party not subject to a confidential obligation to the other party; or c. Now is or later becomes publicly known through no breach of confidential obligation by the receiving party; or d. Is disclosed to a third party by the source without a similar nondisclosure restriction; or e. Was developed by the receiving party without the developing person(s) having access to any of the Confidential Information received from the other party; or f. Is authorized in writing by the disclosing party to be released or is designated in writing by that party as no longer being confidential or proprietary. 4. Supplier agrees that either party may disclose Confidential Information to an Affiliate, subject to the terms and conditions set forth herein. For purposes of this Agreement, an Affiliate shall be defined as an entity that controls, is controlled by, or is under common control with such party. 5. Other than as required by law or as set forth in 2(e) or under the Agreement, neither party shall, without the other party’s prior written consent, disclose to any person, or make a public announcement of, the existence of discussions or negotiations or any of the terms relating to the matter of mutual interest described above or any Confidential Information. 6. If a party (“Ordered Party”) receives a request to disclose any Confidential Information of the other party, whether pursuant to a valid subpoena or an order issued by a court or regulatory body (“Ordering Party”), and on advice of legal counsel that disclosure is required by law, then prior to disclosure, the Ordered Party shall (i) notify the other party of the terms of such request and advice, (ii) cooperate with the other party in taking lawful steps to resist, narrow, or eliminate the need for such disclosure, and (iii) if disclosure is nonetheless required, work with the other party to take into account the other party’s reasonable requirements as to its timing, content and manner of making or delivery and use best efforts to obtain a protective order or other binding assurance from the Ordering Party that confidential treatment shall be afforded to such portion of the Confidential Information as is required to be disclosed. The foregoing is without limitation of the other party’s ability to seek a protective order or other relief limiting such disclosure; in such a case, the Ordered Party shall cooperate in such efforts by the other party. 95 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential

7. Supplier acknowledges that the proprietary data, know-how, software or other materials or information obtained from a party under this Agreement may be commodities and/or technical data that may be subject to the Export Administration Regulations (the “EAR”) of the United States Department of Commerce as well as trade and economic sanctions subject to the Trading With the Enemy Act (TWEA) and the International Emergency Economic Powers Act (IEEPA) of the Office of Foreign Asset Control within the Department of Commerce, and that any export or re-export thereof must be in compliance with the EAR, TWEA and IEEPA. Each party agrees that it shall not export or re- export, directly or indirectly, either during the term of this Agreement or after its expiration, any commodities and/or technical data (or direct products thereof) provided under this Agreement in any form to destinations in or nationals of Country Groups D:1 or E, as specified in Supplement No. 1 to Part 740 of the EAR, and as modified from time to time by the U.S. Department of Commerce, or to destinations that are otherwise controlled or embargoed under U.S. law in contravention of the EAR or any of the above statutes. 8. It is agreed that a violation of any of the provisions of this Agreement will cause irreparable harm and injury to the non-violating party and that party shall be entitled, in addition to any other rights and remedies it may have at law or in equity, to seek an injunction enjoining and restraining the violating party from doing or continuing to do any such act and any other violations or threatened violations of this Agreement. Absent a showing of willful violation of this Agreement, neither party shall be liable to the other, whether in contract or in tort or otherwise, for special, indirect, incidental or consequential damages including lost income or profits of any kind, even if such party has been advised of the possibility thereof. In no event shall either party be liable to the other for punitive or exemplary damages. 96 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential

EXHIBIT G SUMMARY OF VERIZON’S GUIDELINES FOR EVALUATING CRIMINAL RECORD REPORTS 1. Information regarding criminal offenses that is provided by or received about candidates who are under consideration for assignment to provide services to Verizon (the “Candidate”) will not necessarily bar their assignment with Verizon. Each Candidate must be considered on a case-by-case basis. 2. If a Candidate has a criminal record, Supplier must determine whether the disclosed criminal conviction will impair the Candidate’s ability to successfully perform the services that he/she may be assigned. Thus, a conviction may only be used to disqualify a Candidate from assignment if the criminal conviction is related to the nature of the services that he/she may be assigned to perform for Verizon. When determining whether a Candidate should be disqualified from assignment to Verizon due to a criminal record, Supplier must consider the below Mitigating Factors. Although this is not an exhaustive list of factors, these factors must be evaluated along with any other associated extenuating circumstances. 3. These additional guidelines should be used in combination with the Mitigating Factors listed in Section 4 below: • Look at each case individually. • Consider each factor and decision point carefully. • Consider state law requirements - for example, certain states may not allow consideration of misdemeanor convictions. • If additional information is needed, actual court records may be pulled and reviewed prior to making a decision to hire. Additionally, consult Supplier’s background check supplier or counsel if a Candidate has: • Expunged or Sealed Records (Note: certain states do not permit inquiries into expunged or sealed records) • Parolee Status • Pending Charges/Arrests (Note: certain states do not permit inquiries into arrests that have not resulted in a conviction) • Juvenile Records 97 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential

4. Mitigating Factors Factors to be Decision Points Considered For all criminal convictions, the nature of the job applied for must be considered. This factor considers the nature and gravity of the offense as it relates to the nature of the position sought. Is the nature of the conviction such that there is a concern for the safety of Verizon employees/customers, protection of company assets, or the confidentiality/sanctity of Verizon records including confidential consumer information? • For jobs involving direct personal contact with Job Relatedness - Nature customers, other employees, or the public, careful of job and crime consideration should be given to whether a Candidate convicted of a crime involving violence presents a significant risk to Verizon, its employees or its customers. • Criminal convictions involving integrity, fraud or theft of property could weigh against Candidates applying for positions with financial responsibility (e.g., cash, etc.) and responsibility for handling proprietary and confidential information (e.g., customer &/or employee information). Was the Candidate a teenager or close to one when s/he committed the crime? If the Candidate was a minor at the Age at time of crime time of the criminal offense, this could weigh in the Candidate’s favor Efforts at rehabilitation and If sentencing required probation, community service or successful completion of other, has the Candidate completed the service? sentencing Time elapsed since If significant time has elapsed since the crime was conviction or final committed, this could weigh in the Candidate’s favor. adjudication If the crime was committed under extenuating Candidate’s explanation of circumstances, which would not be present in the reason crime was workplace, this could weigh in the Candidate’s favor. committed Court records should be pulled and reviewed to validate Candidate’s explanation. 98 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential

Successful employment Has the individual held steady employment since the following criminal conviction? Satisfactory employment history since the conviction crime was committed could weigh in the Candidate’s favor. Has the Candidate had additional convictions? Number of criminal If the Candidate is a repeat offender, this could weigh convictions against the Candidate. 99 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential

100 Application Service Provider Agreement - Synchronoss and Verizon Proprietary and Confidential

